
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
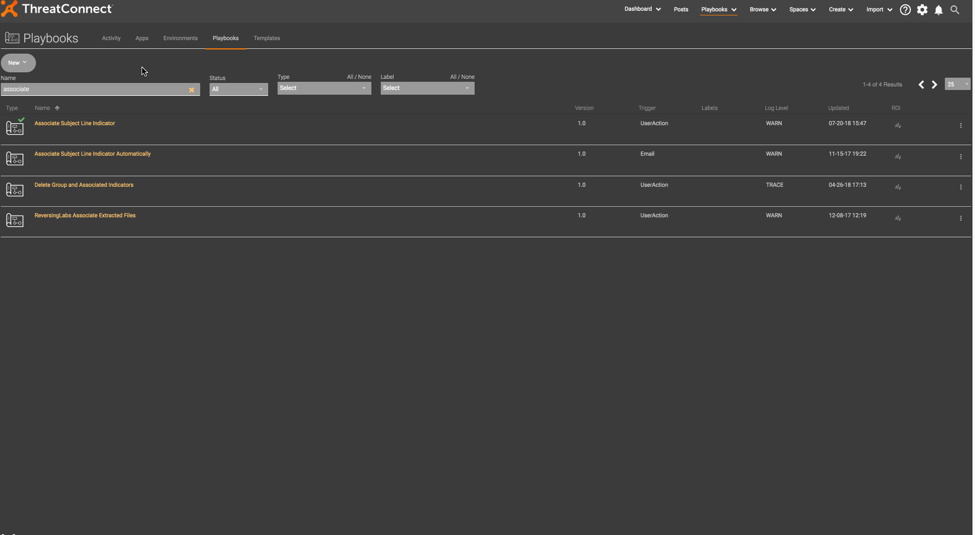
Playbook Fridays: Indicator Status Updater Playbook Component
This Friday, we introduce a Playbook Component that allows you to change the status of an Indicator. An Indicator’s status classifies the Indicator as either active or inactive. An active status indicates that the Indicator should be treated as an indicator of compromise (IOC) at the current time. An inactive status lets you keep an […]
Good News! ThreatConnect’s CAL™ (Collective Analytics Layer) 2.1 is now live!
The new and improved CAL is now active in the ThreatConnect Platform! Have you heard of CAL? Yes, you have? Awesome! No, you haven’t? Well, to quickly explain, ThreatConnect’s CAL™ (Collective Analytics Layer) provides anonymized, crowdsourced intel about your threats and indicators. It leverages the collective insight of the thousands of analysts who use ThreatConnect […]
Orchestrate Actions Based on Automating Phishing Email Analysis
Set up phishing and feed mailboxes for automated ingestion of indicators and phishing emails ThreatConnect allows users to setup phishing and feed mailboxes for automated ingestion of both indicators and phishing emails. These mailboxes can be setup to receive emails directly from network devices or receive the headers in the form of attachments. Upon ingestion […]

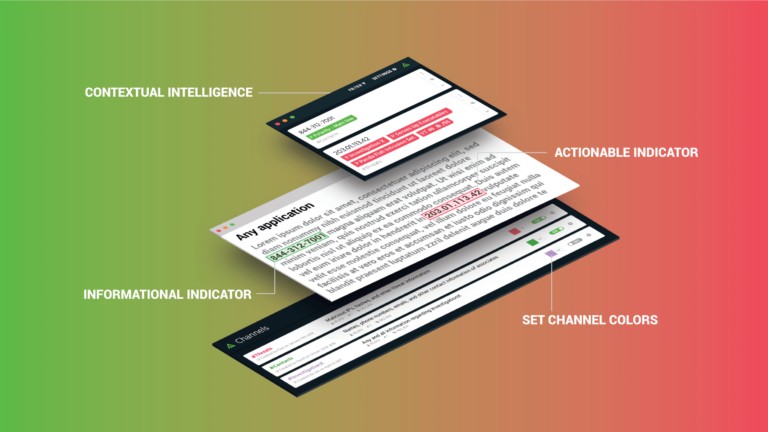
Latest Polarity Release
We are happy to announce our latest Polarity 3.1 client, Polarity Web 3.4 and Polarity 3.7 Server releases. This release includes some great new features and the official release of our Linux client. Check out the gifs below to learn more. Features in New Release Linux Client: We now support Ubuntu 16 and 18, Centos […]

May the Force (of Partnerships) Be With You
What the Rebels Taught Me About Building Alliances To say that ThreatConnect has a “thing” for Star Wars would be putting it mildly. Whether it be our office decor, the names of our conference rooms, the themes of our t-shirts, or our blog posts, everything at ThreatConnect is viewed through certain Star Wars-colored lenses. As […]
Introducing ThreatConnect’s Version 5.8
Showcasing the Platform’s increased user flexibility for creating Playbooks and expanded options for in-Platform application (App) building It’s here! Version 5.8 is here: ThreatConnect’s newest Platform features and functionality that we (humbly) think will heighten your experience. With these “ ease-of-use” updates, we’re continuing to enhance your experience when it comes to the development, design, […]
