No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.
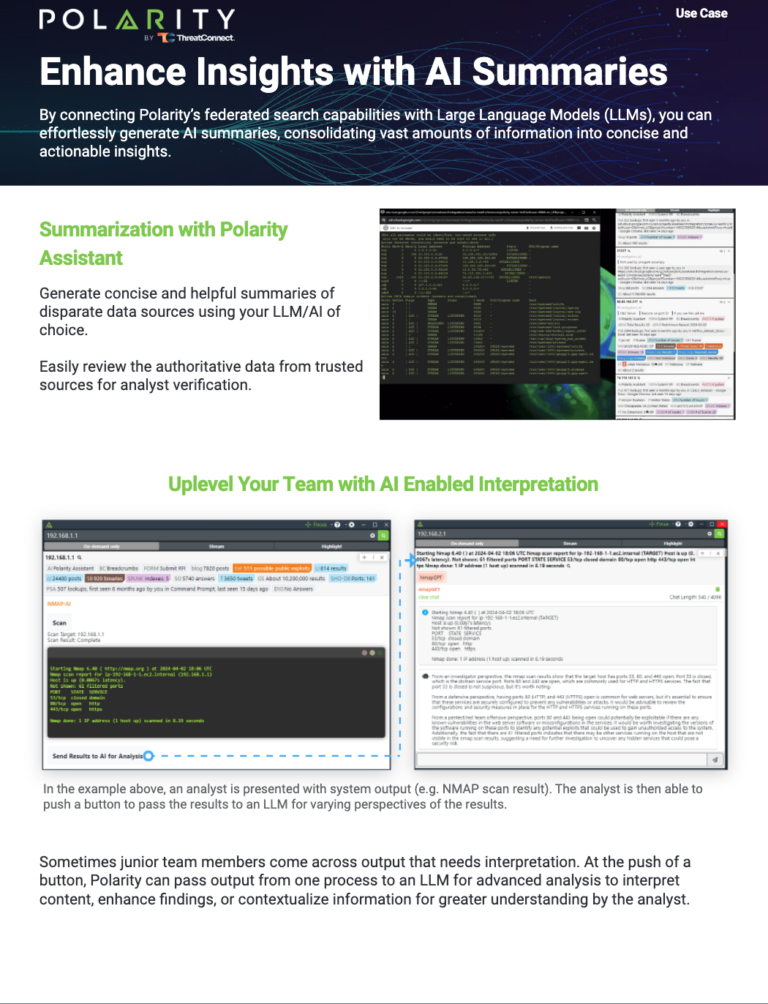
Enhance Insights with AI Summaries
Revolutionize cybersecurity with ThreatConnect and Polarity’s AI integration. Gain actionable insights, streamline analysis, and enhance defenses with AI-driven tools.
SANS CTI Survey 2024: Managing the Evolving Threat Landscape
Unlock Insights into the State of Cyber Threat Intelligence (CTI) It’s not surprising that cyber threats remain top of mind for organizations of all types. The global geopolitical situation is growing increasingly unstable, resulting in more conflicts and hybrid threats. Staying ahead of adversaries and knowing the latest trends is crucial for CTI professionals to […]
Choosing the Right Cyber Risk Quantification Solution Webinar
Watch this on-demand webinar of the popular use cases for CRQ programs and the benefits and challenges of CRQ approaches and solutions.
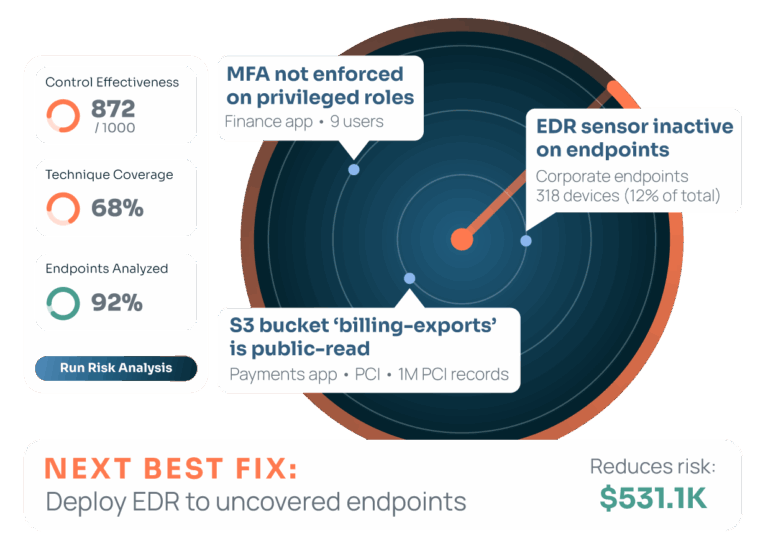
ThreatConnect’s Guide to Cyber Risk Quantification
Develop a strategic approach to cyber risk management with our definitive Guide To Cyber Risk Quantification. Uncover how to effectively assess, communicate, and mitigate the complexities of cyber risks in today’s evolving digital landscape. Why Cyber Risk Quantification Is Essential Organizations must enhance their cyber risk management strategies in the face of rising cyber attacks […]

