Posted
ThreatConnect is changing the way security works and that means better alignment with, and transparency to, the business. ThreatConnect’s intelligence-driven, security operations solutions include both Threat Intelligence (TIP) and Security Orchestration, Automation and Response (SOAR) platforms. These solutions are designed to put intelligence at the core of every security decision, improve the way your security teams work together and also help align your security focus to the issues that matter most. With ThreatConnect you align your team to a common, shared vision that maps back to business priorities. This ensures that security is defending against the right threats and helps demonstrate the value of security to the rest of the business. This is accomplished through dashboards that drive and streamline action for maximum effect and efficiency and through defined, demonstrable ROI, and metrics that matter.
Dashboards and Reporting
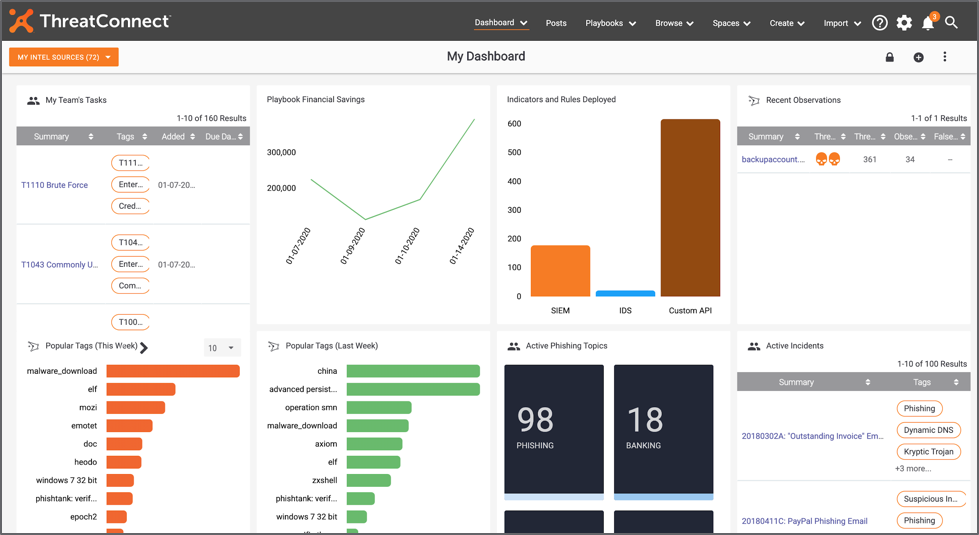
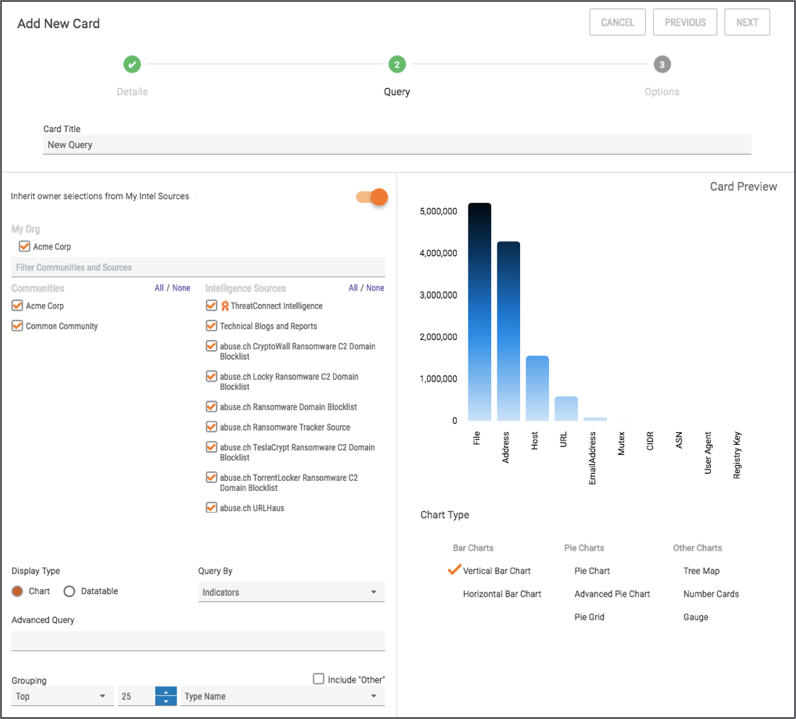
Using ThreatConnect’s Dashboards, you can easily visualize data that helps you gain a better understanding of the threats your organization faces, helps you orchestrate and automate actions to counter those threats, and shows the overall impact of your security efforts. You can automatically monitor your security operations and intelligence in a way that is actionable and meaningful for you and your team. With customizable reports you can access the information you need in a digestible format. View, edit, or create custom dashboards to track the metrics that will inform critical decision-making for your security operations and your business.
With ThreatConnect you can:
- Choose from pre-built dashboards to view the data that is most critical and useful for your team, to monitor the most urgent security operations needs, or to get more direct insight from your intelligence sources
- Monitor recent history, open tasks, active incidents, observations, false positives, and more with pre-built and configurable cards
- Easily drill down from charts and data tables to dig deeper into more specific information
- Clearly articulate impact and actionable insights by presenting your data in the most effective formats including sparklines, bar charts, tree maps, and datatables
Demonstrate Cost Control with Customizable Metrics
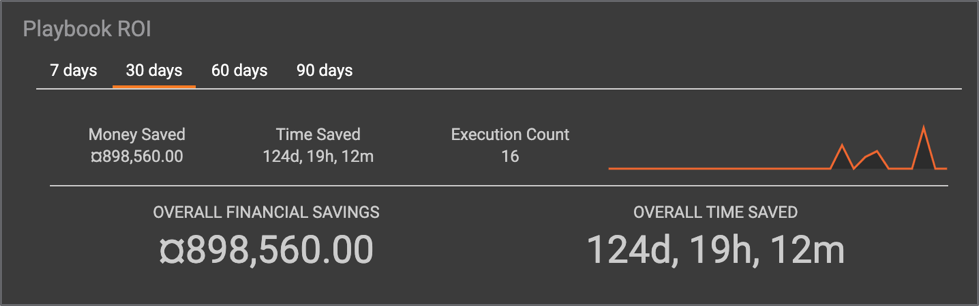
Security is seen as a huge cost center in most organizations. Demonstrating consistency in tracking your team’s spend shows that you’re always considering costs when making decisions. The savings seen when implementing automation can be seen through ThreatConnect’s ROI Calculator built into every Playbook. Customizable values tell you, based on how many times any given Playbook has been run, how much your organization has saved to date by implementing an automated workflow.
ThreatConnect is the only solution that combines intelligence, orchestration and automation, analytics, and templated workflows relevant for each member of the security team. It contains all the functionality you need to drive informed decision-making based on the power of your organization’s threat intelligence. We provide not only the ability to orchestrate your security functions, but also the confidence that you are basing your tasks and decisions on vetted, relevant threat intelligence. With ThreatConnect, organizations are able to better align their teams, streamline processes and technology, and measure the impact of their efforts against core business goals.
