
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
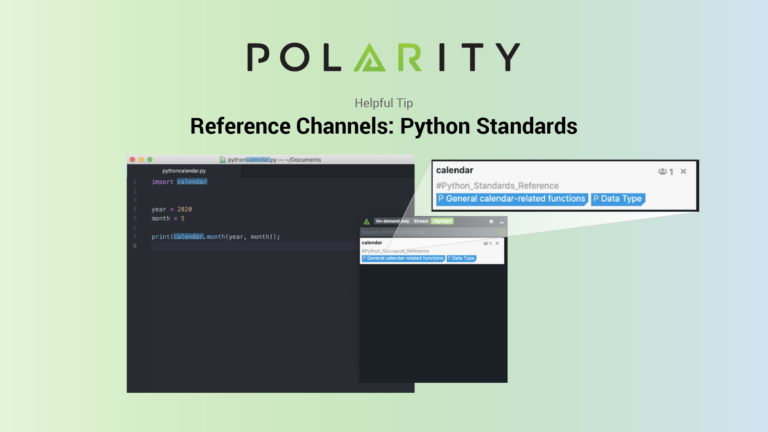
Polarity Reference Channels: Python Standards
Today’s post continues an ongoing series on Polarity User Tips. Data tells a story, Polarity helps you see it with Augmented Reality overlaying contextual information as you work, giving you the right data at the right time to make informed decisions and take action with speed (no glasses or goggles required). This guide explains how […]
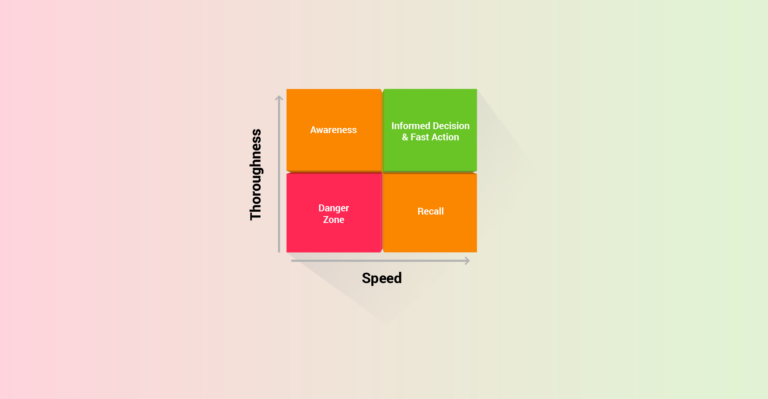
Survey Says: SOC Still Plagued by Inefficiency
There is no shortage of interesting research characterizing the challenges faced by SOC teams. Two recent reports from Exabeam and Devo/Ponemon include all the well known stats reminding us that SOCs suffer from too many tools, not enough people, and ongoing challenges with key metrics like MTTD and MTTR. Both reports also include a few unique perspectives on data […]
5 Reasons CISOs Need Security Operations, Automation, and Orchestration (SOAR)
At ThreatConnect, we are out to change the way security works by making cybersecurity software that reduces complexity for everyone, makes decision making easy and unifies processes and technology to constantly drive down risk. To make good on this core idea, we’ve evolved from our heritage as a leading Threat Intelligence Platform (TIP) to deliver […]
Realizing the Benefits of Security Orchestration, Automation, and Response (SOAR)
SAO, TIP, SIRP: Better Together When industry analyst firm Gartner, Inc. coined the term SOAR (Security Orchestration, Automation, and Response), it was because they recognized the benefits innately achieved when the capabilities of three previously very separate platforms are fused together: security orchestration and automation (SOA), security incident response (SIR) and threat intelligence platform (TIP) […]
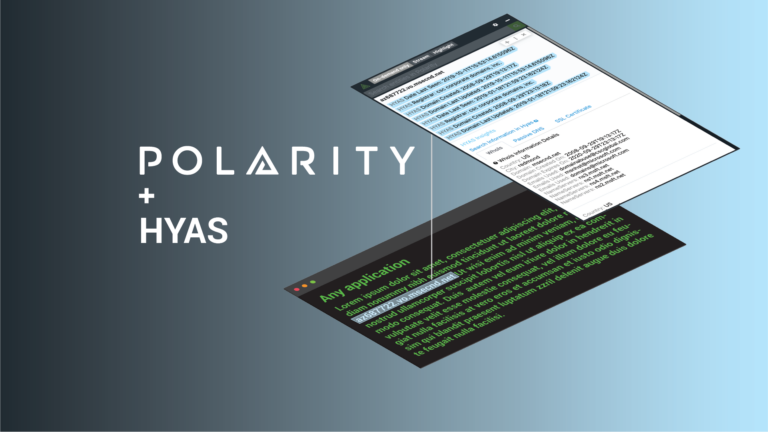
Immediately Triage Threats with the Polarity-HYAS Integration
Today’s post continues an ongoing series on Polarity Integrations. Data tells a story, Polarity helps you see it with Augmented Reality overlaying contextual information from the applications you use every day, no glasses or goggles required. With over 100 powerful integrations, Polarity’s open-source Integrations Library arms you with the right data at the right time […]
ThreatConnect and Tanium: Improved Incident Response with Intel Packages
ThreatConnect and Tanium’s partnership just got stronger. Recently, we released 3 Apps for Tanium Threat Response as well as developed a brand new Playbook App for Tanium Platform. With these Playbook Apps, you can take immediate action to investigate, stop, and remediate potential threats at the endpoint based on external threat intelligence. Let’s dive in! […]