Leveraging Channels – Reference Channels versus Collaborative Channels
The past few posts have discussed how Polarity’s 3rd party integration framework operates, so today we wanted to talk more about how you can take better advantage of Polarity’s Collective Memory by utilizing our Channel Framework. What is a Polarity Channel? Channels in Polarity provide a way to organize Entities and Annotations into logical groups. […]
Playbook Fridays: Indicator Defanging
To avoid indicators of compromise becoming links to malicious content, “defang” them. If you’ve worked in the computer security industry for a while, you have probably seen a website, email, Slack message, or spreadsheet with a malicious URL, email address, or domain name that has become a link. One of the ways to avoid indicators […]
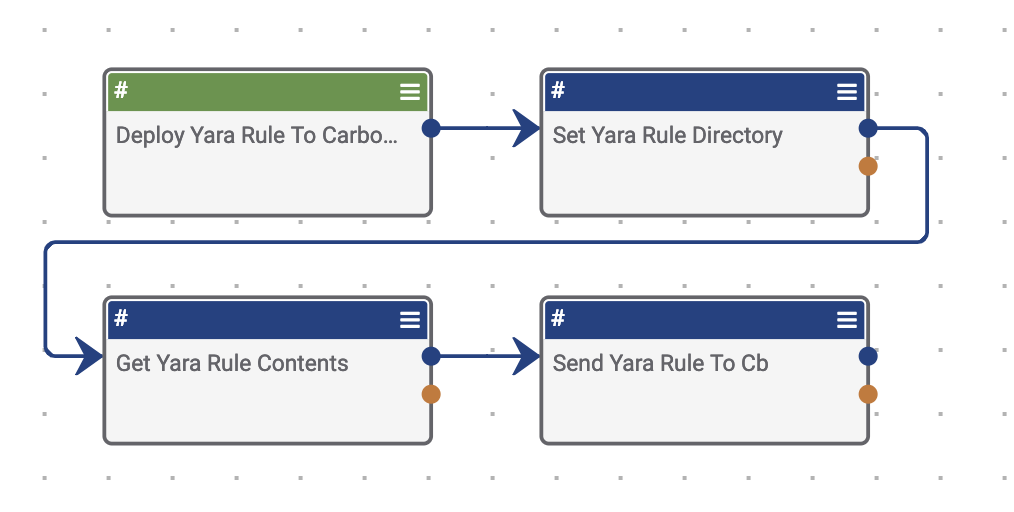
Playbook Fridays: Deploying Yara Signature to Carbon Black CB Response
Rapidly deploy Yara rules that are associated to intel products within ThreatConnect out to CarbonBlack’s CB Response via their Yara Connector This Playbook allows analysts that are performing an investigation or doing proactive threat hunting to quickly deploy signatures to Carbon Black’s CB Response. Normally this process is very manual as it requires the user […]
What Can CAL™ (Collective Analytics Layer) Do For You?
CAL™ has billions of data points that it can bring to bear to power its analytics—and we’re adding more every day It’s been two years since we announced CAL™ , our Collective Analytics Layer. Since then, we’ve made fantastic strides in leveraging some of the latest big data technology to make our users’ lives easier. […]
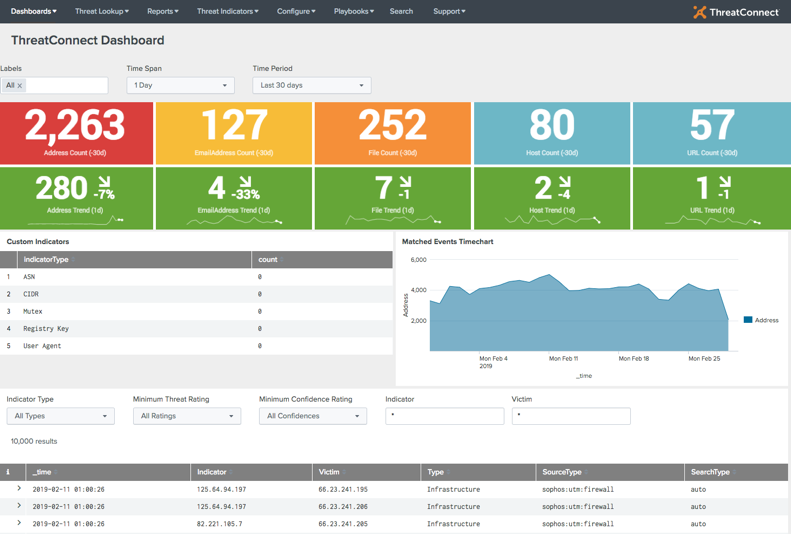
Playbook Fridays: New ThreatConnect App for Splunk 3.1
Splunk Users Can Now Launch Playbooks Directly from Splunk With ThreatConnect App Updates Earlier this week, the latest ThreatConnect App for Splunk (v3.1) was released to Splunkbase. This release for Splunk is all about taking action and enabling our customers to fully leverage the power of the ThreatConnect Platform while working directly inside Splunk or […]
Lights, Camera, Actionable Intelligence!
ThreatConnect Research builds out a network of domains and subdomains spoofing organizations related to the entertainment industry, most likely used in credential harvesting efforts. To be frank, if we were going to give out an award for this acting, we don’t know who it would go to. Following a partner tip identifying IP addresses hosting […]