Optiv & Clearshark – Polarity on the Go!
Discover how Polarity and FlyAway kits enhance secure network operations. Learn from experts Matt Toth, Dan Clarke, and Stan Vignier how these tools revolutionize data recall and incident response. Watch the webinar for insights on transforming your cybersecurity processes.

ThreatConnect Risk Quantifier App for ServiceNow Risk Management Product
ThreatConnect announced the official launch of the ThreatConnect RQ App for ServiceNow, now available in the ServiceNow Store. Click here to show transcript Hello, and welcome. In this video, I will illustrate the value of the new ThreatConnect RQ app within the ServiceNow GRC and how easy it is to get immediate value from the […]
Buyer’s Guide for Cyber Risk Quantification Solutions
This guide equips CRQ solution buyers with the knowledge to assess and determine the appropriate solution across a variety of use cases when implementing or evolving a CRQ program.

Smarter Security – Security Expert Reveals Top Concerns in an Evolving Digital Landscape
In the latest episode, Lara Meadows engages with Incident Response expert Matt Scheurer to delve into the intricacies of cybersecurity threats in a rapidly evolving digital landscape. Matt shares his deepest cybersecurity concerns, focusing on the fear of the unknown that plagues today’s security professionals. He highlights the uncertainty in dealing with mergers and acquisitions, […]

Smarter Security – The Convergence of Physical and Cyber Security
In the last episode of this installment of ThreatConnect’s Smarter Security Series, host Lara Meadows unpacks the increasingly intertwined world of cybersecurity and physical security with Incident Response expert Matt Scheurer. Matt emphasizes the eroding boundaries between different corporate sectors and their collective need for robust cybersecurity strategies. He showcases how physical security considerations, like […]

Smarter Security – Expert Insights on Alert Fatigue, New Technologies, and Detection Systems
Lara Meadows interviews seasoned incident response specialist Matt Scheurer on the ever-evolving challenges in cybersecurity. Matt discusses the complexities faced with alert fatigue, the integration of new technologies, and the critical importance of fine-tuning detection systems to prevent analyst burnout. He highlights the shift towards cloud-based systems and how this increases vulnerabilities, particularly concerning the […]

Smarter Security – The Evolving Landscape of Behavioral Security
In this eye-opening episode of our Smarter Security Series, Matt Scheurer delves into the evolving landscape of behavioral security, reflecting on how past trends are resurfacing with innovations in technology and strategy. He shares his unique experiences from leading a local information security group and discusses his hands-on approach and the difference in behaviors between […]
Addressing the SEC Requirements for Materiality Disclosure Webinar
Watch this webinar where we discuss why did the SEC choose to create these regulations now and what does materiality mean and how are companies dealing with them.