Buyer’s Guide for Threat Intelligence Operations
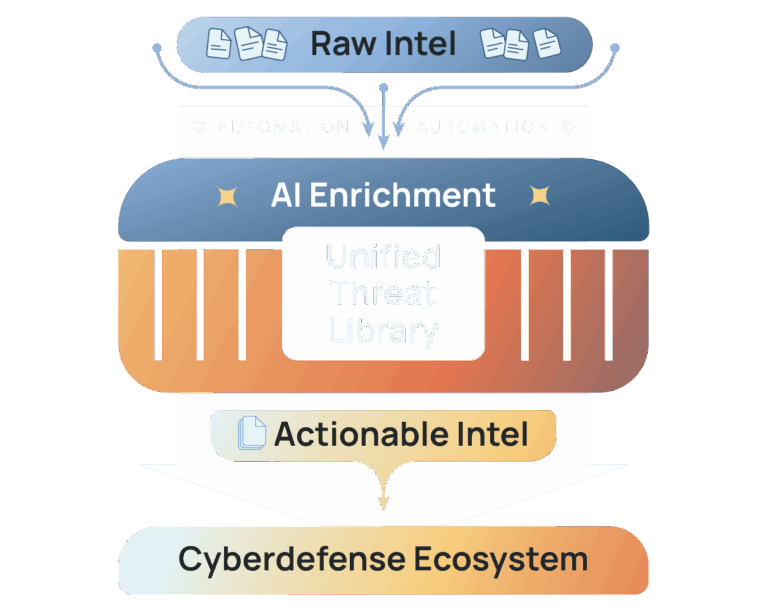
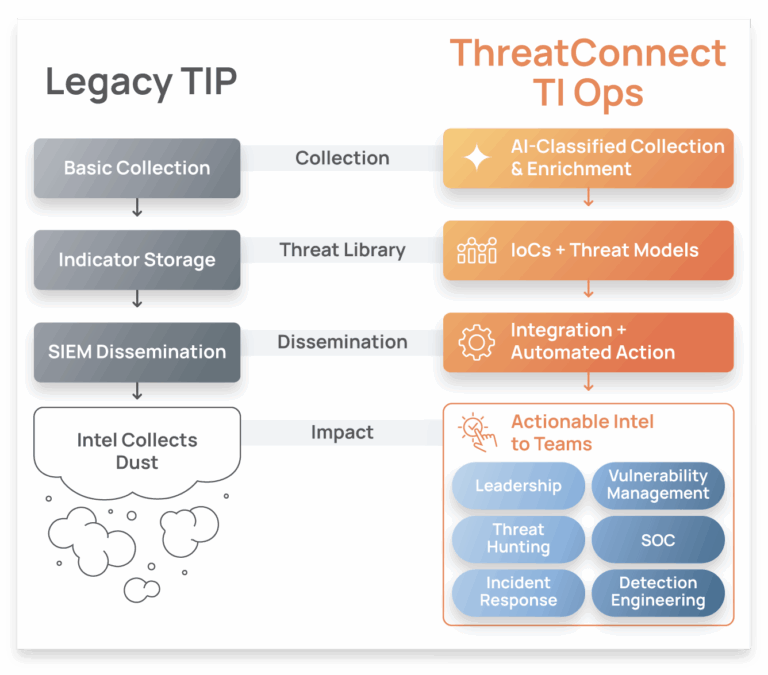
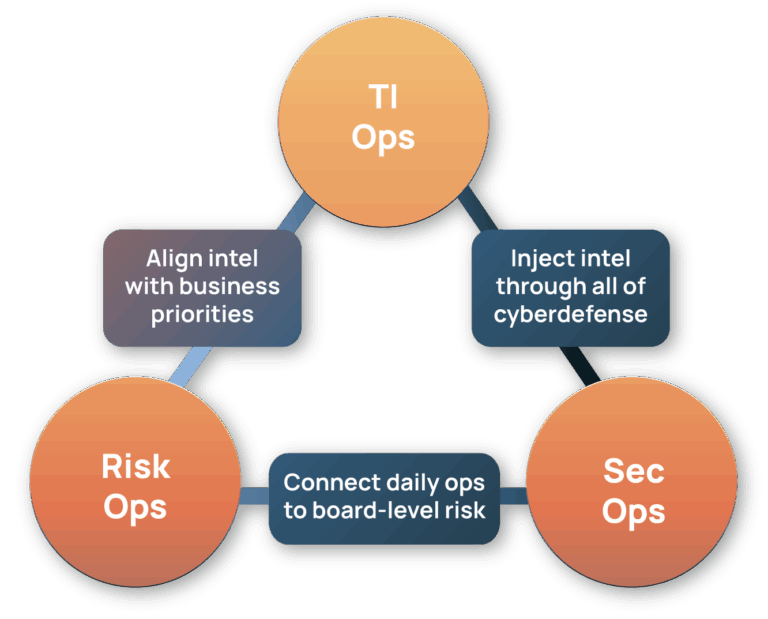
The ThreatConnect Buyer's Guide for Threat Intelligence Operations is a comprehensive resource tailored for cybersecurity leaders, strategists, architects, and analysts seeking to enhance their organization's security and risk posture by effectively utilizing cyber threat intelligence (CTI).











Trusted By Leading Companies
ThreatConnect allows our organization to collect, analyze, and share intelligence with various teams in a single platform, effectively reducing the amount of time needed for an analyst to produce actionable intelligence to share with our partners and stakeholders.
ThreatConnect enabled us to quantify ROI and to define business requirements for onboarding technology. Tools need to be open to automation, scalable, and reliable
ThreatConnect is a one stop shop for me. I can get intel, risk, and deep dive into threats and source, all in one place.
ThreatConnect has a vision for security that encompasses the most critical elements – risk, threat, and response. The RQ solution strengthens their offering and increases alignment to our core strategic objectives with one platform to assess our risk and automate and orchestrate our response to it.