Posted
CTI analysts encounter numerous challenges in handling the constant influx of data from various unstructured open-source intel (OSINT) sources, such as reports and blogs, news sites, and other websites. ThreatConnect’s CAL Automated Threat Library (ATL) efficiently distills over 60 definitive OSINT sources into a structured and ready-to-use threat intel feed.
CAL: Real-Time Insights and Global Intelligence
In our last blog, we explored the source of power – the brain, if you will – of ThreatConnect’s TI Ops Platform—ThreatConnect CAL. CAL is a comprehensive solution from ThreatConnect, utilizing AI and ML-powered analytics to offer real-time insights and context into threats and their behaviors. This includes automated ATT&CK analysis, unique feeds specific to ThreatConnect, and the collective intelligence shared among ThreatConnect users.
With a little grounding in CAL’s overall scope and power, let’s now focus on the Automated Threat Library (ATL) within CAL.
CAL ATL: Simplifying OSINT Handling
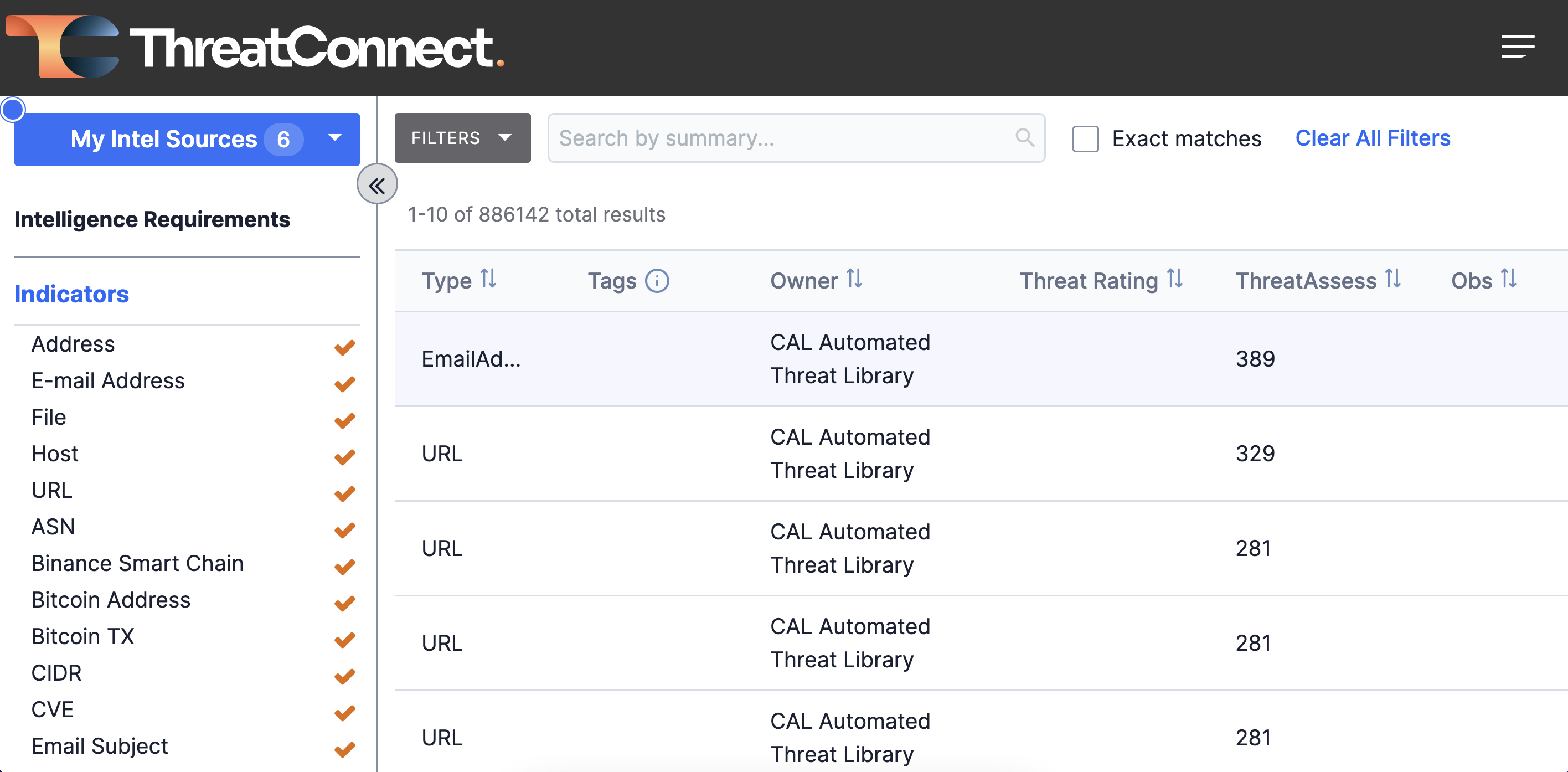
The Automated Threat Library (ATL) plays a crucial role in simplifying the handling of unstructured OSINT. By distilling information from diverse sources into a structured format, CAL ATL automates the heavy lifting required by analysts. This saves valuable time and enhances the efficiency of threat intelligence operations.
