
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
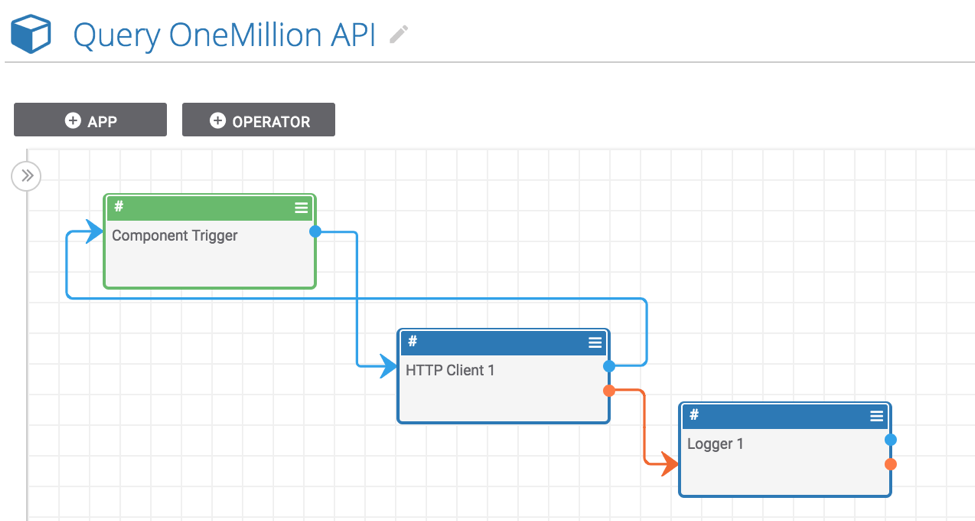
Playbook Fridays: OneMillion API Component
Using this Playbook Component, incident responders and analysts can check if a given domain exists on any lists of the most frequently visited hostnames ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis […]
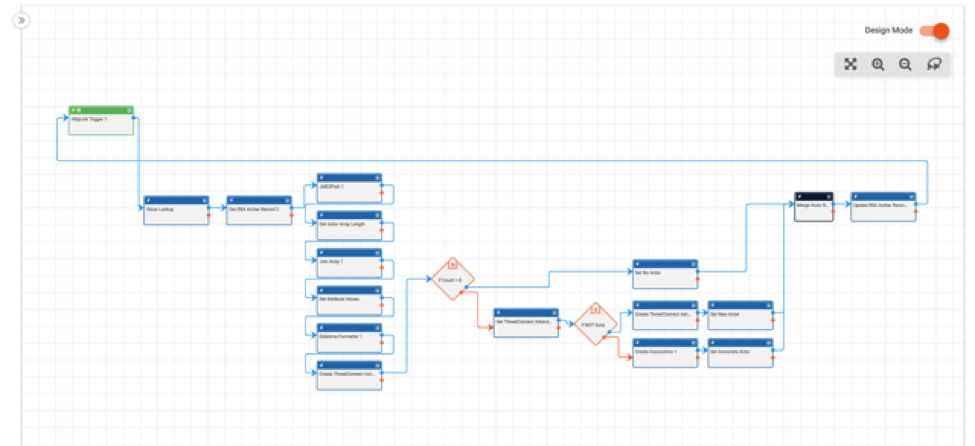
ThreatConnect’s RSA Archer Integration, Playbooks, and Apps (oh my!)
