
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
ThreatConnect Provides a Report on Healthcare and Medical Industry Threats
Learn about the threats and how to protect your healthcare organization Summary Medical and health organizations, which include organizations operating in the pharmaceutical sector, face a variety of threats that are inherent to the services they provide and the data they safeguard. Within medical and health verticals the risks associated with compromise are often significantly […]
Best Practices for Dashboards in Cybersecurity and Threat Intelligence
Explained Using New ThreatConnect Dashboards There’s no shortage of “dashboards” available in the software world. Walking the floor at any major industry event, it’s hard to miss the hordes of vendors touting their wares by showcasing line graphs, fancy animations, and (shudder) pie charts on big screen displays designed to shock and awe attendees into […]
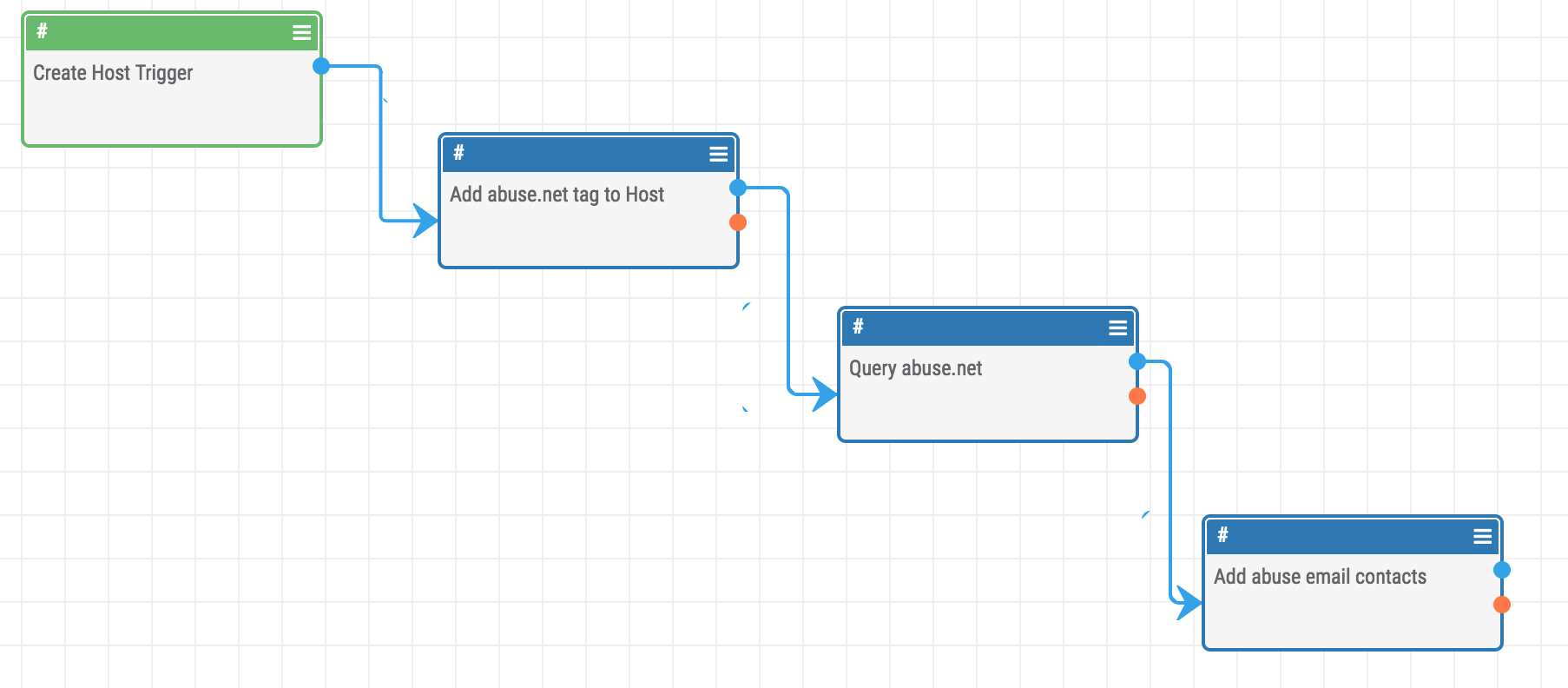
