Posted
Today, we’re launching version 7.2 of the ThreatConnect TI Ops Platform. It’s an exciting day because, with this release, we’re giving a massive upgrade to our customers with some fantastic new features and capabilities.
Our latest features now include ATT&CK Visualizer, ThreatConnect’s native ATT&CK navigator, and Tag Normalization and Management.
ATT&CK Visualizer will enable Threat Intelligence Analysts to:
- Visualize tactics, techniques, and sub-techniques used by each Group in the MITRE ATT&CK Framework.
- Present useful details on each technique and sub techniques.
- Insights into Groups using similar techniques and sub-techniques.
Our improved Tag Normalization and Management feature:
- Reduces the number of custom and redundant tags in the current system.
- Reduces confusion.
- Increases efficiency.
These new features make the collection and processing of data more expedient and cost-effective.
ATT&CK Visualizer
We are excited to announce ATT&CK Visualizer. Threat Intelligence Analysts, SOC and Security Ops Analysts, Incident Responders, Pen Testers, and Red Teams, can now leverage the MITRE ATT&CK Framework, like never before to anticipate, prevent, and respond to attacks.
ThreatConnect’s ATT&CK Visualizer enables threat intelligence analysts to visualize existing attacker tactics, techniques, and sub-techniques in order to identify adversarial behaviors for planning and organizing defenses. In this release, customers can now visualize the TTPs employed by Threat Actors and identify other groups that utilize the same techniques and sub-techniques. By doing so, customers can expedite their investigations and implement security controls for widely employed techniques. In future releases, customers will benefit from security control gap identification, defense prioritization, and collaboration with internal and external teams.