One of our top integration requests has been Playbooks for RSA Archer. Good News: we now have numerous out-of-the-box integration capabilities for connecting RSA Archer and ThreatConnect! These apps and playbooks templates allow you to perform a variety of use cases with Archer, from saving users time by automatically assigning relevant threat intelligence to cases, […]
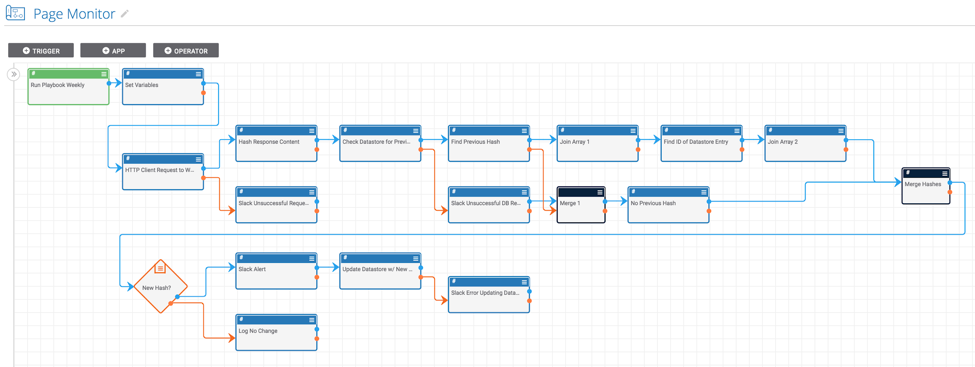
Playbook Fridays: Web Page Monitoring
Monitor a website’s content and get alerts if it changes ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human intervention. Monitoring websites for […]
Playbook Fridays: Domain Spinning Workbench Spaces App
Gain insight into possible permutations of domain names to indicate suspicious activity and further analysis For this week’s Playbook Fridays post, we’re mixing things up a little. Instead of directing you on how to set-up a specific Playbook, we’re going to help you take advantage of an App we built which is set up on […]

Polarity – VulnDB Integration
Polarity was built to be as versatile as possible, not only enabling a real-time collective memory across teammates, but also extending to any 3rd-party datasource through our integration framework. This allows analysts to get any information they need whether from internal or external sources. Our newest integration is with Risk Based Security’s VulnDB. The Polarity […]
ThreatConnect 5.7 Shows Advancements in Playbooks Capabilities
Juggling Priorities and Countless Orchestration Use Cases? We’ve Got Your Back Automation and Orchestration are terms that are thrown around interchangeably and claimed to be supported by just about every product offering out there. The advancements in technology required to truly support scalable workflows should not be understated. Remember those connect-the-dot games we used to […]