Playbook Fridays: How to Query Abuse.net with Playbooks
Query abuse.net for abuse contacts registered to a domain ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. You can also communicate with third-party services to trigger events outside of ThreatConnect. Why Was the Playbook Created? With the massive amount of […]
DNC Association Does Not Compute
Joining the cyber community to conduct independent analysis of the DNC Hack Recently, an article purported that the Democratic National Committee (DNC) turned down requests from FBI forensic units to look at its server and instead opted to use ThreatConnect and two other cyber security firms. While we cannot speak to the veracity of the […]
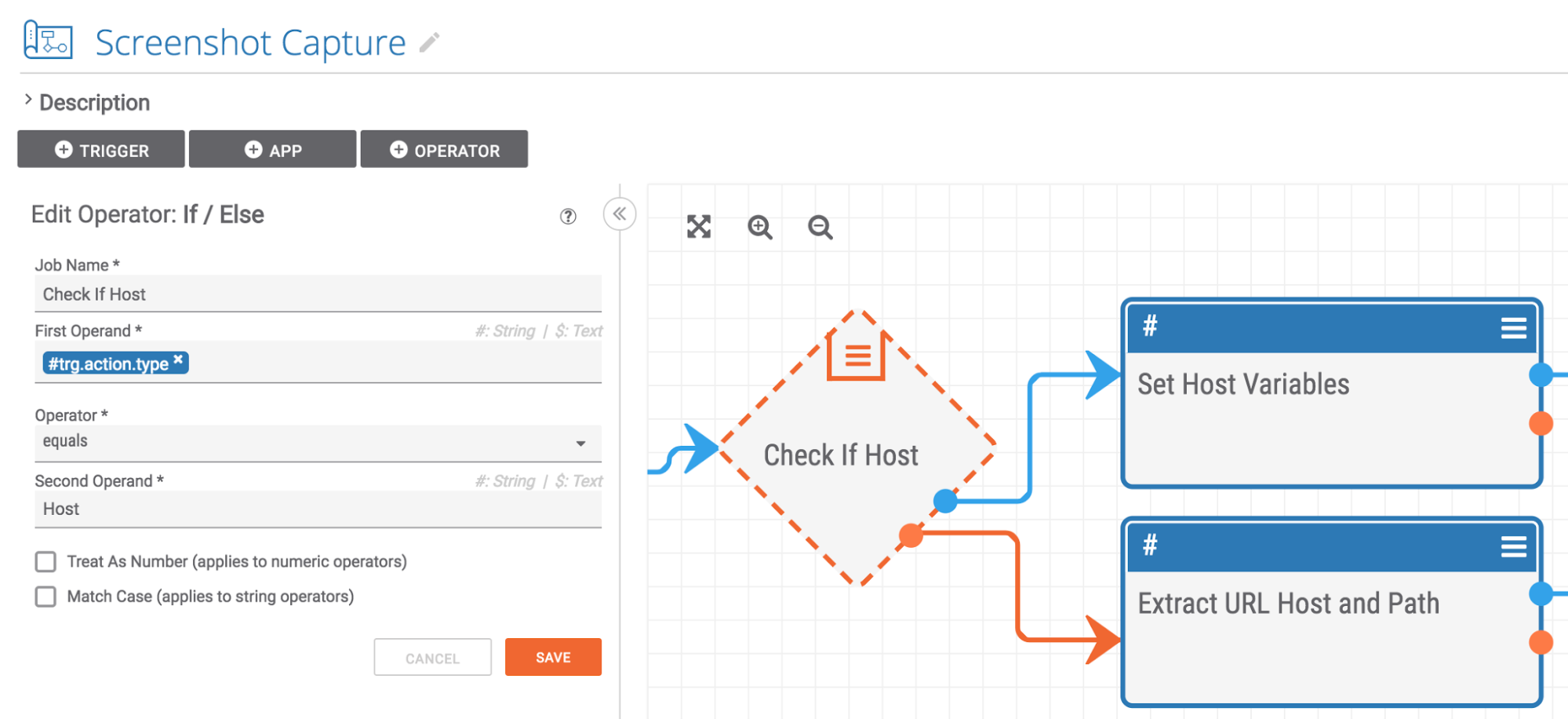
Playbook Fridays: Taking Screenshots with a Playbook
Playbook Fridays: Screenshot Capture Playbook ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. You can also communicate with third-party services to trigger events outside of ThreatConnect. Why was this Playbook created? When analyzing a phishing page, keeping a screenshot as […]
