
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
Finding Nemo(hosts)
How to identify potential malicious infrastructure using ThreatConnect, DomainTools, and more All that is bad is not known Individual indicators are often highly perishable, but understanding the patterns adversaries use to stand up infrastructure can give us a leg up by illuminating suspicious domains potentially prior to an attack. But where to start? How to […]
How to Use Threat Intelligence & Orchestration to Defeat Stranger Threats
Threat Intelligence and Orchestration can come together to defeat threats to your network, or D&D monsters…whichever you face. When watching Stranger Things it’s easy to notice many incidents throughout the show worthy of further investigation. Many of the characters in the show could actually benefit quite a bit from the processes and techniques security professionals […]
Getting Started with the ThreatConnect Query Language (TQL)
From Neanderthal to Ninja Users in ThreatConnect have a lot of data to go through, and a big part of our job is finding ways to empower them to find the right data faster. Our Browse Screen harbors an array of different filters you can apply and chain together, slicing and dicing the dataset to […]
Phantom of the Opaera: New KASPERAGENT Malware Campaign
KASPERAGENT Malware Campaign resurfaces in the run up to May Palestinian Authority Elections ThreatConnect has identified a KASPERAGENT malware campaign leveraging decoy Palestinian Authority documents. The samples date from April – May 2017, coinciding with the run up to the May 2017 Palestinian Authority elections. Although we do not know who is behind the campaign, […]
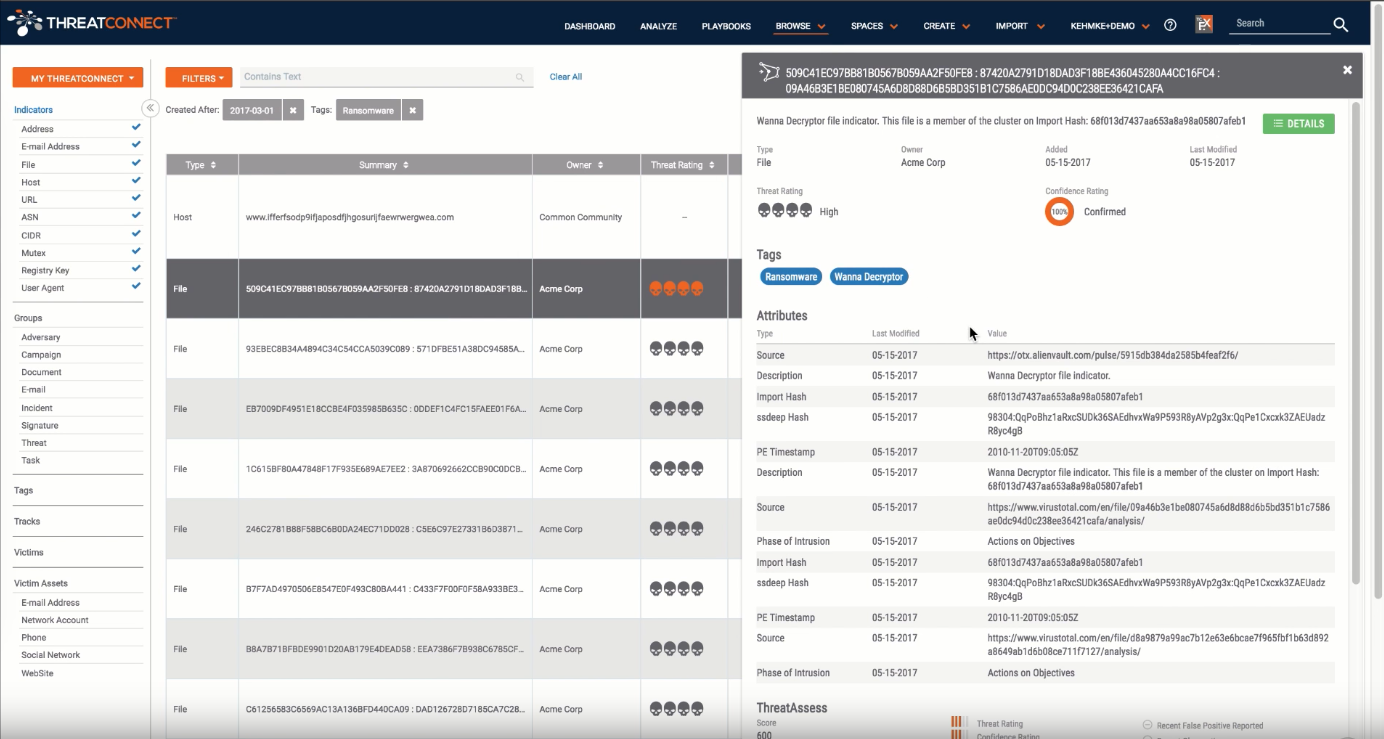
Get Started with Cyber Threat Analysis: How to Research Ransomware
Learn How to Research Ransomware in ThreatConnect We recently recorded a video to show what members of our Research Team do on a daily basis within the ThreatConnect platform to perform cyber threat analysis, research threats, conduct investigations, create new intelligence, and more. Our hope is that this video will help to educate viewers on the […]