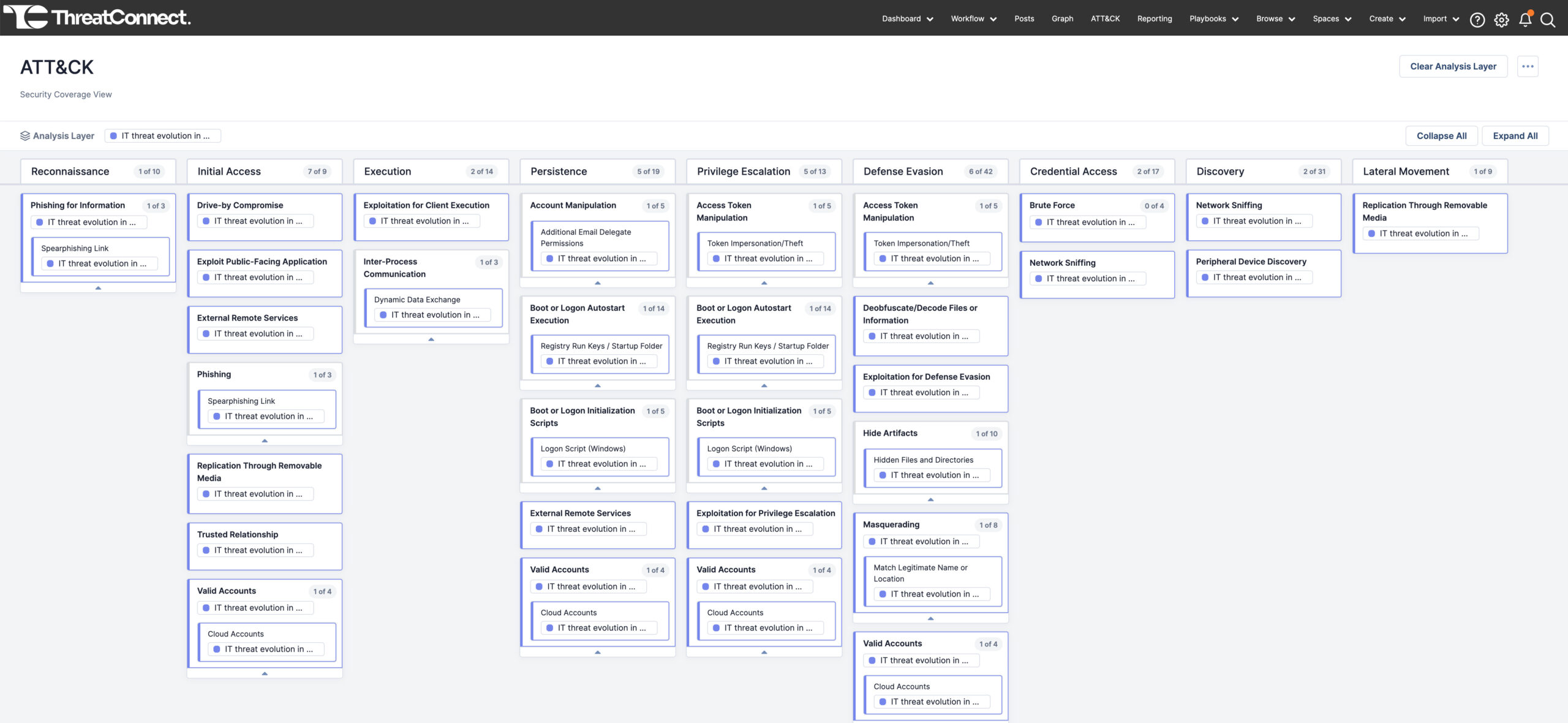
Visualizer extends upon the current support for ATT&CK in the ThreatConnect Platform by enabling customers to visualize existing TTPs, but also the latest and most sophisticated real-world attack campaigns. This provides organizations with a common language when referring to adversarial behaviors, enhancing their ability to plan and organize defenses against common adversary techniques. Security teams can quickly gather the right evidence for detecting future attacks and take necessary actions to prevent threat progression.
Explore ATT&CK Visualizer in our interactive demo
Tag Normalization and Management
ThreatConnect is also proud to announce Tag Normalization and Management. We are excited to introduce this as it allows for more efficient creation and application of custom tags.
Through Tag Normalization and Management, users can define their own main tags and establish 1-to-1, user-editable tag mapping. This enables the auto-conversion of tags so that if a user creates a new tag that has already been defined, that new tag will automatically convert to the appropriate tag, making tag management simpler and more streamlined.
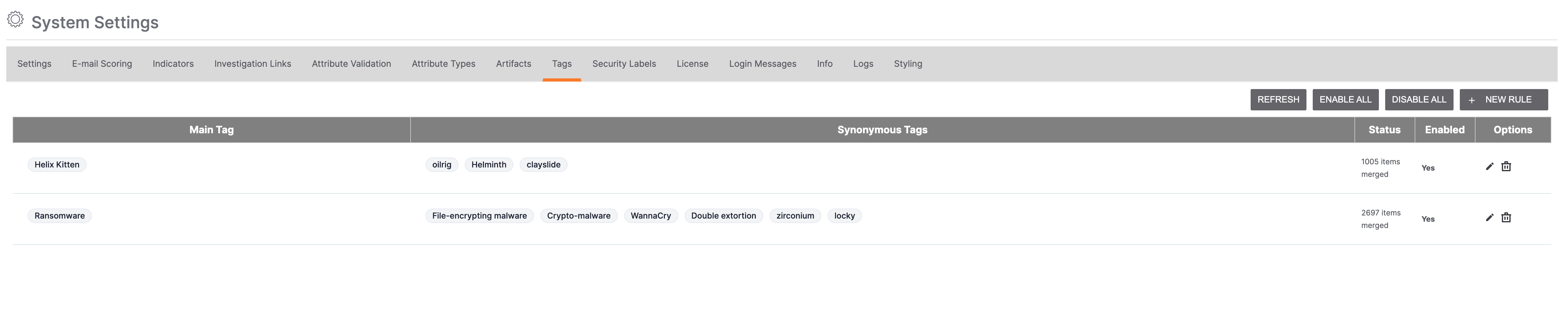
Administrators can also create custom rules for converting different synonymous tags to their corresponding main tags, auto-correct synonymous tags, and enable bulk and individual rule management capabilities. Say goodbye to tag inconsistencies, tedious manual work, or complex playbooks, and ensure a more standardized tag structure!
Explore Tag Normalization and Management in our interactive demo
Additional Enhancements
But wait, there’s more! Beyond the awesome features mentioned above, we have also included an array of enhancements, empowering analysts to conquer their tasks with unparalleled speed and effortless efficiency.
