Posted
When Risk Quantifier (RQ) became a part of the ThreatConnect family last year, it was clear we had big plans when it came to changing the way security works. We spoke about the deep rooted belief we have that understanding and quantifying risk is critical to building an effective security program. Organizations are seeking to quantify their cyber risk in order to better align security to the business, drive remediation and response activities, support investment decisions and demonstrate return on security investment.
Well, the first step to making the solution to this challenge a reality is here. Now, when you combine ThreatConnect’s TIP and SOAR capabilities with ThreatConnect Risk Quantifier (RQ), you’re not only able to better prioritize vulnerabilities based on the level of financial risk they introduce to your business, but also take action on those vulnerabilities directly from the ThreatConnect Platform.
With this integrated solution, users can quantify the financial impact of a given CVE (Common Vulnerabilities and Exposure) to their organizations with ThreatConnect Risk Quantifier (RQ) and automatically import that value into your ThreatConnect TIP or SOAR solution to help prioritize response actions like patching and investigation.
In a Ponemon Institute survey of 3,000 IT professionals, 72% reported difficulty in prioritizing what needs to be patched. Perhaps even more troubling is that 60% of those surveyed indicated that breaches at their organization were linked to a vulnerability where a patch was available, but not applied.
This integration puts forth a new approach – an approach that is built around determining prioritized remediation based not solely on CVSS score, but on how this vulnerability could potentially affect your organization. This unique approach takes financial risk information which has been calculated with your applications and controls in mind, and gives you immediate insight into financial impact and vulnerable endpoints, empowering you to make confident decisions backed by real-time data.
The benefits this has for security operations analysts are immense, and those benefits are felt across the entirety of the security team – the whole way up to senior leadership. In a recent blog, we introduced readers to Sriya. Sriya will help us clearly articulate the strategic or business-level benefits achieved through ThreatConnect solutions. If you missed her, I’ll reintroduce her now:
Meet Sriya
In the process outlined below, we use a CVE Report within ThreatConnect to notify us of a vulnerability that could potentially affect our organization.
Let’s walk through how ThreatConnect makes it possible to quickly understand financial impact, identify vulnerable endpoints, and issue a patching request without leaving the Platform.
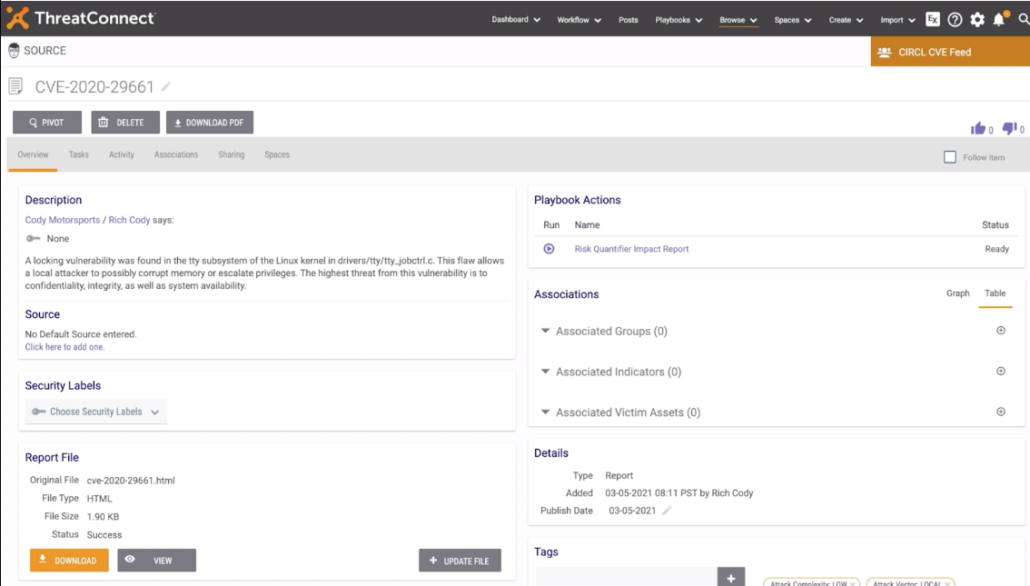
Above, you’re able to see how easy it is to request additional information from ThreatConnect RQ about a vulnerability identified in a CVE Report within the ThreatConnect TIP & SOAR.
