Posted
ThreatConnect is excited to announce a new integration with Spur! The integration with Spur’s Context-API allows a range of ThreatConnect users – intel analysts, detection engineers, SOC analysts, threat hunters, and incident responders – to save effort when enriching IP address Indicators to facilitate their work. Spur enables threat intel and security operations teams to gain advanced detection of anonymization and threats to counter fraud and other malicious activity.
Spur Context-API is a REST API service providing detailed IP context. It offers rapid IP search with actionable data, including client behaviors, geographical concentration, and associated risks. The outputs analysts benefit from include autonomous system details, client behavior and geographic information, known risks and threats associated with the IP, VPN and proxy insights, org details, and much more.
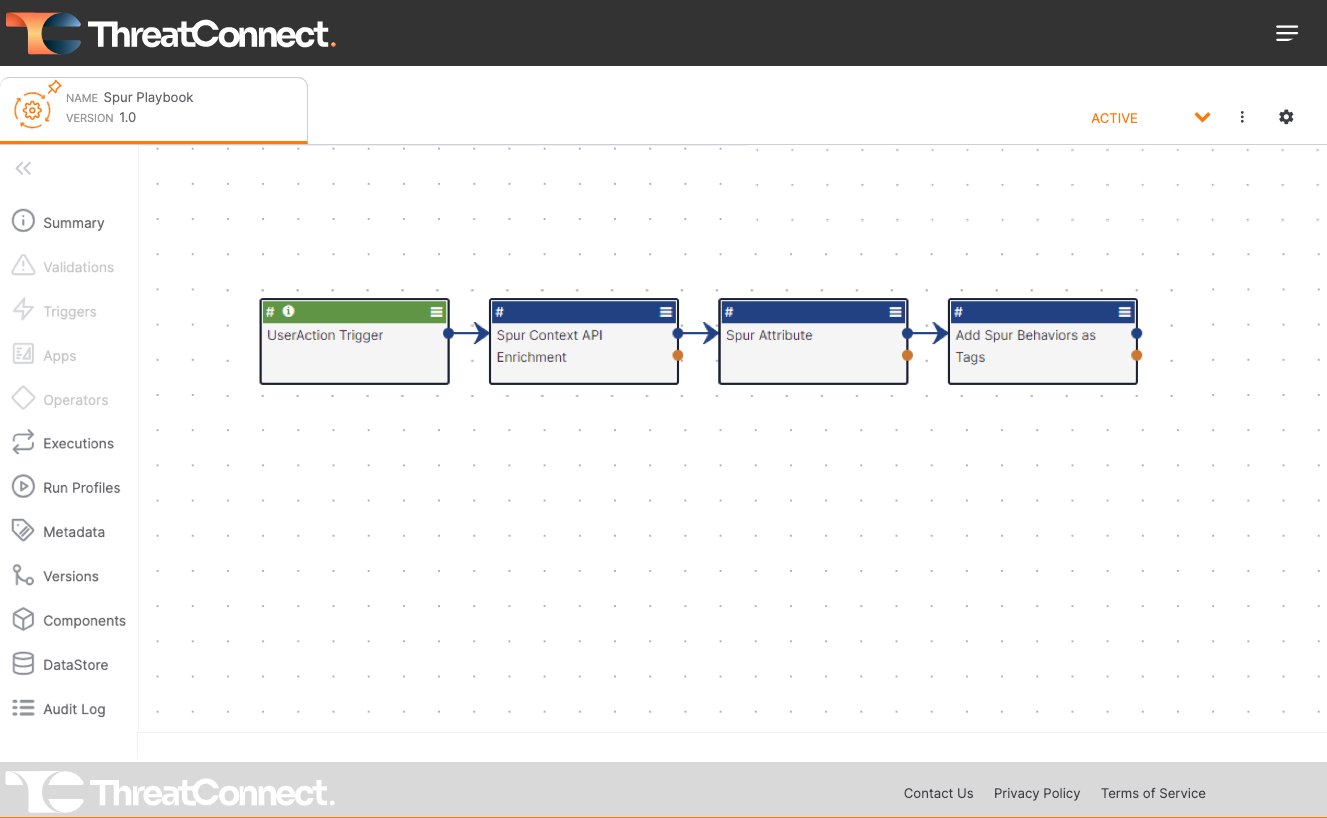
Using Spur’s Context-API is really easy. It can be leveraged via Playbook automations in the ThreatConnect TI Ops Platform. Playbooks allow organizations to easily create custom automations using a drag-and-drop, low-code interface. Access to Spur’s rich IP address context is done using a pre-built Playbook App. This allows IP address context to be quickly incorporated into new and existing automations, saving analysts time and reducing manual effort.
Want to learn more?
Checkout the Spur Playbook App in the ThreatConnect Marketplace. To learn more about how ThreatConnect and Spur can help you reduce malicious attacks and fraud activities, reach out to an expert at ThreatConnect today.

