
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
ProxyNotShell Zero-day Vulnerabilities Exposed
The Latest on ProxyNotShell and How To Respond If You’re Impacted Word is spreading fast about two of the newest zero-day (0-day) vulnerabilities targeting Microsoft Exchange servers, now referred to as “ProxyNotShell” – and how their initial mitigations fell short of expectations. Given the evidence that these vulnerabilities are already being exploited to mount attacks […]
Cloud-Delivered Cyber Threat Intelligence Platforms Bring Quick Time to Value
If you don’t have a cyber threat intelligence (CTI) platform, then you need one. The challenge is getting your entire security team, from the CSO or CISO to the security and threat-analyst teams in the trenches, trained and able to use the platform to support daily incident response, network defense, and threat analysis. That’s the […]
Threat Graph – Seeing is Believing
We all know the saying that, “a picture is worth a thousand words.” It is a fact that people derive meaning faster from imagery and graphics. At our core, humans are visual. Imagery can convey thoughts much faster and more efficiently than just words. Consider an example where you need to describe the shape of […]

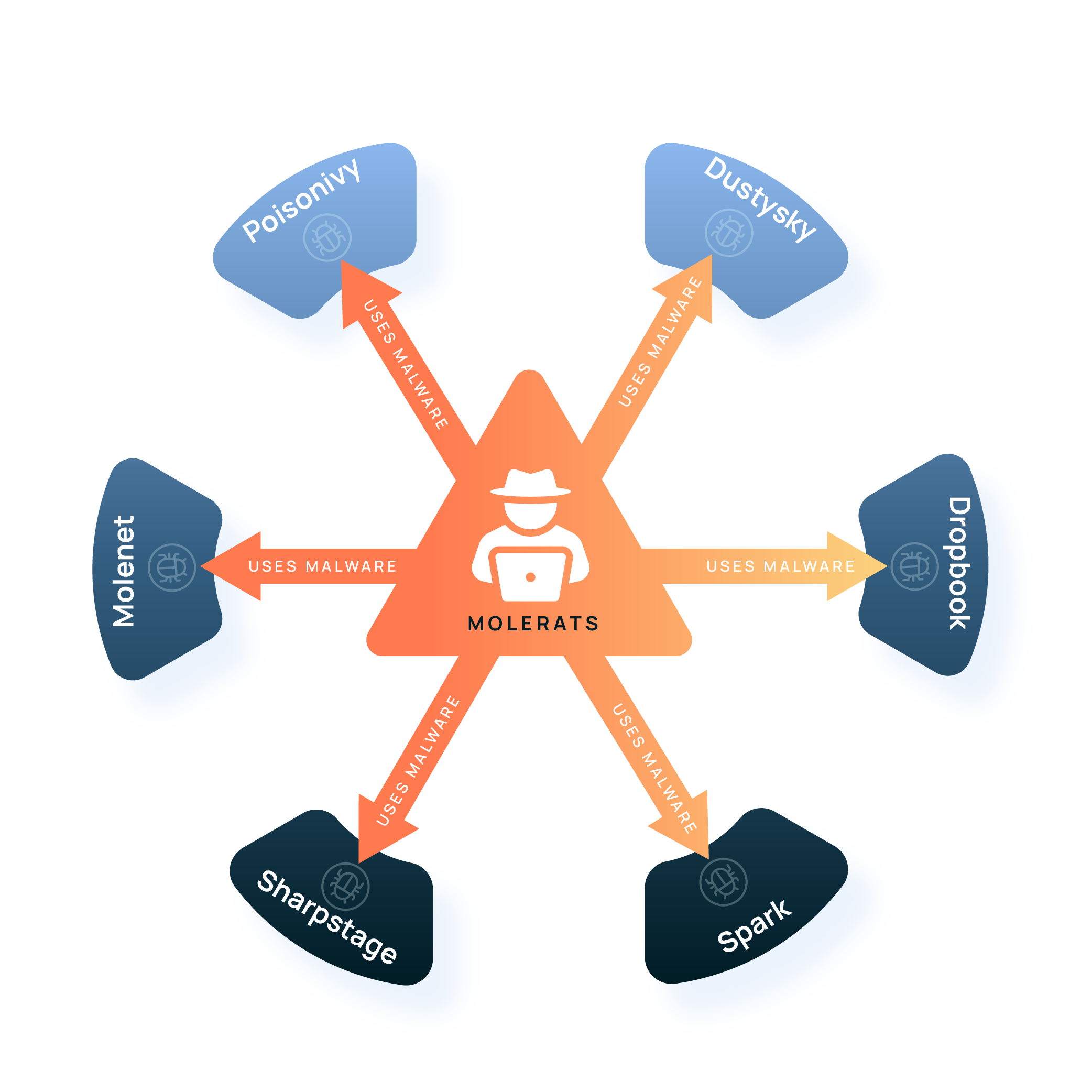
Top Malware Strains Used by Threat Actors in 2021 – CISA Alert
Malware continues to grow in sophistication as record numbers of cyberattacks occur worldwide. Malware is often the tip of the spear for threat actors — first, they use it to compromise a computer or mobile device and then gain access to it. In recognition of the expanding threat that malware presents, the US Cybersecurity and […]

