No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.
Customer Story: Large Enterprise Needed Centralized Threat Intelligence Management
Company Type: Software Provider Industry: Technology Company Size: 130,000+ Employees Challenge This large technology client was looking for a centralized repository of contextualized threat intelligence, from which humans and machines can get a unified view to derive associations, prioritize, and collaborate on observations. The solution needed to be able to collect, normalize, and disseminate data […]

Need a Polarity refresher? Watch this 5 minute video.
Polarity is a cutting-edge data fusion platform designed to streamline workflows, enhance decision-making, and improve visibility across your organization. By unifying both internal and external data sources into a single platform, Polarity eliminates blind spots and reduces time wasted switching between tools. With seamless integration across 180+ systems—including custom-built solutions—Polarity offers features like automated searches, […]

A Guided Quickstart of Polarity
Watch our Quickstart onboarding video with Joe Rivela to master Polarity’s features. Learn seamless installation, powerful integrations, and boost your efficiency and decision-making.
Polarity Use Cases: MSSP & MDR
Enhance your MSSP and MDR operations with Polarity. Boost efficiency, reduce false positives, and accelerate threat analysis.

Working in the SOC with Power Tools
Watch our Quickstart onboarding video with Joe Rivela to master Polarity’s features. Learn seamless installation, powerful integrations, and boost your efficiency and decision-making.
Smarter Security and Maximum Impact from Intelligence-Powered Security Operations
Download our whitepaper to learn why operationalizing threat intelligence is critical to preparing teams to face the challenges of today and tomorrow.

ThreatConnect For Threat Intel Analysts
As a cyber threat intel (CTI) analyst, you’re tasked with aggregating and analyzing multiple data sources to turn into actionable intelligence but getting high-fidelity intel in the hands of the right people, and into the right tools, at the right time can be a challenge. With ThreatConnect, automate tasks and easily access data so you […]
ThreatConnect For Security Leadership
The ThreatConnect Platform gives security leaders a single pane of glass to easily visualize data that shows the impact of your security teams’ efforts and gain a better understanding of the threats your organization faces. The ThreatConnect Platform infuses threat and risk intelligence across security and the business for a modern security operations center. ThreatConnect’s […]
ThreatConnect For Incident Response
ThreatConnect for Incident Response drives quicker response times with native case management capabilities and relevant intelligence at your fingertips. Make your security teams and your security tools and tech work better together, faster, and more efficiently to make the greatest impact with ThreatConnect Playbooks and set up workflows to support countless use cases. The ThreatConnect […]
ThreatConnect For Security Operations
Security operations teams need to be efficient, responding to relevant threats fast, but without the right information and context about an alert, it’s difficult to know what to prioritize and how to respond. With the ThreatConnect Platform, you’re able to centralize your intelligence and automate tasks, processes, and playbooks to make teams more efficient, consistent, […]
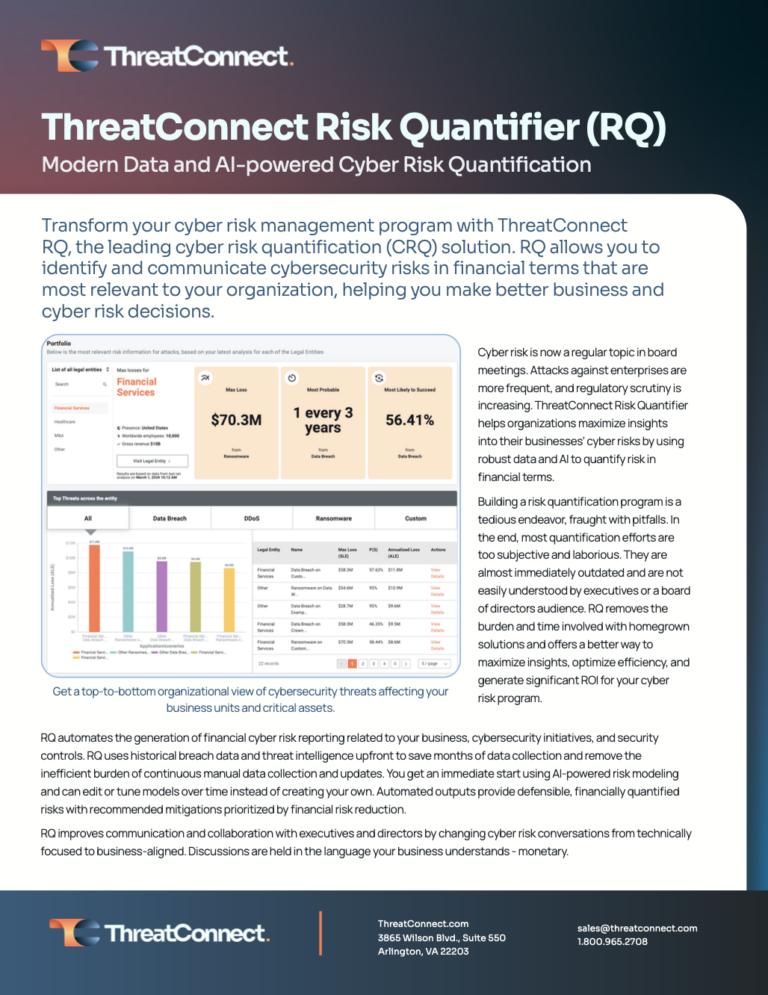
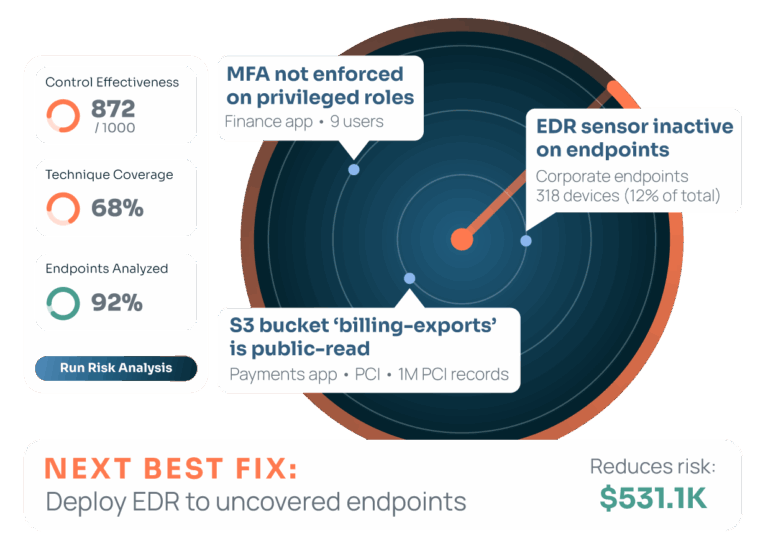
ThreatConnect Risk Quantifier
Cyber Risk Quantification (CRQ) is a critical part of cybersecurity that will fundamentally change the way security works and how risk is communicated to business stakeholders. CRQ technology gives security teams the tools to translate cybersecurity into financial risk and business impact, which allows for proactive cyber defense and data-driven decision-making across the board. ThreatConnect […]

Phishing with ThreatConnect
Phishing attacks are at an all time high. There were over 1 million attacks just in Q1 of this year! These attacks are getting more sophisticated and morphing into more clever ways to entice end users to click on those links. Security analysts are overwhelmed by the intricacies of hidden details in email messages, headers, […]