No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.
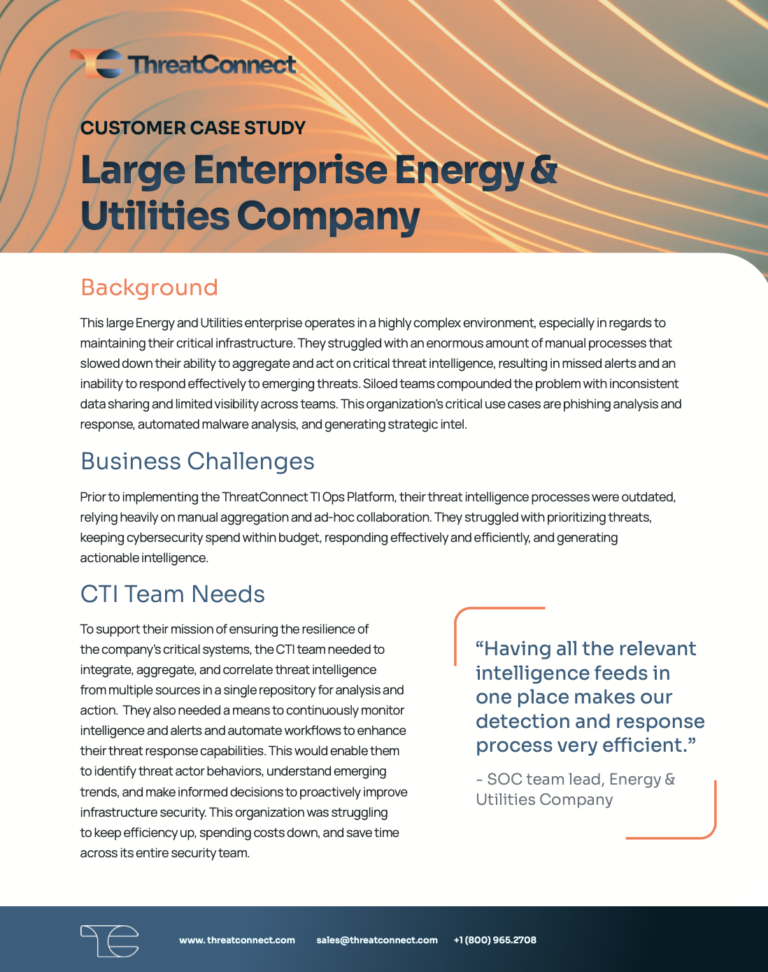
Energy and Utilities Organization Achieves Higher Efficiency and Better Cyber Defense With One Platform
This large Energy and Utilities organization was struggling with outdated threat intelligence processes – relying heavily on manual aggregation and ad-hoc collaboration. They struggled with prioritizing threats, keeping cybersecurity spend within budget, responding effectively and efficiently, and generating actionable intelligence. Implementing The ThreatConnect TI Ops Platform revolutionized how this organization leveraged threat intelligence to improve […]
ThreatConnect ATT&CK Visualizer
Evolve Your Defense with ATT&CK Visualizer ThreatConnect’s ATT&CK Visualizer enables analysts to see attacker tactics and techniques and identify adversarial behaviors. By leveraging the power of the MITRE ATT&CK Framework, ThreatConnect empowers analysts to quickly determine how to detect future attacks and take the necessary actions to prevent threats.
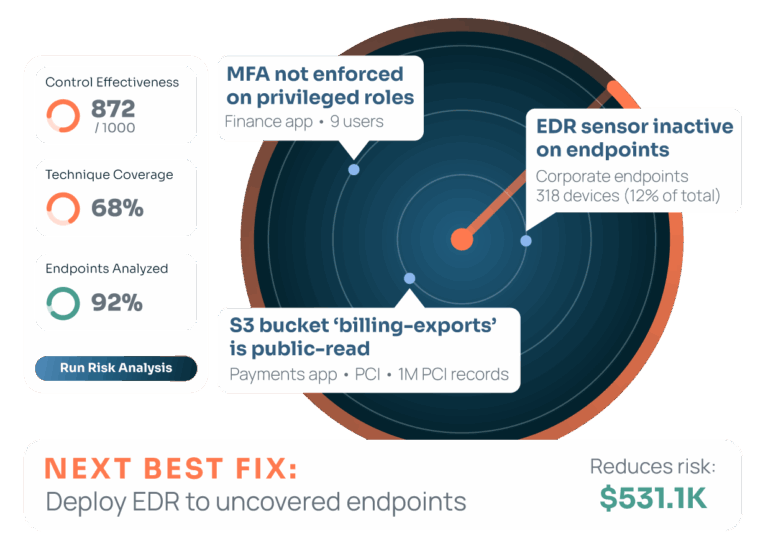
Operationalizing Risk Quantification for Smarter Security
How can organizations effectively analyze and communicate cyber risk to make the best possible investment and prioritization decisions? In this joint whitepaper from IBM and ThreatConnect, we’ll highlight the significant financial and operational benefits of adopting a cyber risk quantification approach and explore the top 5 use cases that enterprises are adopting. Use Cases We’ll […]
Smarter Security Series – Demystifying the Deep and Dark Web Intel
In the final video of this installment of the Smarter Security Series, Devin Somppi and Lara Meadows bring into focus the much-discussed, sometimes feared, realms of the deep and dark web. The duo dissects what these terms mean, not just to tech wizards but also to business leaders and key decision-makers. Devin emphasizes that the […]
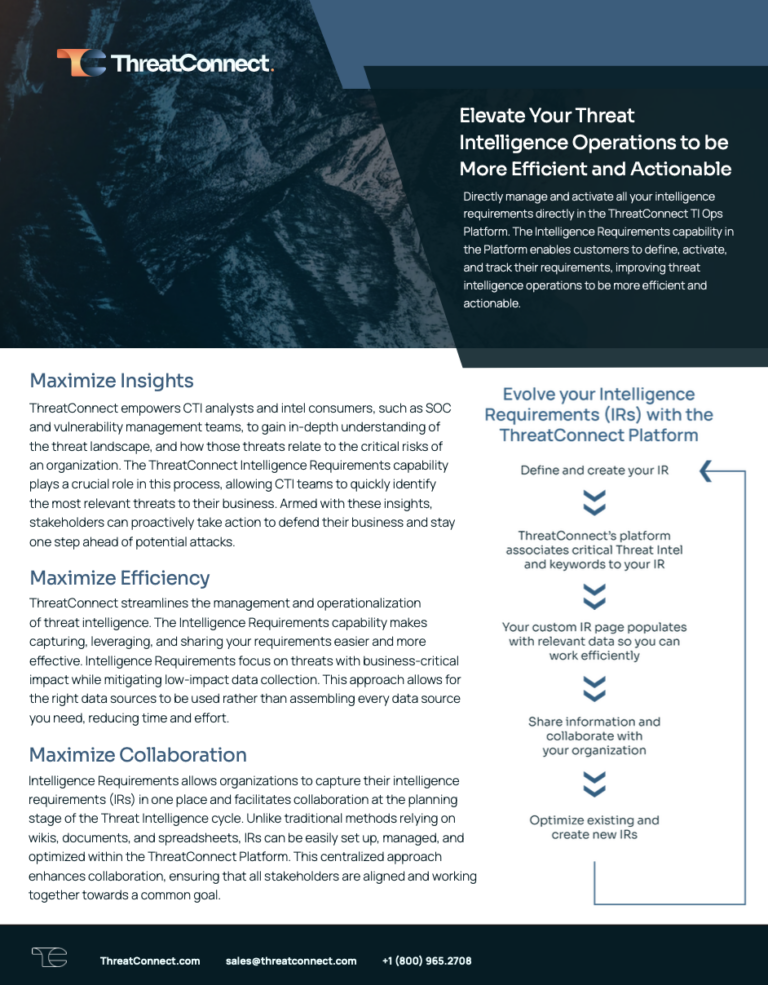
Intelligence Requirements
Elevate efficiency and actionability in threat intelligence operations with ThreatConnect’s Intelligence Requirements capability. Gain deeper insights, maximize efficiency, and collaborate seamlessly, while reducing the time it takes to gather and disseminate valuable threat intelligence. See datasheet here.
Operationalizing Intelligence Requirements: A Comprehensive Guide
