No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.

The ThreatConnect TI Ops Platform
The ThreatConnect TI Ops Platform, built on an industry-leading threat intelligence platform, enables security teams to confidently forge their path to smarter security with intel-powered security operations. ThreatConnect enables the operationalization of cyber threat intelligence analysis and management, and by leveraging native automation, orchestration, and knowledge capture, it lets teams work smarter, faster, and better […]
ThreatConnect CAL™
ThreatConnect’s Collective Analytics Layer (CAL) combines powerful insights from the ThreatConnect community of users with machine learning-powered analytics to generate actionable, high-fidelity threat intelligence that lets you prioritize the greatest risks to your business. CAL anonymously leverages billions of data points, offering real-time insights into how widespread and relevant a threat is, providing global context […]

Leveraging Channels in Polarity
Discover how Polarity enhances data management with channels and annotations in this webinar. Learn from experts Joe Miller and Ed Dorsey to optimize your workflow and improve business operations.
Enterprise Defense at the Speed of Data
Quickly and efficiently turn data into intelligence and make informed decisions Today’s threats are relentless. Cyberattacks are often multi-year campaigns targeting valuable, sensitive data and have many business implications — brand reputation, lost revenue, and more. In this paper, we discuss how an intelligence-driven security program gives your company or agency a fighting chance to […]

Polarity Source Analytics: Enabling Leaders and Upleveling Teams
Join our session to explore how Polarity’s telemetry data can enhance your data analysis. Learn to set up source analytics, integrate data seamlessly, and improve workflows. Watch now to revolutionize your processes!

Peaky Blinders: Combat Ransomware Gangs with High Fidelity Intelligence-Driven Operations
The plague of ransomware continues to grow in 2022 with attacks raging through industries and affecting structures such as oil pipelines, payroll systems, and managed service provider software. Many reports indicated that there were more than 700 million attempted ransomware attacks in the past year alone. The resulting costs to businesses and the time lost […]
Enabling Analysts: Intelligence-Driven CVE Enrichment & Remediation
Security analysts need the ability to filter out the noise and focus on what matters most – particularly when it comes to vulnerability management. By using threat intelligence to enrich response programs, it makes it much easier to prioritize patching and more importantly, reduce the time it takes to respond. We call this Intelligence-Powered Security […]

How to SOAR with Risk Based Vulnerability Management
Risk-based vulnerability management (RBVM) is an ideal use case to operationalize and automate within SOAR as it needs to connect threat intelligence, data collection, enrichment, cross-team workflows, and incident management, all labor intensive processes. The integration of cyber risk quantification in the RBVM process via SOAR makes financial impact based decisions about which vulnerabilities to […]
Key Functionalities of a Modern CTI Program
Everyone knows security is overloaded work wise – not everyone understands what that means. Cyber Threat Intelligence (CTI) is typically very technical so how can you convince the teams setting business objectives and allocating resources (for budget) of what the cybersecurity priorities should be? A modern CTI program needs to show value to the business […]

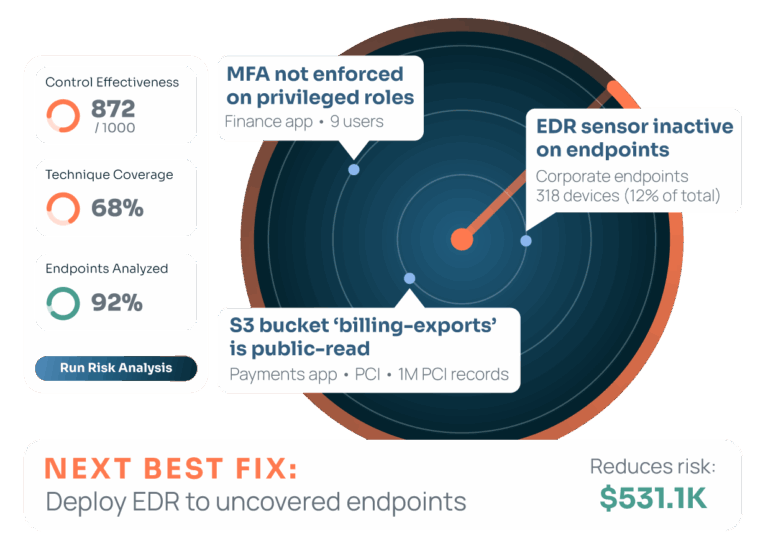
Operationalizing Cyber Risk Quantification
Cyber risk has long been acknowledged as one of the top risks facing companies of all sizes. Many security leaders struggle with communicating cyber risk in business and operational terms that matter to C-suite executives and boards of directors.
The Fastest Triage & Action Possible
Enhance cybersecurity analysis with Polarity. Boost memory recall, streamline data discovery, and improve collaboration through advanced tools like instant recall, federated search, and augmented reality.

Instant Recall of Flashpoint Intelligence with Polarity
Explore how the integration of Polarity and Flashpoint provides real-time intelligence, enhancing cybersecurity operations and empowering teams to respond to threats faster and more effectively.