The Top Security Risks of Remote Working
The pandemic brought major changes to the way organizations work. The rapid adoption of work from anywhere (WFA), completely changed the enterprise cybersecurity landscape. A recent survey, led by Ipsos Research and management consulting firm, McKinsey, shows that 92 million US workers have the opportunity to work remotely. During the survey, 25,000 Americans were queried, […]
Black Hat USA 2022 Cybersecurity Conference Highlights
Black Hat USA, also known as Hacker Summer Camp, was held on August 10-11 at the Mandalay Bay Resort in Las Vegas, marking its 25th anniversary of the conference, and it was great to see everyone in person! Our team had a great time at the conference and wanted to share some highlights they noticed […]
FBI FLASH on RagnarLocker Ransomware Expands Known Indicators of Compromise
The Federal Bureau of Investigation has recently released an updated FLASH Number CU-000163-MW as part of the overall Government efforts to identify and document ransomware threat actors and the multitude of ransomware variants they deploy. RagnarLocker first surfaced in April 2020 and continues to impact a wide variety of critical infrastructure sectors. These sectors include […]

5 Steps to Combat Phishing With Intelligence-Powered Security Operations
Did you know there were over 1 million phishing attacks just in Q1 of this year? 1,025,968, to be exact! Phishing attacks are getting more sophisticated and involve more clever ways to entice end users to click on those links. Security operations teams are overwhelmed with the number of suspected phishing emails and the lack […]