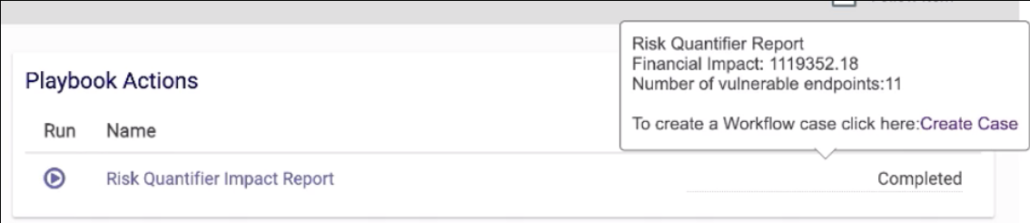
Almost instantaneously, receive information on the financial impact this vulnerability could have on your organization if exploited as well as the number of vulnerable endpoints. Then, if the information deems it necessary, Create a Case immediately from the same interface with ThreatConnect Workflow functionality to investigate further or request a patch.
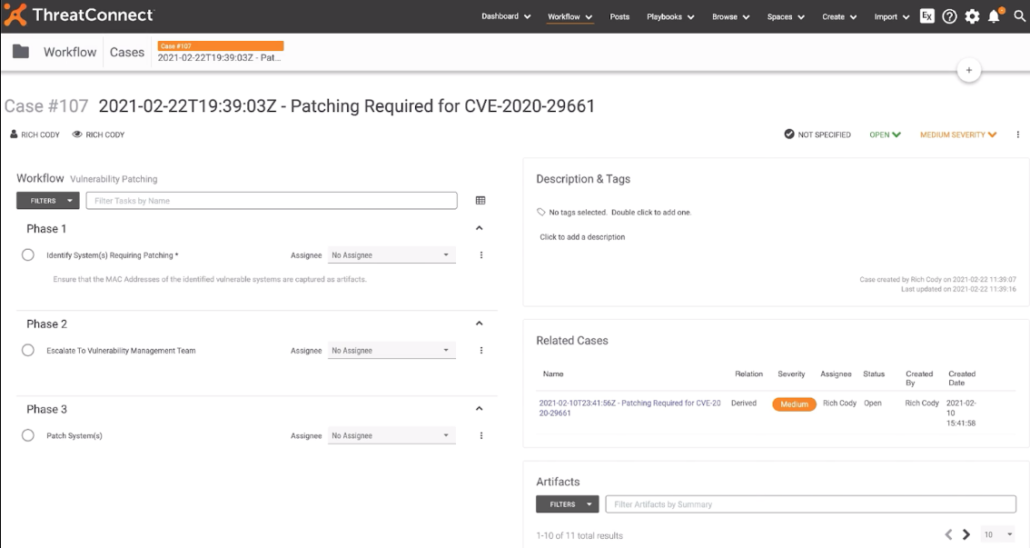
Upon requesting a Case be created, thanks to a template that’s been pre populated and approved by your team, agreed upon steps to patch the CVE will be populated and the process can continue on as determined and be documented appropriately.
Sriya the CISO Says..
Allowing my team to retrieve how a specific CVE could financially impact my organization based on information that is specific to the controls and applications I have in place ensures that my team is making well-informed decisions – ultimately better protecting our organization. Additionally, it incorporates a level of information sharing and efficiency that previously was impossible for me to achieve. My team is working smoother and more confidently than ever before.
A full explanation and walkthrough of the above can be seen in this short, 5-minute video:
By breaking down information and process silos for each stakeholder, they are in turn broken down across the entire team. Everyone is on the same page related to the risks that matter most, with threat intelligence, security processes and response plans all aligned together. This increased visibility helps reduce redundancies and improve efficiency across the entire program.
The following actions are available via the RQ Playbook App for ThreatConnect TIP & SOAR:
- Get Vulnerable Endpoints By CVE: This action returns arrays detailing the associated applications and endpoints with this CVE.
- Get Financial Impact by CVE: This action returns the total monetary contributory effect of the CVE ID to the enterprise.
- Get Endpoint Financial Information: This action returns the max Single Loss Expectancy (SLE) value and type of attack for the associated CVE.
Together, ThreatConnect’s solutions can help organizations to quickly understand their level of financial risk and initiate important response efforts. If you’re a ThreatConnect customer, please reach out to your dedicated Customer Success Team for more information. If you’re not yet a customer and are interested in more information about ThreatConnect TIP, SOAR, or Cyber Risk Quantification products, please reach out to sales@threatconnect.com.

