
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
Introducing ThreatConnect’s Intel Report Cards
Providing insight into how certain feeds are performing within ThreatConnect As part of our latest release, we’ve introduced a new feature to help users better understand the intelligence they’re pumping into their systems. Intelligence can be a fickle thing; indicators are by their very nature ephemeral and part of our job is to better curate […]
Introducing the Polarity Heads-Up-Display
What is a Heads-Up-Display (HUD)? A Heads-Up-Display, HUD for short, is a visual indicator that presents data to a person without having them look away from their usual viewpoints. A HUD was originally associated with a fighter pilot being able to see information in a heads-up position while looking forward, flying an aircraft. Different HUDs […]
The Power and Responsibility of Customer Data and Analytics
How ThreatConnect stores, uses, and protects customer data There has been a lot of recent news surrounding compromises in trust where companies purposefully or unintentionally misuse or allow others to misuse customer data. After my last post, in which I talked about the power of data and analytics, I thought it would a good time […]
Don’t Get Caught Up in the Hype of AI for Security
Don’t get caught up in the hype of artificial intelligence or machine learning. Does the product correlate and analyze alerts? When Nails are Exciting, Everyone Wants to Talk about Hammers… Sticking with the tool theme from my last post, data is ushering in “better” products in every industry, but why are we so enamored with […]

Annotating & Building a Collective Memory
What if you could build a collective memory across your team and teams that all your analysts could seamlessly benefit from? At Polarity, we post a lot about integrations and the extensibility of our Memory Augmentation Platform, but most customers have observed that building the collective memory across the team is even more valuable. One […]

A Song of Intel and Fancy
A case study tracking adversary infrastructure through SSL certificate use featuring Fancy Bear/APT28/Sofacy. A long time ago, in a galaxy… No. Stop. We’re not doing that anymore. Instead, we’re pivoting to Game of Thrones, or A Song of Ice and Fire for you bookworms, because the fantastical realm provides great material we can relate to […]
Polarity – Open Source Intelligence Integrations
If you use open source threat intelligence platforms, we have two integrations you’re going to love. Polarity recently developed open-source integrations with AlienVault’s Open Threat Exchange (OTX), and Shodan! Yes, you read that right. We’re launching two integrations back-to-back. By integrating with these open source products, we are enabling threat analysts to take full advantage […]
Query a Host or URL Indicator in Archive.org’s Wayback Machine
One-Click querying of the Wayback Machine See if a website has been archived in the Wayback Machine ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real […]
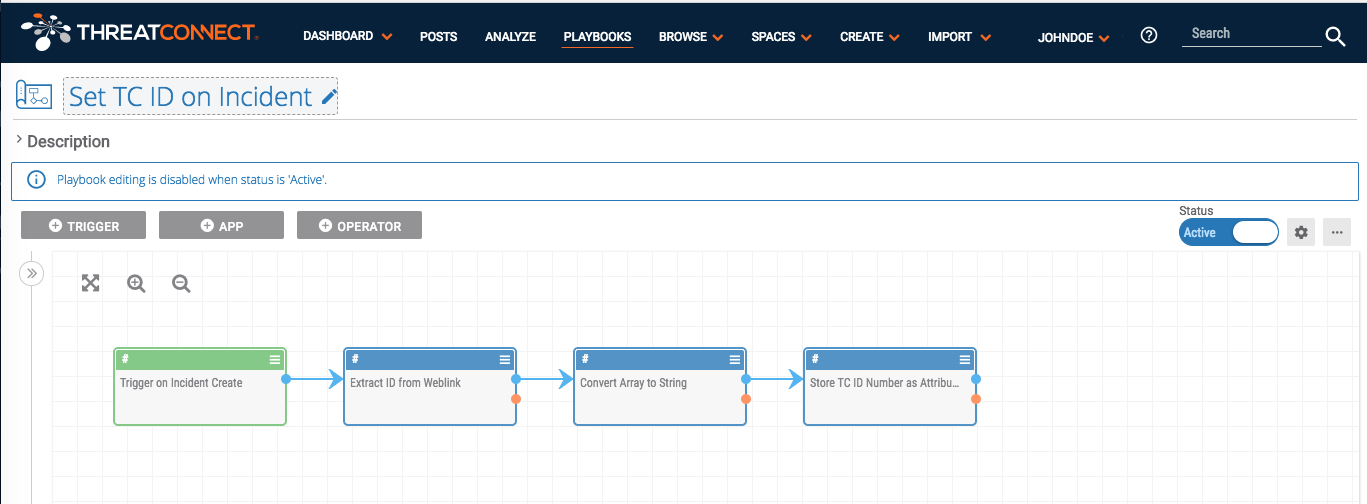
Playbook Fridays: Using Playbooks to populate custom attributes
Create Custom Attribute Types and Validation Rules, then use Playbooks to populate them automatically I was working with a customer who wanted to use ThreatConnect’s Task and workflow features like a traditional ticketing system, with a unique identifier for data objects that they could key off of and pass to other teams as needed. This […]
Duping Doping Domains
Possible Fancy Bear Domains Spoofing Anti-Doping and Olympic Organizations Update – 1/19/18 We recently identified two additional domains — login-ukad[.]org[.]uk and adfs-ukad[.]org[.]uk — which appear to spoof UK Anti-Doping. The domain login-ukad.org.uk uses the Domains4Bitcoins name server previously mentioned and, as of January 19 2018, is hosted on dedicated server at the IP 185.189.112[.]191. This […]
Please Do Not Feed the Phish
How to Avoid Phishing Attacks We’ve all heard the phishing attack stories that start with someone receiving an email that requests an urgent invoice review or password change, and ends with a data breach where personal information is compromised and money is lost. Although many of us may roll our eyes at the possibility of […]
Playbook Fridays: Task Management
Playbook Fridays: Task Management Simulate a task in ThreatConnect which can be modified to recur daily, weekly, or monthly ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and […]