Top 3 Ways To Defend Your Organization – CISA Issues Critical Alert on MedusaLocker Ransomware
The Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Security Agency (CISA), the Department of the Treasury, and the Financial Crimes Enforcement Network (FinCEN) have recently released a Cyber Security Advisory AA22-1812A to provide updated information on MedusaLocker ransomware. This advisory is part of the Government’s efforts to document ransomware threat actors and the […]
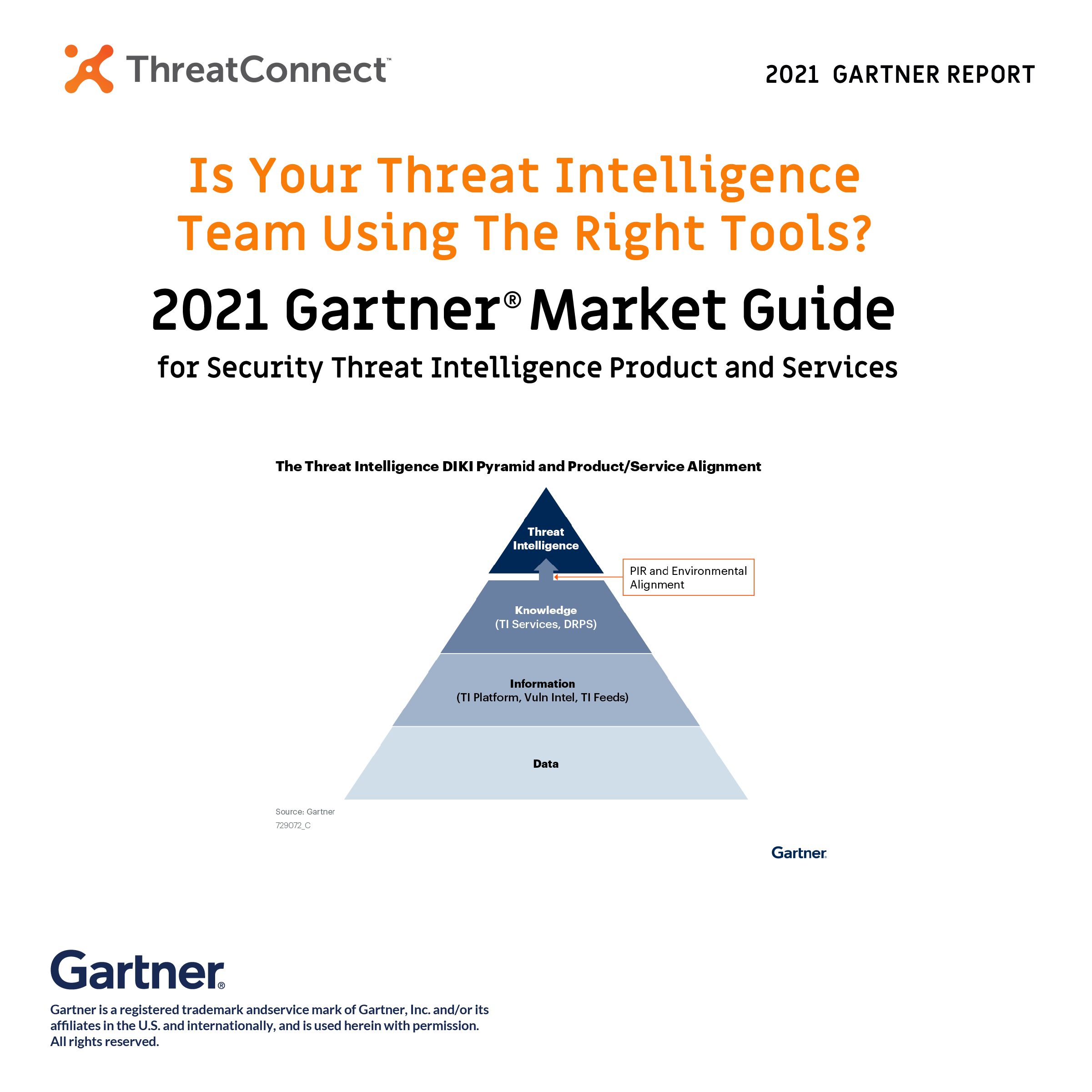
Put Threat Intelligence at the Core of your Security Operations
Threat intelligence teams have a problem, a big data problem due to the velocity, variety, and volume, of the different sets of data they collect. Data comes through non-stop in different forms, from different sources, and from different environments. To make matters worse, not all data is good data because it’s not always accurate or […]
Community Powered Insight Gives Defenders the Advantage
Leveraging Automation and the Cloud to Improve Cyber Response Threats are moving faster than ever in today’s cyber threat environment. A timely and impactful response to an ongoing cyberattack is critical. Yet, still, today, many companies cannot detect any potentially malicious activity, especially in the early phases of an attack. Most companies are just outnumbered […]

When It Comes To CRQ, What Is An “Open” Model and Is It The Right Question To Ask?
As more companies look to quantify cyber risk in financial terms, a common question we hear all the time is, “which model (or approach) should I use?.” I saw an interesting quote from a Gartner® research note titled “Drive Business Action with Cyber Risk Quantification “ that spoke about where the CRQ space is going: […]