Enhance your cybersecurity with intelligent requirements and craft effective intelligence strategies. Stay ahead of cyber threats by adapting to an evolving landscape. Download the comprehensive guide here.
Buyer’s Guide for Threat Intelligence Operations
The ThreatConnect Buyer’s Guide for Threat Intelligence Operations is a comprehensive resource tailored for cybersecurity leaders, strategists, architects, and analysts seeking to enhance their organization’s security and risk posture by effectively utilizing cyber threat intelligence (CTI).
Streamline Your Cyber Threat Research with ThreatConnect Intelligence Requirement Webinar
Learn more about the importance of intelligence requirements and the impact they have on your threat intel org.
Power of Polarity + Google
Learn how Polarity’s platform integrates with Google services to enhance cybersecurity. Discover integration use cases, essential tools like VirusTotal and Chronicle, and streamline your workflow with expert insights.
ThreatConnect and SecurityScorecard
ThreatConnect has partnered with SecurityScorecard for their Cyber Risk Quantification (CRQ) solution powered by ThreatConnect Risk Quantifier (RQ). Applying ThreatConnect’s statistical and machine learning algorithms to the Security Scorecard data enables customers to easily understand their risk, both external and internal, and more importantly prioritize which factors should be improved based on financial risk reductions. SecurityScorecard’s […]

Smarter Security Series – The Putty That Fits Into All Your Security Tools
Lara Meadows, VP of Sales Engineering at ThreatConnect, brought to light some significant issues that revolve around key integrations when dealing with clients and building their systems. In her discussion with Devin Somppi, VP of Cybersecurity at Decisive Group, they unravel numerous intriguing elements. Devin paints a picture of the infinite possibilities offered through integrations […]

Smarter Security Series – What is Threat Hunting?
What is Threat Hunting? In this video of the Decisive Group interview, Lara Meadows, VP of Sales Engineering at ThreatConnect, discussed the current trends in threat hunting with Devin Somppi, VP of Cybersecurity at Decisive Group. They share insights on: What is Threat Hunting, and how to enhance its efficiency Importance of staying updated on […]