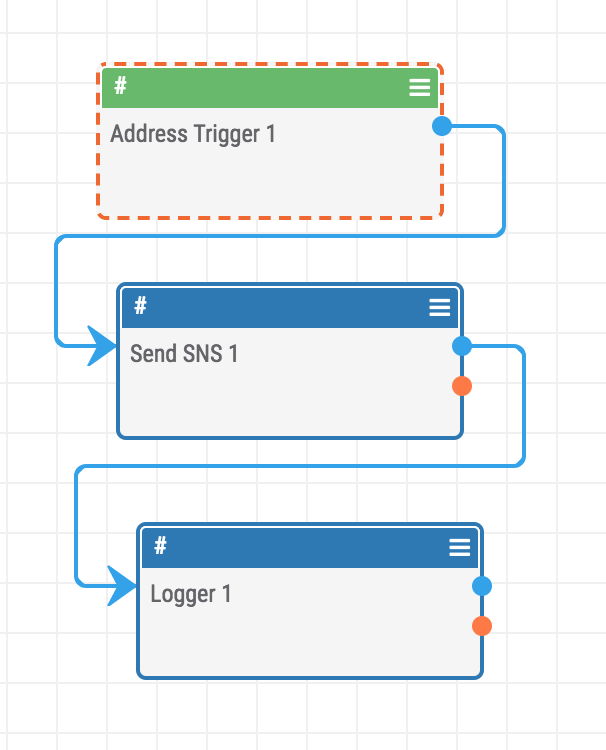
Playbook Fridays: How to Control the Cloud with Playbooks
Playbook Fridays: How To Control The Cloud With Playbooks Interacting with SNS from ThreatConnect Playbooks ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. You can also communicate with third-party services to trigger events outside of ThreatConnect. Why Was the Playbook […]

Track to the Future
How to use historical intelligence to get back to the future and defend your organization We need to talk about something. In the history of this blog, we’ve never discussed Back to the Future. It’s crazy to think that that’s the case as arguably the second-greatest sci-fi trilogy is rife with quotable lines and meme-able […]
Casting a Light on BlackEnergy