Once identified by ATL, IOCs are seamlessly integrated and enriched with relevant information, such as Classifiers, MITRE ATT&CK tactics and techniques, and Domain Generation Algorithms discovered through Machine Learning. ThreatAssess scores and Classifiers further aid teams in focusing on the most critical intelligence.
Easy to Read and Digest
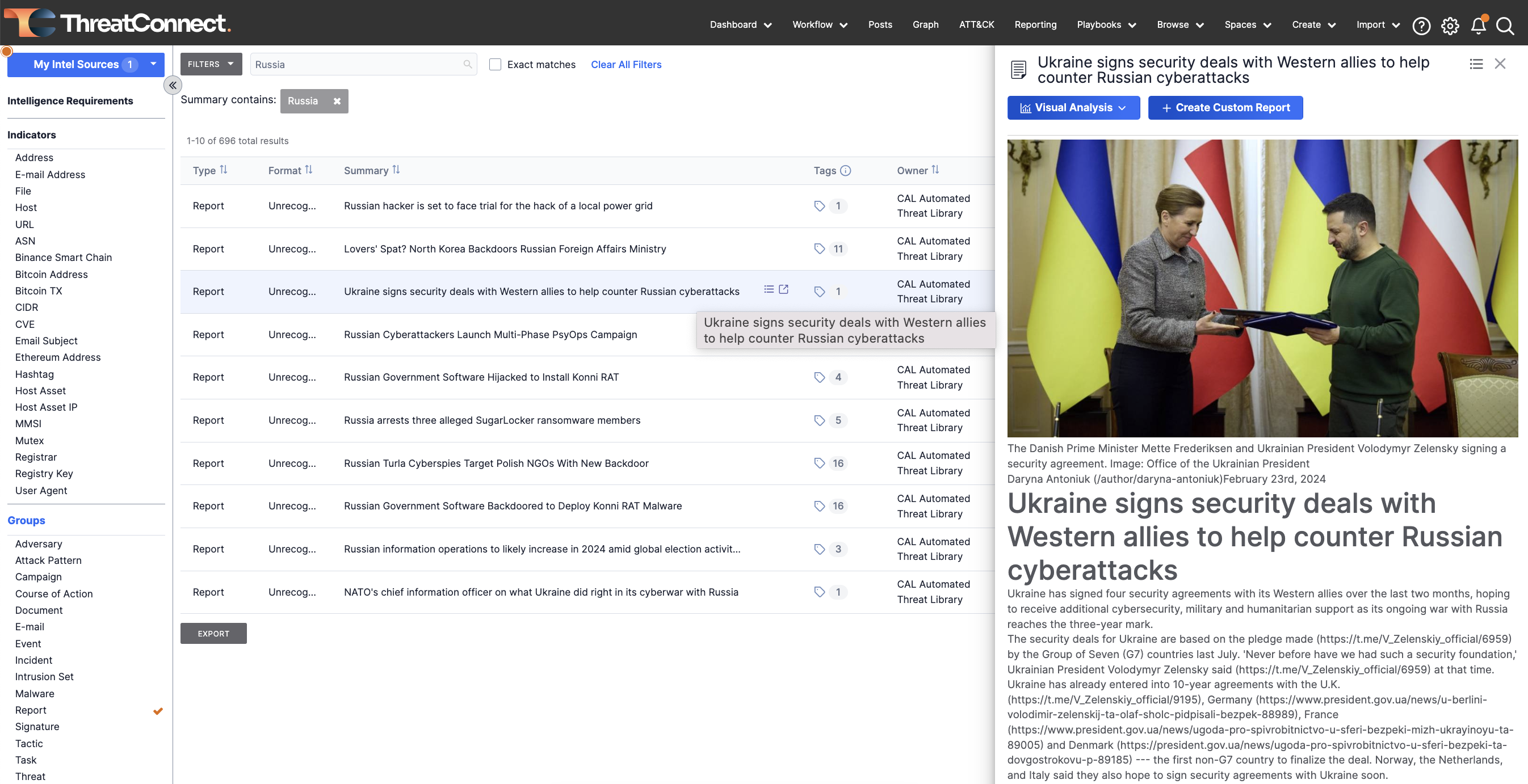
All of CAL ATL is assembled in one feed that is easy to search and consume. CAL ATL automatically tags intelligence with known aliases for mentioned groups, such as threat actors, malware, etc. CAL ATL users can also select CAL Alias Information or combine group nodes by alias to provide a better understanding of which objects are related to a given Group. This saves time for analysts so they don’t have to manually deduplicate all the threat actor group names.
