
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
How to Choose the Right SOAR Platform: A Checklist
The great thing about SOAR is that, if deployed correctly, it gives your organization the platform required to implement an intelligence-driven security strategy. You can think of SOAR and how it’s been defined and implemented (so far) as operating very much like an enabler, or a hub for decision making. It provides a centralized location […]

Introducing Polarity’s 3.2 Client Release
We’re excited to announce our 3.2 Client Release! This release includes updates to our Settings, Menu, Optimizations, Zoom Capabilities, and Installer, as well as a few key improvements that will enhance the overall Polarity user experience. Check out the new features and improvements below! New Features Connection Settings Polarity’s all-new connection settings page makes it […]
ThreatConnect and ServiceNow: More Integrations for Better Context
We’re strengthening our partnership with ServiceNow® by offering more robust integrations with the ServiceNow Orchestration and ServiceNow Security Operations products, as well as launching a new Playbook App for managing table records across all ServiceNow products. With this update, we’ve added three types of integrations to the ServiceNow and ThreatConnect Platforms, each with its own […]
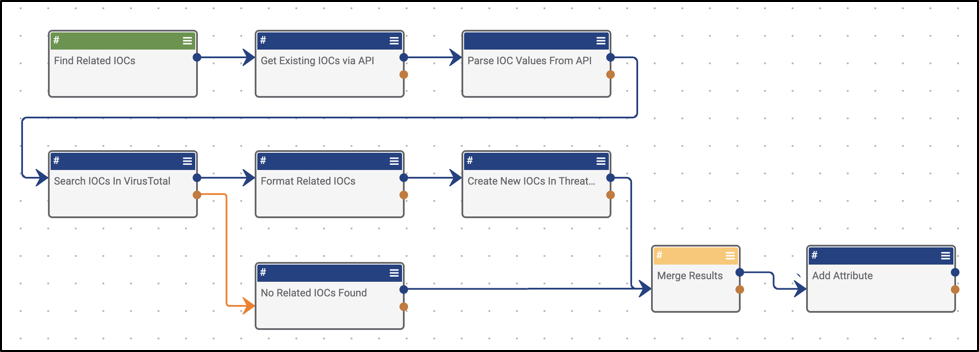
Playbook Fridays: Query Jira for Ticket Information
As someone in Customer Success for ThreatConnect, we are constantly asked to push the limits of our creativity for a customer. The Playbook below is the result of such a request. So without ado, I present Get all available information from JIRA! The prerequisites that you will need for this Playbook: URL to JIRA Instance […]

Seamlessly Analyze Windows Events with Polarity
Anyone who’s worked with Windows Event Logs during forensic investigations knows how tedious and time consuming it can be. Working with large data sets of random numbers without context immediately available, forensic analysts end up spending their time constantly referencing Windows and flipping between multiple screens. Analyzing Windows Events using Polarity is a different story. […]
Playbook Fridays: Query Hashes via Email Submission
We were asked by a customer to extend the analysis functionality of ThreatConnect to other SOC personnel that didn’t have direct access to the Platform. So we did. This Playbook creates a new process in which non-ThreatConnect users can get on-the-fly analysis and context into potential hash IOCs they’ve encountered, and simplifies the process of […]

Security Teams Can Spend Less Time Querying & More Time Analyzing with Polarity’s Updated Splunk Integration
We’re excited to announce our updated integration with Splunk, a platform that empowers teams from Security to IoT to Business Analysis with data. These updates will enable Polarity users to retrieve a more in-depth analysis from different Splunk queries even more seamlessly than before. Now, instead of running the same Splunk query over and over to get […]
Playbook Fridays: Generate Intelligence Reports, Part 2
As promised, below is how to customize this app to change the disclaimer, and contact information. However, I encourage you to stick around as I dig in for a deeper dive, explaining in detail all of the code within this app. With that said, let’s go! Replace everything after the = on Lines 32-34 and […]
Polarity – urlscan Integration
Ever gotten an email with a link and wondered what that link is and if you should click on it? Ever seen a random url in your logs and wondered what it is? Well, with Polarity’s latest integration with urlscan, you will always know if that url or domain is malicious or not! What is […]
Best Practices for Writing Playbooks, Part 2
This is Part 2 of the Best Practices for Writing Playbooks in ThreatConnect blog post series. This time, I wanted to get into the weeds on some best practices for development and testing. If you haven’t already read it, I highly recommend taking a minute and reading Part 1, here. To Playbook or not to […]
Playbook Fridays: Generate Intelligence Reports
John Locke, a wise man, once said, “No man’s knowledge here can go beyond his experience.” The same is true with the latest release of ThreatConnect that includes quite a few new features. The feature that has me excited the most is the AppBuilder functionality. The primary reason is that I can see the full […]
The Secret to our (Customer) Success
I recently sat down with Jody Caldwell, the Senior Director of Customer Success at ThreatConnect, to pick his brain and understand the specifics of how we help a customer from initial deployment throughout the entire span of their relationship with ThreatConnect. Will you describe your role at ThreatConnect? What does a day look like for […]