A look into BlackEnergy malware and using ThreatConnect to aggregate and memorialize the identified intelligence. As workers prepared to head home on December 23, 2015, an attack against Ukraine’s energy sector left 230,000 without electricity (or heat) for six hours. The attackers demonstrated a variety of capabilities, including spearphishing emails and variants of the BlackEnergy […]
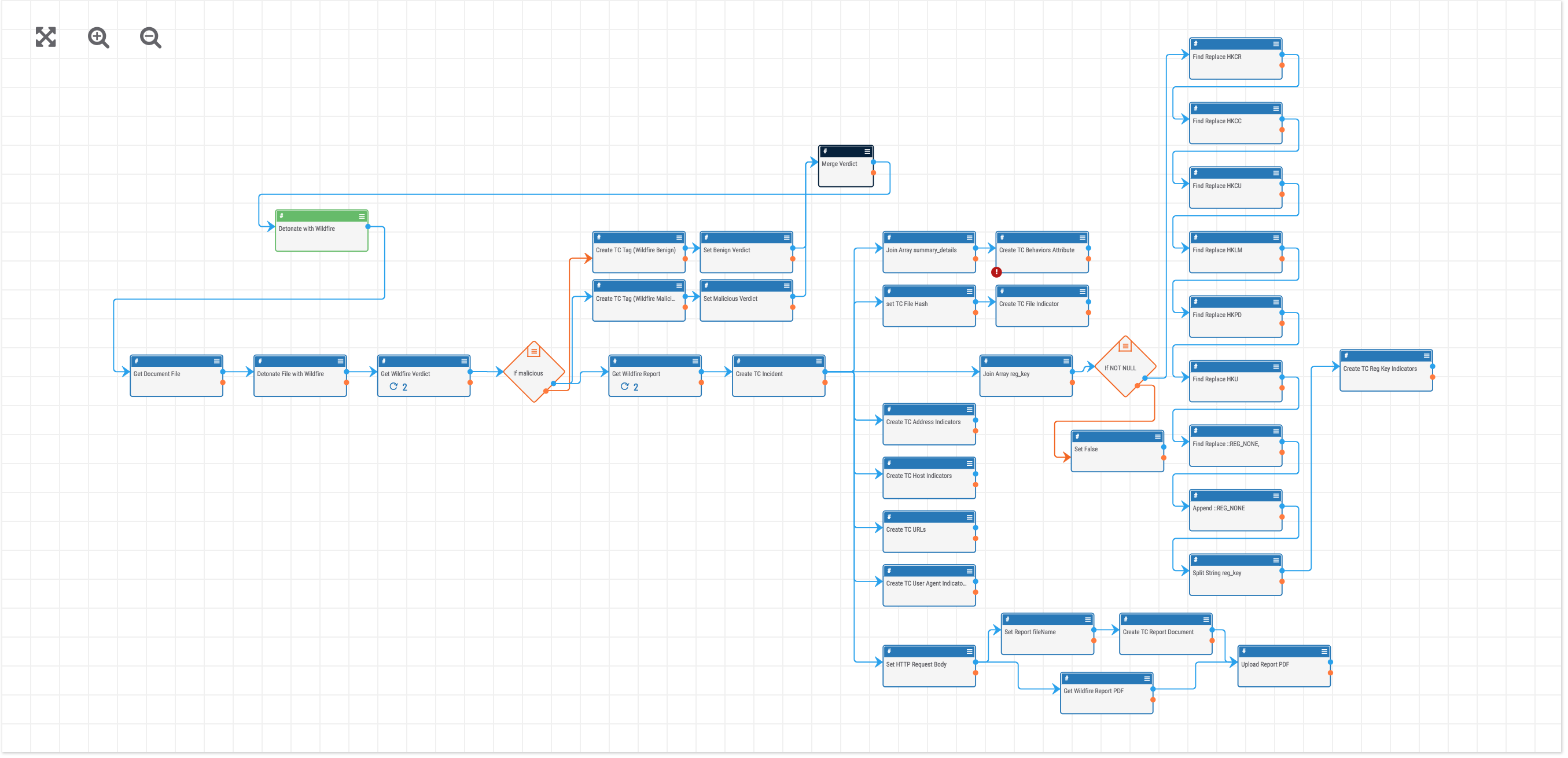
Playbook Fridays: How to Build a Playbook in ThreatConnect
This week: Palo Alto Wildfire Malware Triage Playbook ThreatConnect is beginning a NEW blog post series. We will continually publish posts featuring Playbooks that can be built in the Platform. ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in […]
ThreatConnect Training: Save Time and Act Faster with Playbooks
Automate almost any cybersecurity process – no coding needed Ingesting threat data, malware analysis, and data enrichment can all be time consuming tasks. To learn how to automate these things (along with almost any cybersecurity task) using an easy drag-and-drop interface, watch the video, Save Time and Act Faster with Playbooks. It’s presented by Dan […]
