
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.

Are Critical Infrastructures Ready For The New Federal Cybersecurity Standards Initiative?
President Joe Biden signed a National Security Memorandum last week that establishes a new Industrial Control Systems Cybersecurity Initiative to develop a voluntary set of standards for the nation’s critical infrastructure owners and operators. “The primary objective of this Initiative is to defend the United States’ critical infrastructure by encouraging and facilitating deployment of technologies […]
Q&A: Joe Weiss of Applied Control Solutions on Control Systems and Cybersecurity
During a recent ThreatConnect Podcast, Joe Weiss, Managing Partner at Applied Control Solutions gave his insights and thoughts on Control Systems and Cybersecurity issues facing our nation’s critical infrastructures. Joe is an international authority on control system cybersecurity and is currently a member of the International Society of Automation Standards Committee ISA99, Industrial Automation and […]
Q&A: Bob Kolasky of the Department of Homeland Security on Systemic Cyber Risk and Critical Infrastructure
ThreatConnect Podcast host Dan Verton recently had the pleasure of speaking with Bob Kolasky, Director of the National Risk Management Center at the Cybersecurity and Infrastructure Security Agency (CISA) during a recent ThreatConnect Podcast, where he gave his insights on systemic cyber risk and critical infrastructure. There have been nearly a thousand documented and reported […]
ThreatConnect Supports MITRE ATT&CK Groups and Software
ThreatConnect now supports MITRE ATT&CK Groups and Software within our Platform! Before we dive too deep, let’s define Groups and Software in MITRE ATT&CK. What are Groups? Groups are sets of related intrusion activities tracked by a common name in the security community. Analysts follow clusters of activities using various analytic methodologies and terms such […]

ThreatConnect and Amazon GuardDuty: Protection for your AWS Environment
ThreatConnect has built 3 new Apps to work seamlessly with Amazon GuardDuty. Amazon GuardDuty is a threat detection service that continuously monitors for malicious activity and unauthorized behavior in your AWS accounts, workloads, and data stored in Amazon S3. With these Apps, any known IP addresses (good and bad) can be set up for monitoring […]
Q&A: AVEVA’s Tim Grieveson on Cyber Risk Management and Critical Infrastructure
During a recent ThreatConnect Podcast, Tim Grieveson, Chief Information Security Officer (CISO) at AVEVA, gave his insights and thoughts on cyber risk management issues facing our nation’s critical infrastructures. The recent surge in cyberattacks targeting critical infrastructure companies demonstrates the urgent need for critical infrastructure owners and operators to adopt a risk-led cybersecurity program. It […]
Q&A: Felicia Thorpe of AHT Insurance on Cyber Insurance and Cyber Risk Quantification
During a recent ThreatConnect webinar, Felicia Thorpe, Managing Advisor at AHT Insurance, offered her insights on the latest trends in the cyber insurance market and changes that need to be considered to battle the surge in ransomware attacks. The increasing sophistication and cost of cyberattacks, particularly ransomware, have led to a massive jump in demand […]

ThreatConnect and Amazon S3 and EC2: Better Manage Cloud Infrastructure
ThreatConnect has built new integrations to work with Amazon’s cloud infrastructure. With these integrations, you can more easily monitor and protect your AWS environment. Amazon Simple Storage Service (S3) is a service offered by Amazon Web Services that provides object storage through a web service interface. Amazon S3 uses the same scalable storage infrastructure that […]