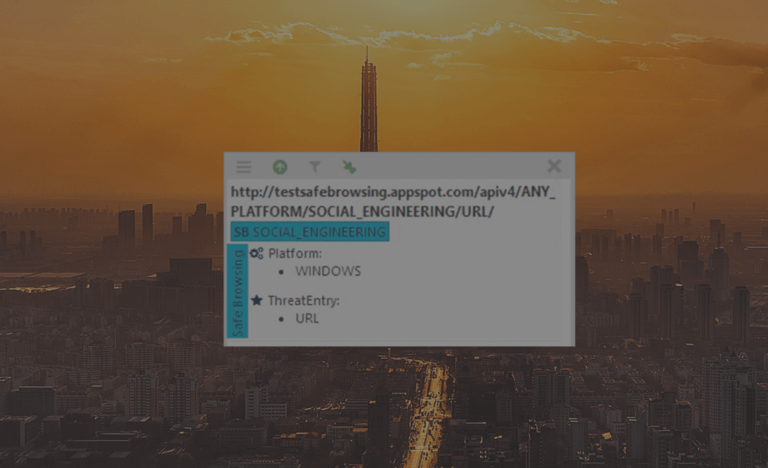
Always know if that URL is Malicious
Did you know that not every website you visit, or link that you might click on is safe? Well I hate to break it to you, but a decent amount of them are not. To mitigate that, Google has released their database of URLs that they consider malicious in some way, called Google Safe-Browsing. This […]
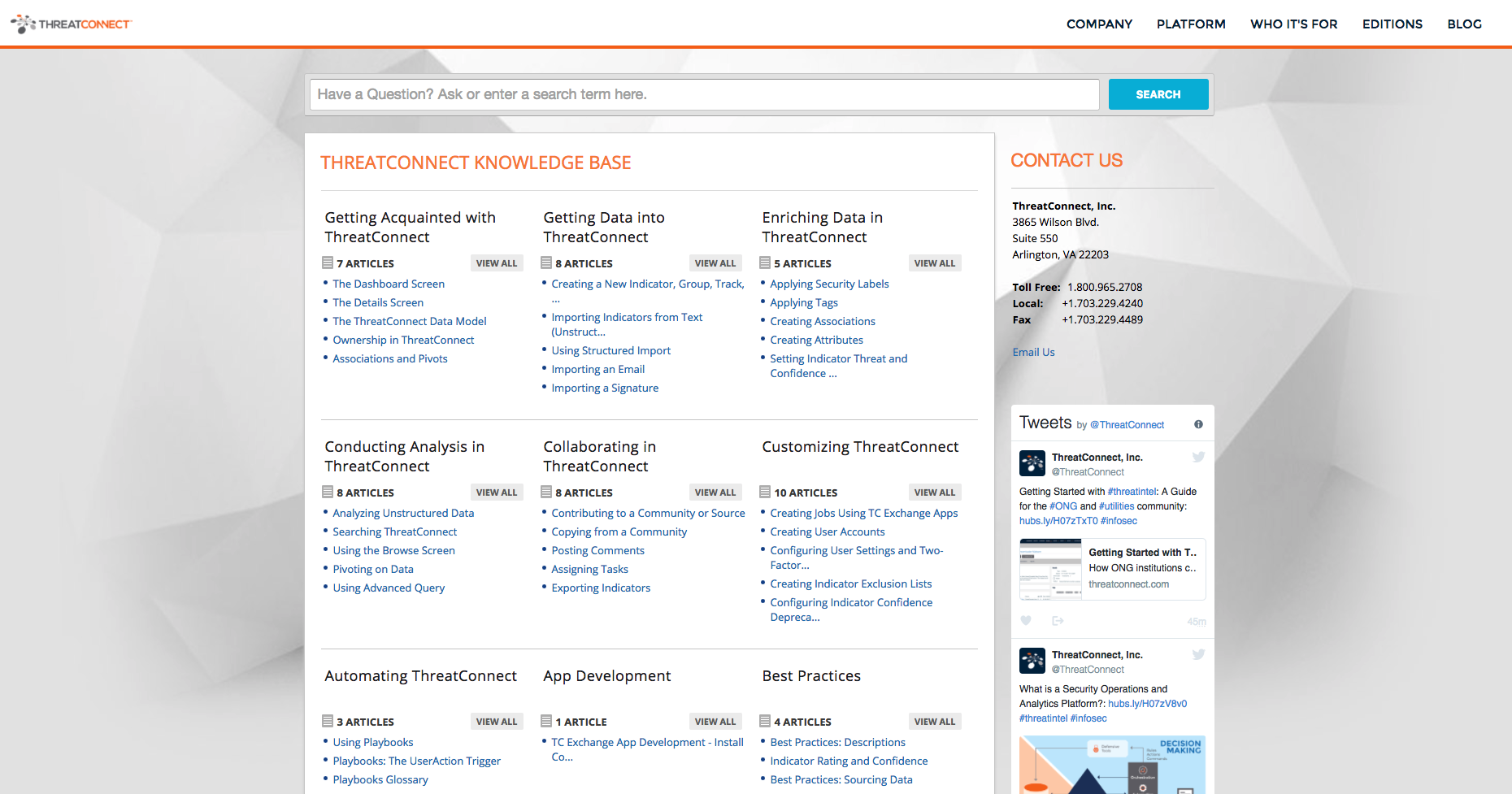
Did You Know We Have A Knowledge Base?
From guides to training videos and best practices, ThreatConnect’s Knowledge Base has everything you need to use the Platform to its fullest potential. Did you know that ThreatConnect has a knowledge base? What is a knowledge base, you ask? And why is it awesome? Read on… First, let’s define it: a knowledge base is a […]
Remembering Network Ports and Services