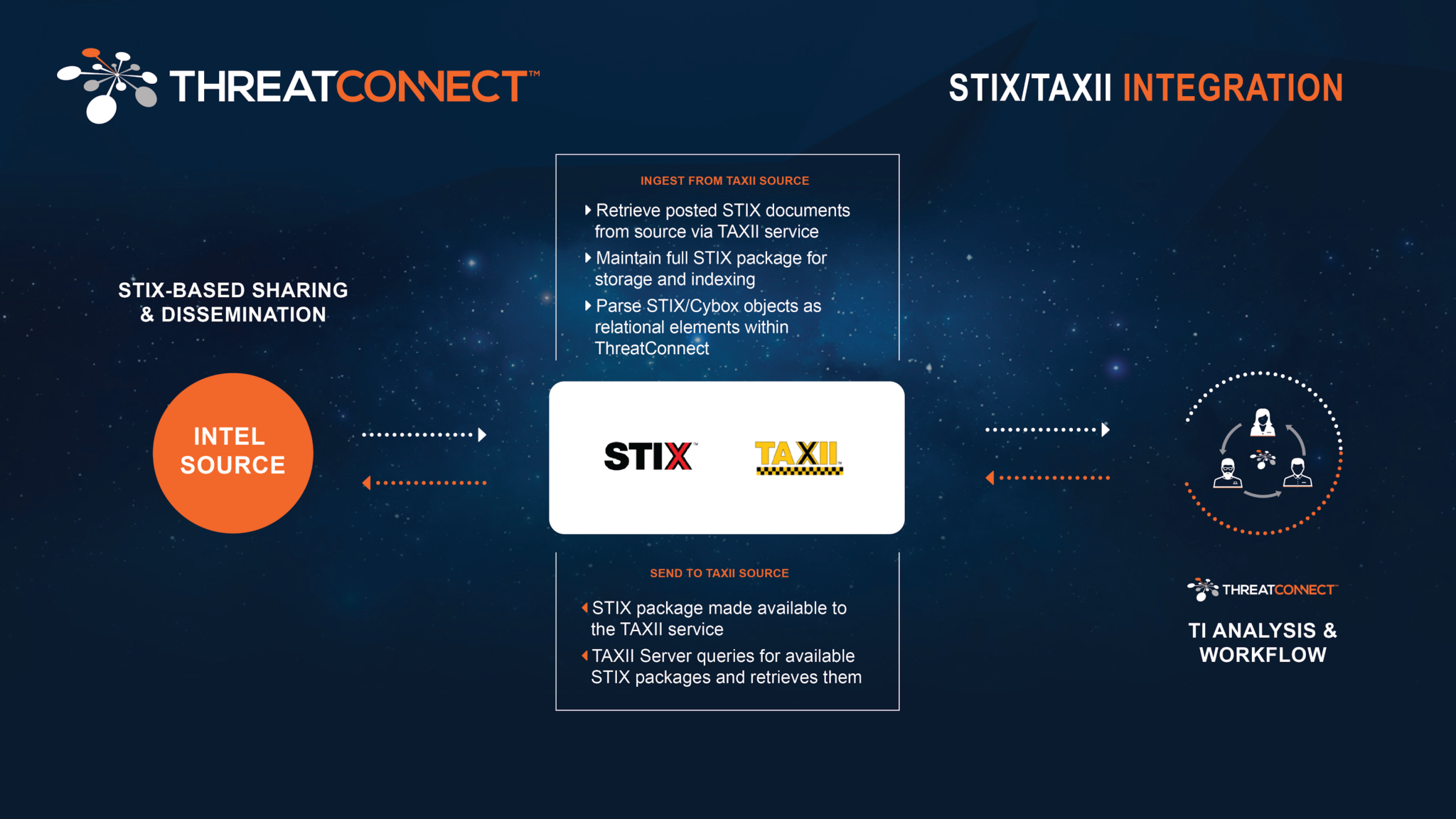
Sharing Threat Intelligence Using STIX-TAXII
STIX-TAXII | Learn how to Collect and Send STIX Threat Intelligence in ThreatConnect Sharing threat intelligence and collaborating with your peers, vendors and partners, is not optional to protect your network. ThreatConnect® supports STIX-TAXII. STIX (Structured Threat Information Expression™) and TAXII (Trusted Automated eXchange of Indicator Information™) standards in our Platform to enable effective sharing […]
ThreatConnect Introduces its Multi-Environment Orchestration Capability
Providing flexibility and scalability to unite all of your security management processes Everyone is talking orchestration these days. Including us. But not one to sit back and let our Playbooks capability languish, we took it one step further. Now, Playbooks has the ability to run across multiple environments including cloud, office networks, or virtual. The […]