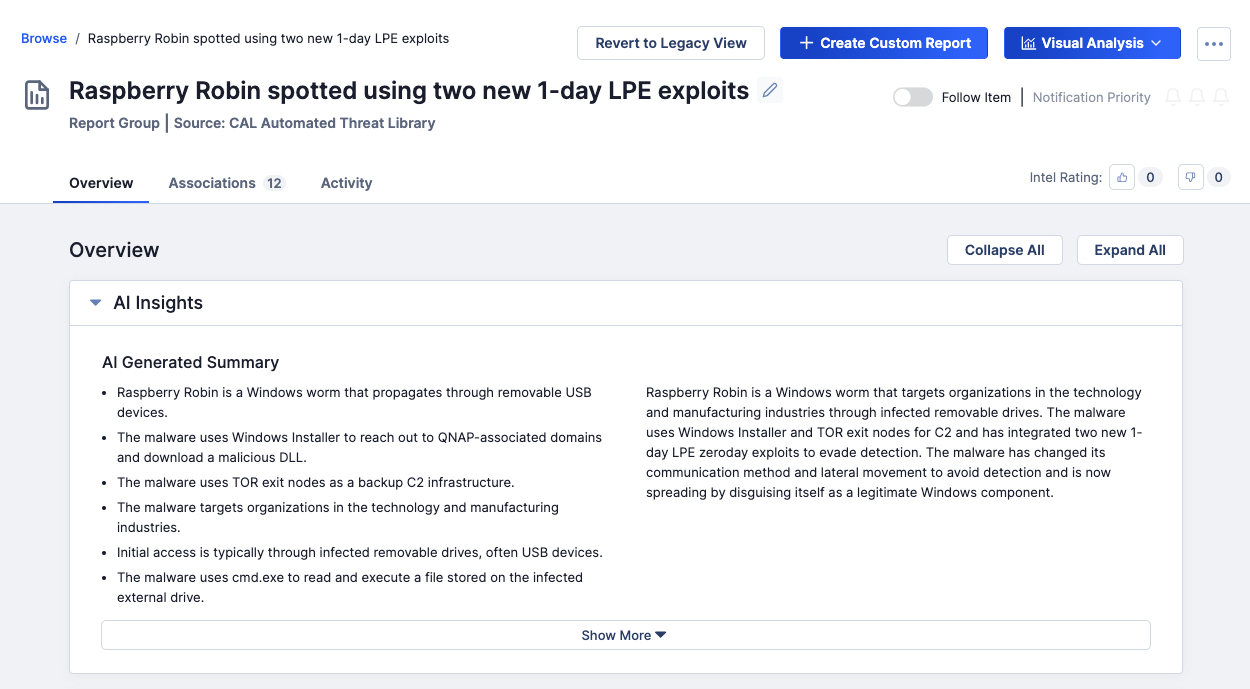
AI Insights: Elevating Report Understanding
CAL ATL provides an AI-Generated summary card prominently displayed at the top of the Report Group’s overview page. This summary consists of brief, easy-to-read bullet points, providing users with a high-level understanding of the report’s contents. This empowers users to efficiently decide whether a report warrants further attention or analysis, optimizing their workflow and ensuring a more focused and informed approach to threat intelligence.
Strategic Intelligence Source
CAL ATL is a strategic intelligence source. By incorporating an organization’s intel requirements in the TI Ops Platform’s Intelligence Requirements feature, analysts can quickly provide intel to help decision-makers answer critical questions and stay informed about emerging threats. The structured threat intel feed allows for efficient communication and informed strategies.
Benefits of CAL ATL
The practical approach of CAL ATL offers a robust, accurate, and actionable solution to the challenges of handling high volumes and varieties of OSINT. By staying abreast of the latest threats, improving analyst operational efficiency, and facilitating faster, informed decision-making, CAL ATL becomes an essential tool in the cybersecurity arsenal.
For more details, please tour the ThreatConnect TI Ops and reach out to sales@threatconnect.com or request a demo to learn more about how ThreatConnect can help you operationalize your threat intel program.