When systems communicate on a network they often use one or more of the available 65,536 TCP/IP ports. https://en.wikipedia.org/wiki/List_of_TCP_and_UDP_port_numbers Such service names and port numbers are used to distinguish between different communication purposes and successfully remembering the association can be the key to troubleshooting a network or security issue. Many IT professionals experience moments where they […]
When Dumpster Fires Make You WannaCry
Stepping back and taking stock of WannaCry lessons learned During the afternoon on Friday May 12th, WannaCry ransomware infections broke out at several UK National Health Service (NHS) medical facilities and Spain’s telecommunication company, Telefonica. By the early evening, the attention to WannaCry had reached a fever pitch. While kill switches for the malware were […]
Getting Started with Threat Intelligence: A Guide for the ONG Community
Getting Started with Threat Intelligence: A Guide for the ONG Community How ONG institutions can get started with ThreatConnect to gain context about threats The utilities vertical, specifically oil and gas (ONG) is a complicated one, especially when it comes to information security. Each company has multiple endpoints that they need to protect – and […]
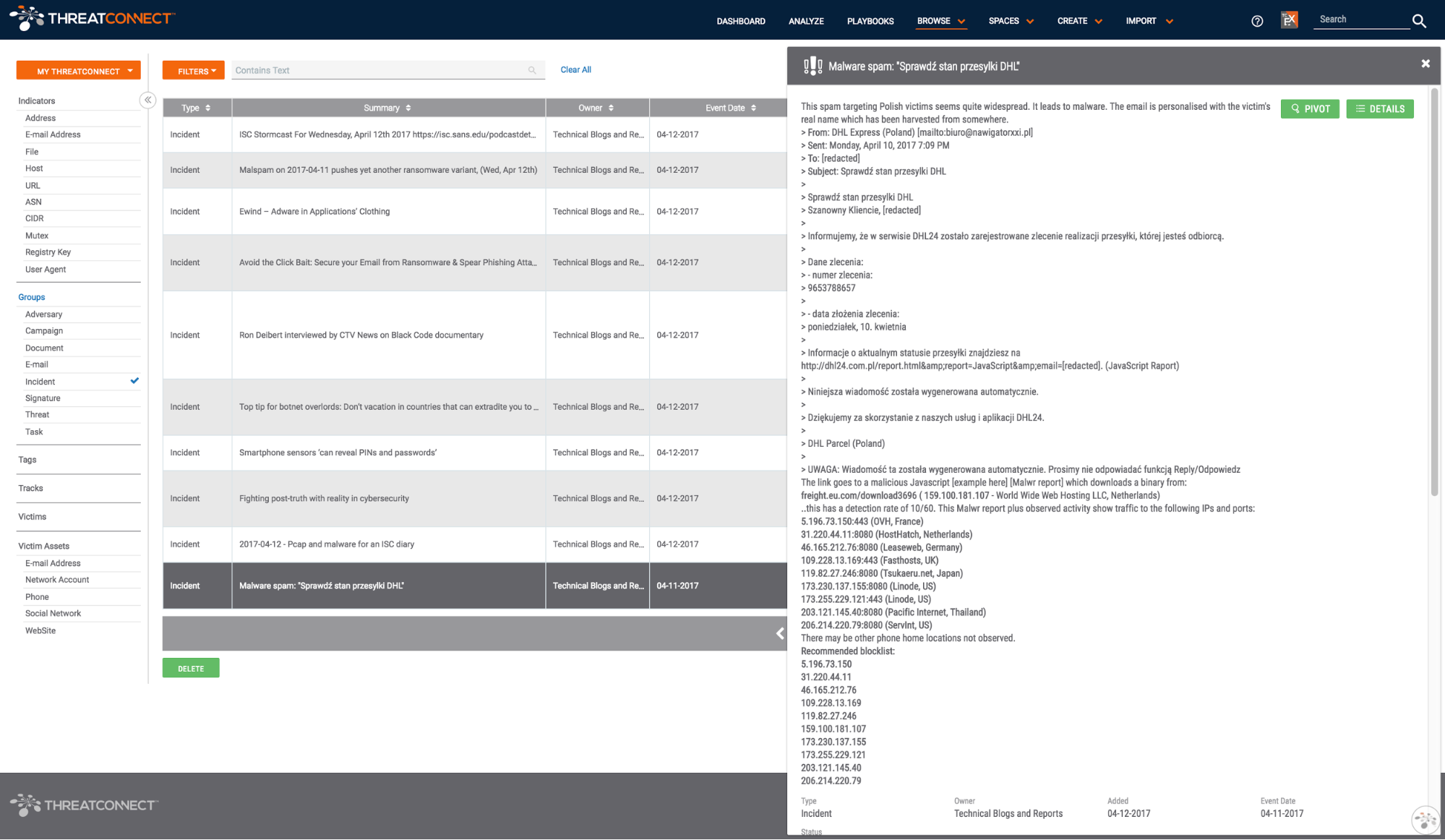
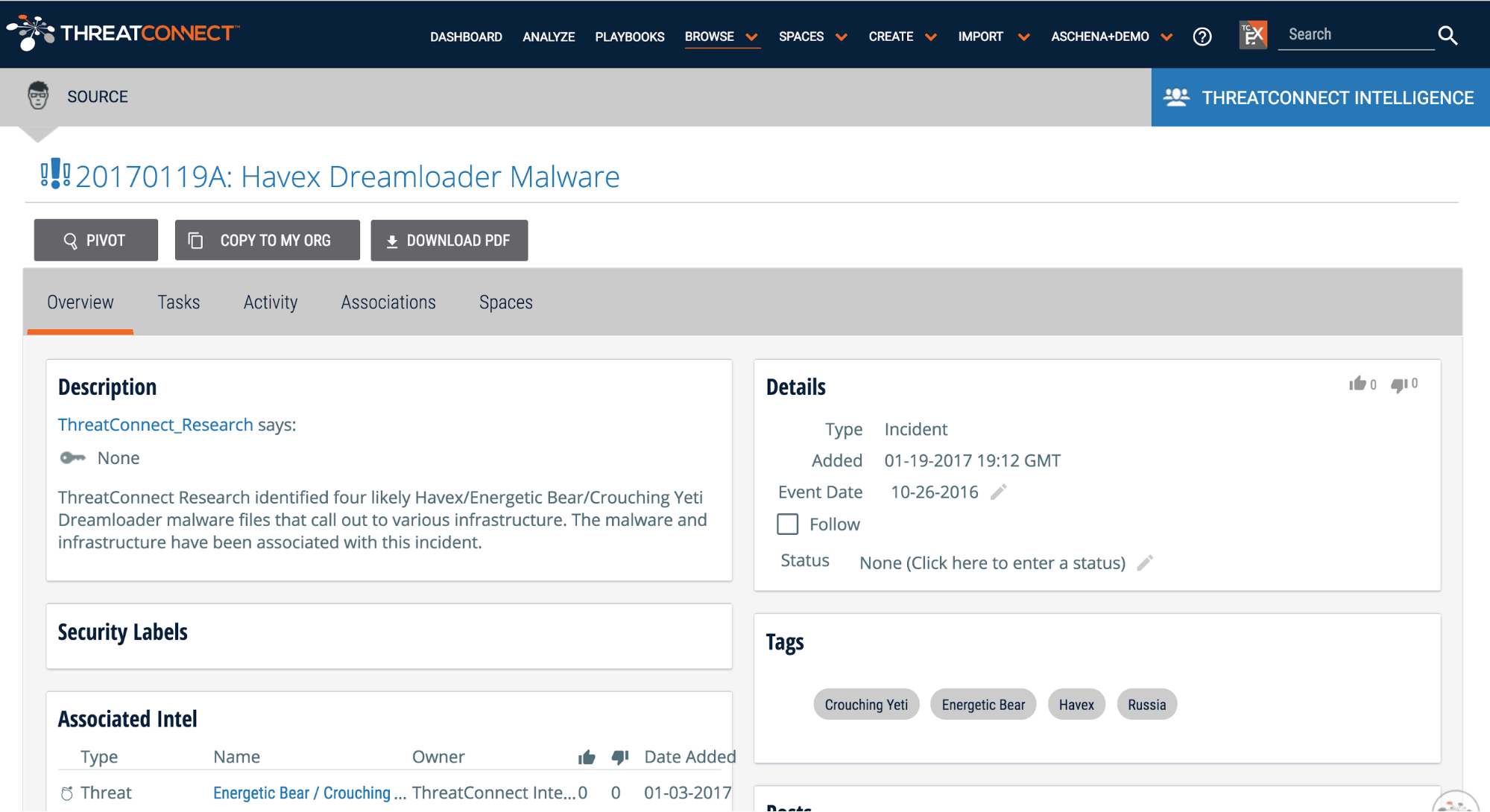
The Technical Blogs and Reports Source
I’ve got 99 problems, but keeping up with the news isn’t one Collecting is the sort of thing that creeps up on you. ~Paul Mellon “Did you see that latest report on [ransomware, ShadowBrokers, insert topic du jour here]?” Keeping up with the latest research in the field is a key task for any […]
Parlez-vous Fancy?
ThreatConnect Reviews Potential Fancy Bear Activity Targeting the French Election Runoff In the run up to the French election runoff between Emmanuel Macron and Marine Le Pen, ThreatConnect reviews intelligence suggesting domains spoofing Macron’s En-Marche.fr website are associated with Russian cyber activity. Pour lire ce blog en français, cliquez ici. In the wake of a […]