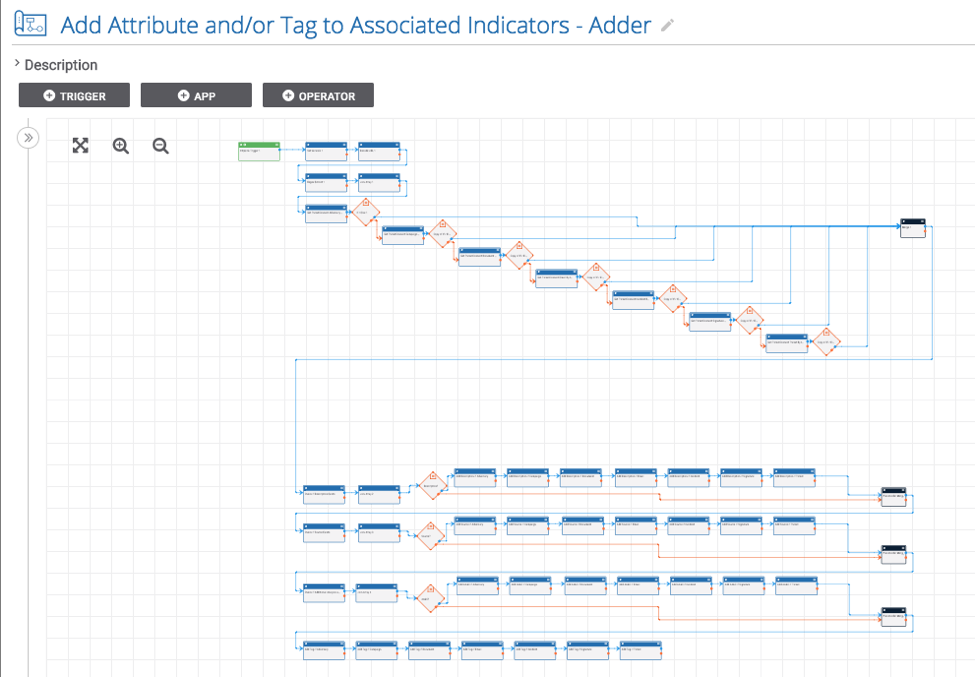
Playbook Fridays: Associated Indicator Metadata Creator
Easily add metadata (in the form of certain attributes and tags) to the all of the Indicators associated with any Group ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur […]
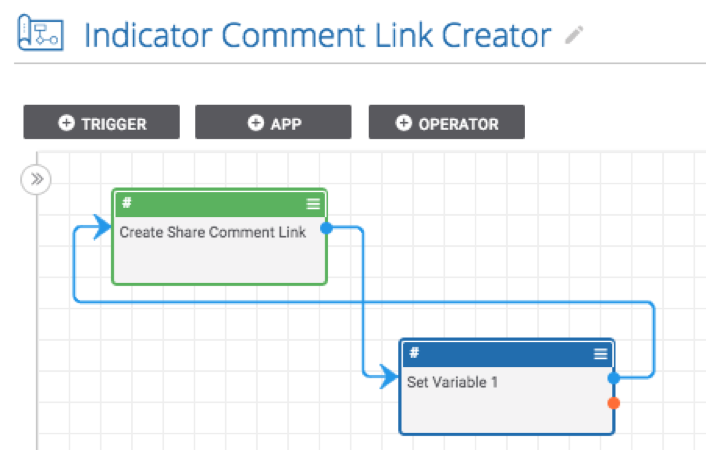
Playbook Fridays: Group and Indicator Comment Link Creators
Create and copy the link to an Indicator or Group in two clicks ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human intervention. […]
Playbook Fridays: Robtex ASN Query and Robtex IP Query
Simplify the process of pivoting through data and expanding an investigation using Robtex ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human intervention. […]
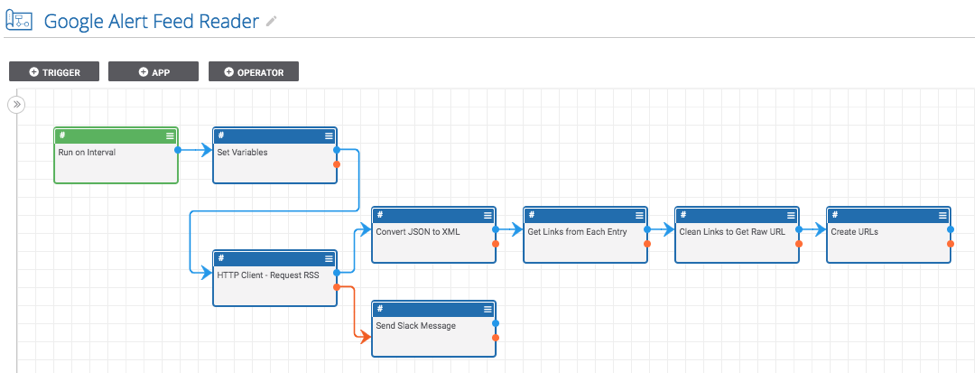
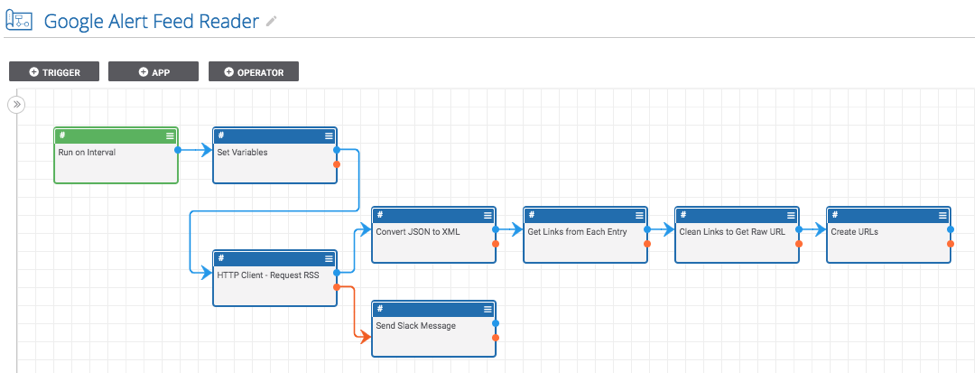
Playbook Fridays: Google Alerts RSS Reader
Read a Google Alerts RSS feed and create indicators from the links ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human intervention. Once […]
Top 5 ThreatConnect Resources for Malware Analysis
Malware Analysis. Some may say it’s the most exciting part of the job, right? You have something you know is bad. What’s it do? How’s it run? Where’d it come from? These are questions we all want to know the answers to. And because technology is a beautiful thing, we have the ability to find […]
Playbook Fridays: QRadar Tag Search in ThreatConnect
Correlate data in QRadar with intelligence in the form of Indicators in ThreatConnect ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human intervention. […]