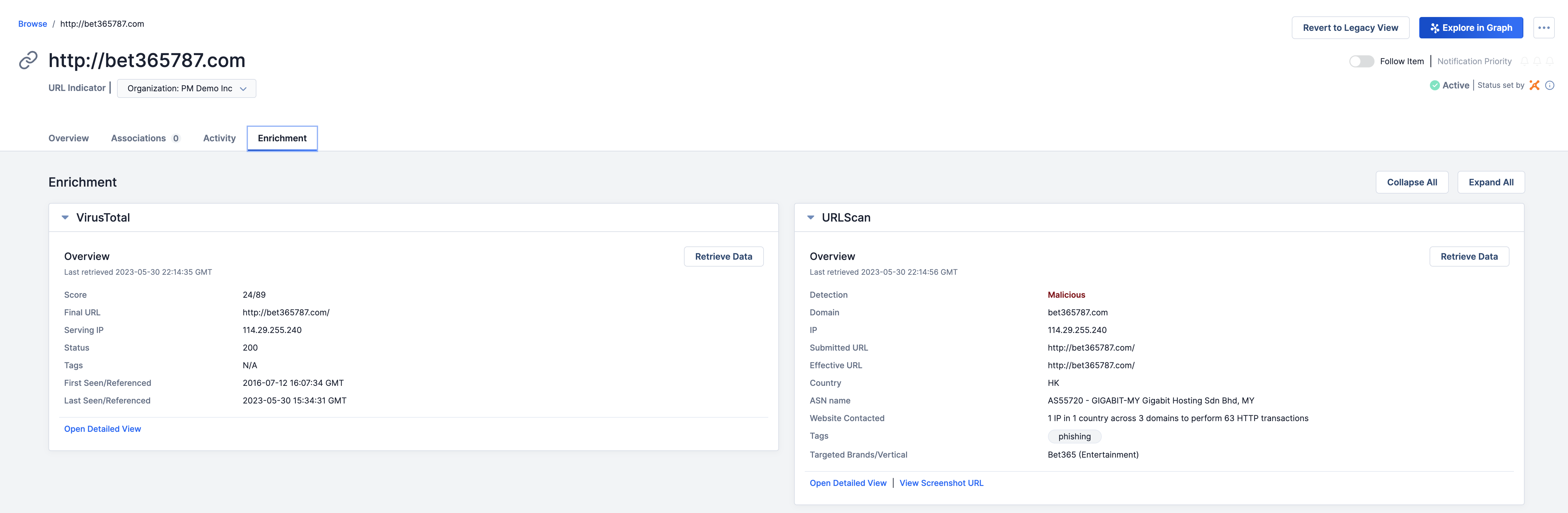
Built-in Enrichment – Urlscan.io
We continue to improve the experience of our customers by providing consolidated views for Indicator (IOC) enrichment. With the 7.2 release, some of the new benefits are:
- Native support for URLscan.io directly in the Platform.
- A comprehensive overview of URL indicators with vital information such as detection verdict, domain, associated IP, submitted and effective URL, contacted website, tags, and targeting brands/verticals.
- API Support for deeper investigation and analysis of URL indicators.
- Screenshots of URLs under investigation for enhanced visual context.
Explore Built-in Enrichment – Urlscan.io in our interactive demo
Details Page Updates
We are also excited to announce several updates to our new Details UI. Here’s what you can expect from this exciting enhancement:
- Enhanced Details UI will now accommodate Reports and Documents as additional Group types.
- UI for Report and Document objects will maintain consistency with the new Details view available for other group objects in version 7.0 and later.
- Version 7.1’s TQL-Auto Associate capabilities will seamlessly integrate within the new Details View for both Report and Document objects.
We will actively gather user feedback and continue iterating on the new Details view to ensure optimal usability and satisfaction.
Reporting Improvements
Updates to our native Reporting capability will provide greater flexibility in creating reports, enabling teams to share precise and impactful information. Version 7.0 introduced report building from Groups, while 7.1 introduced Multi Group and Case support.
Key updates in release 7.2 include:
- Distribution via email is now available.
- Conversion of intel and case data into readable reports, such as PDFs.
- New customization options include rich text contextualization and add aggregate data, i.e., bar graphs.
- Quickly and easily share reports with intel consumers and customers on an ad hoc basis.
For more information on these new capabilities and how ThreatConnect can help your organization operationalize threat intelligence, please reach out to sales@threatconnect.com or request a demo.