Big Changes are Coming to the Cyber Insurance Industry
The surge in ransomware and other advanced cyber attacks during the last 18 months has led to significant changes in the way insurance carriers approach cyber policies and those changes are far from over. For more than two decades, insurance companies have been issuing cyber policies with little to no verification of a client’s cybersecurity […]
Risk-Threat-Response: The Rosetta Stone for Communicating Cyber Risk
Many security leaders struggle with communicating cyber risk in business and operational terms that matter to C-suite executives and boards of directors. This miscommunication is one of the biggest hurdles faced by many security leaders. Security leaders need a way to translate cyber risk into terms that business executives can understand. When both security and […]
Introducing Playbooks 2.0 and Intelligence Anywhere: Creating a Foundation of Collaboration with ThreatConnect 6.2
ThreatConnect 6.2 introduces Intelligence Anywhere and Playbooks 2.0 for improved ease of use and collaboration. When we think of “collaboration” we usually think about groups of people working together, maybe from different teams, to achieve a common goal. In cybersecurity, that may mean the threat intelligence team provides much-needed context to the SOC, or the […]
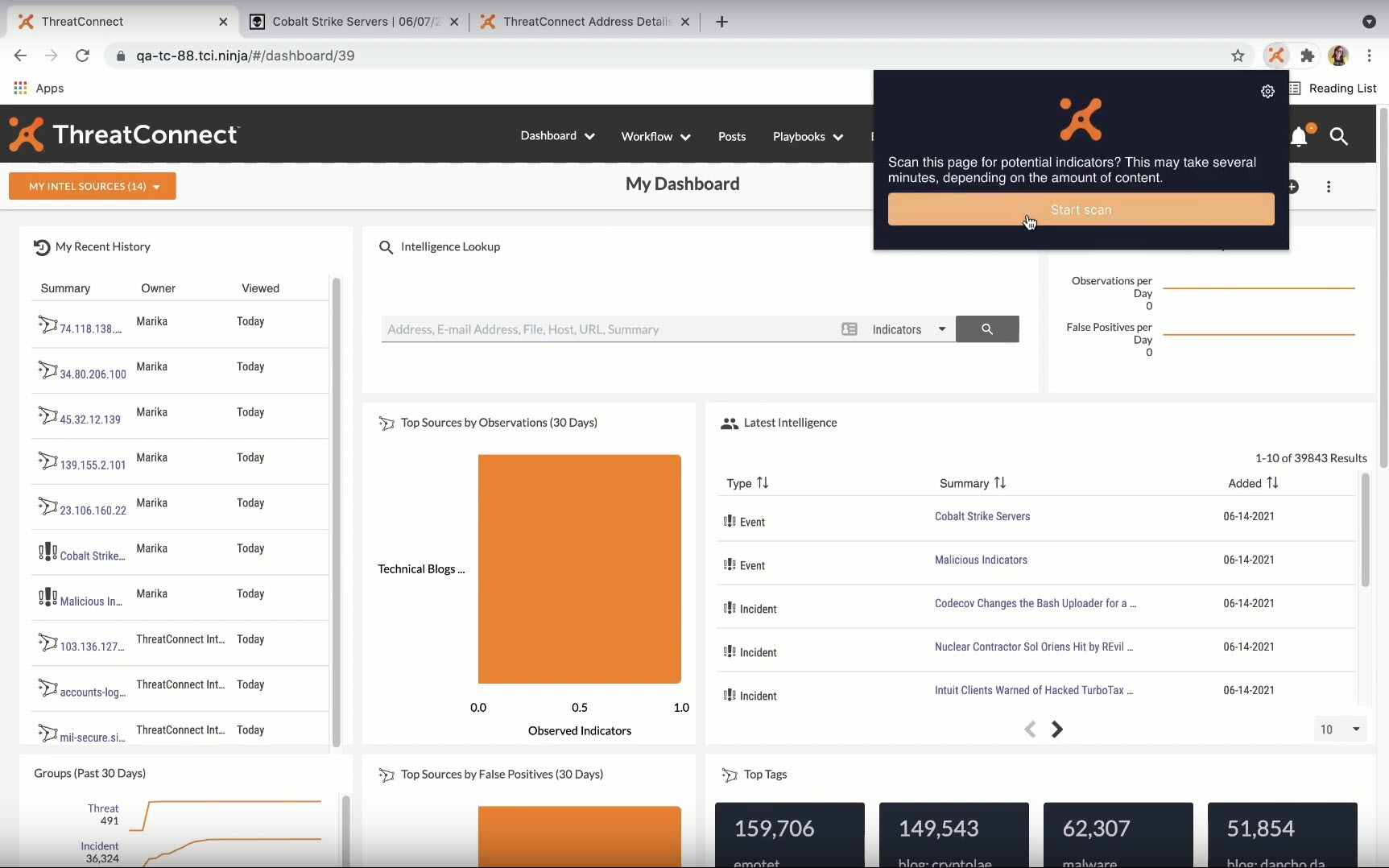
Introducing Playbooks 2.0 and Browser Extension: Creating a Foundation of Collaboration with ThreatConnect 6.2
ThreatConnect 6.2 introduces a new Browser Extension and Playbooks 2.0 for improved ease of use and collaboration. When we think of “collaboration” we usually think about groups of people working together, maybe from different teams, to achieve a common goal. In cybersecurity, that may mean the threat intelligence team provides much-needed context to the SOC, […]
