No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.

Smarter Security Series – Meet The Decisive Group
The Decisive Group, formerly known as Bright Sky, has stirred interest with its distinctive approach to solving data center issues. The Decisive Group provides an array of customized solutions, extending from physical server rack stack management to the provision of its proprietary hybrid cloud services throughout Canada. What sets The Decisive Group apart, however, is […]

Maximize your Splunk Investment with Polarity’s Splunk Integration
Optimize your Splunk deployment with our guide on the Polarity-Splunk integration. Learn to enhance data analysis using custom SPL queries and improve your cybersecurity operations.

Practical Use of AI in Cyber Security Analysis with Polarity & Ventech
Join Polarity’s webinar, where experts will delve into AI in cybersecurity, exploring integration strategies, practical applications, and risk mitigation to enhance security operations.

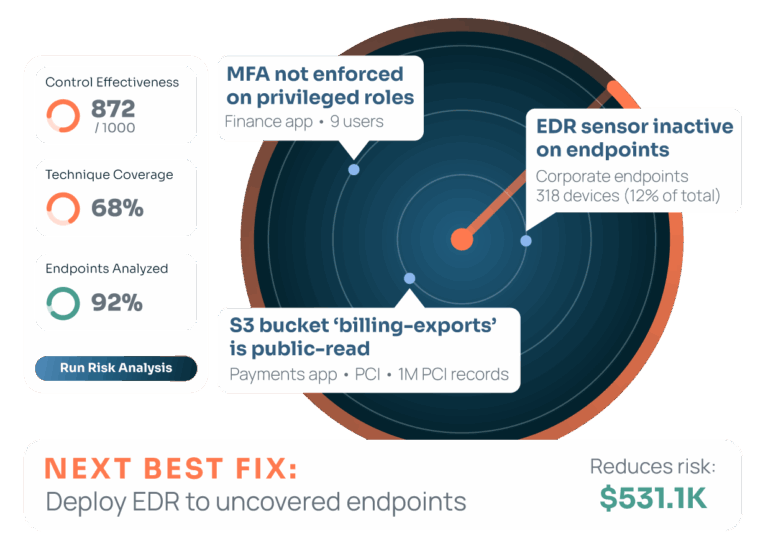
Webinar: Leveraging Big Data to Measure Cyber Risk
Everyone agrees that cyber risk is a business risk. As the number of devices grows and we see greater interconnectivity of devices, the likelihood and impact of material impacts increase. We need to apply big data solutions to help ensure companies understand their risk, can procure the right cyber insurance, and can mitigate or minimize […]

Maximizing Investments with Real-Time Tool Validation
Join our session with expert Matt to explore how optimizing security investments through automation and federated search can enhance efficiency and alleviate team stress.

Smarter Security Series with PWC Cyber Risk Expert
Welcome to ThreatConnect’s Smarter Security Expert Series! We’re interviewing the brightest minds in the cyber industry and getting their expertise on current trends and tips and tricks for a successful modern security team. We’re joined by Yousef Ghazi-Tabataba – Director, Risk at PwC! Yousef sat down with our VP of Cyber Risk Products, Jerry Caponera, […]

Enabling Leaders with Polarity Source Analytics
Security teams today face increasing challenges such as managing large volumes of data, navigating fragmented tools, and responding to evolving cyber threats. Traditional methods of context enrichment often result in incomplete data, inefficiencies, and slower response times. Polarity Source Analytics (PSA) is the innovative solution designed to tackle these challenges by delivering real-time insights, seamless […]

Banking and Finance Organization Matures Threat Intelligence Operations with One Platform
This security team had limited resources and lacked scalability despite having a mature threat intelligence program. Without a defined strategy and approach, they were overwhelmed with the amount of data they needed to analyze, aggregate and produce intelligence for. By implementing The ThreatConnect Platform, they were able to quickly and effectively improve visibility across security […]

Practical Cyber Risk Quantification Usage & Real Life Scenarios Webinar
In this discussion, our general manager of risk products Jerry Caponera and Shreeji Doshi, AMD in Kroll’s Cyber Risk business, dove into the real-life applications of cyber risk quantification, common pitfalls for adoption, and more importantly where the biggest wins lie – especially when it comes to having the discussion around prioritization as it can make communications […]

Fireside Chat Live Panel
An executive view of how cyber risk has changed cyber security – for better and worse Security is not a technical problem – it’s a business one. How can you turn the conversation from technology to business? Have you been looking into how companies are managing and reporting on cyber risk? Or wondering where cyber […]

ThreatConnect Risk Quantification Report: Healthcare, Manufacturing & Utilities
A recent IBM report puts the average cost of an attack at $4.35m. However, that average attack figure takes into account a large number of incidents that cost relatively little (less than $25k) and a few that cost a lot. The question is – does the average apply to you? To answer this question, you […]

Large Enterprise Software Company Leverages One Platform to Improve Efficiency
This security team was overwhelmed by the noise from its security tools and intelligence feeds. Without automation, they were spending a significant amount of time on manual processes. By implementing The ThreatConnect Platform, they were able to improve collaboration between its CTI team and other security teams and the effectiveness of its security tools with […]