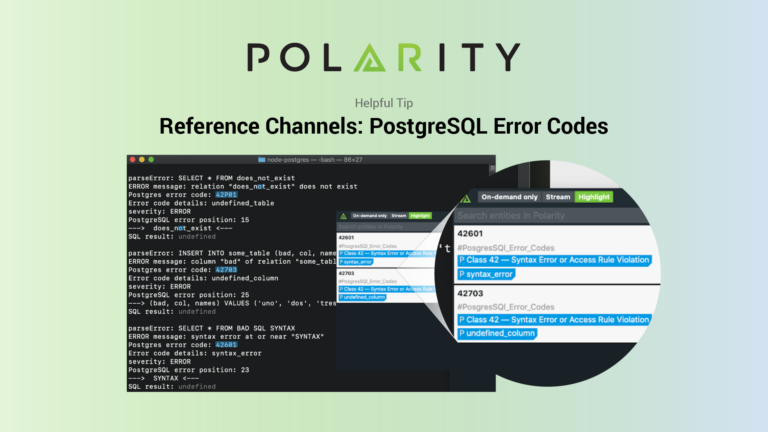
Polarity Reference Channels: PostgreSQL Error Codes
Today’s post continues an ongoing series on Polarity User Tips. Data tells a story, Polarity helps you see it with Augmented Reality overlaying contextual information as you work, giving you the right data at the right time to make informed decisions and take action with speed (no glasses or goggles required). This guide explains how […]
Playbook Fridays: Converting your IOCs to CSVs
Welcome to ThreatConnect’s Playbook Fridays! We will continually publish posts featuring Playbooks (and sometimes Dashboards!) that can be built in the Platform. ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can […]
ThreatConnect Research Roundup: More Kimsuky “AutoUpdate” Malware
Howdy, and welcome to the ThreatConnect Research Roundup, a collection of recent findings by our Research Team and items from open source publications that have resulted in Observations of related indicators across ThreatConnect’s CAL™ (Collective Analytics Layer). Note: Viewing the pages linked in this blog post requires a ThreatConnect account. In this edition, we cover: […]
ThreatConnect Research Roundup: Kimsuky “AutoUpdate” Malware
June 19 2020 Edition Howdy, and welcome to the ThreatConnect Research Roundup, a collection of recent findings by our Research Team and items from open source publications that have resulted in Observations of related indicators across ThreatConnect’s CAL™ (Collective Analytics Layer). Note: Viewing the pages linked in this blog post requires a ThreatConnect account. In […]
Polarity for Phishing Email Analysis
Today’s post continues an ongoing series on Polarity Use Cases. Data tells a story, Polarity helps you see it with Augmented Reality overlaying contextual information as you work, giving you the right data at the right time to make informed decisions and take action with speed. No glasses or goggles required, Polarity is software that […]
Orchestration With and Without Intelligence: What’s the Difference?
Orchestration informed by security intelligence from within your environment, and threat intelligence from a variety of external sources, is more effective, resilient, and adaptive. An intelligence-led approach will inform your strategy for orchestration in two key ways: Intelligence on an adversary’s capabilities, attack patterns, and intent will inform how you build and configure orchestration capabilities […]
