
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
Polarity User Tips: IP Social Distancing
In the opening act of 2020, we’re busier than ever. Building on 2019’s Productivity: Part I, we want to introduce 4 additional productivity hacks to give you back even more of your time this year. Give these tips a read and take the opportunity to implement some new habits – you might be surprised by the […]

The hardest part of remote work – and how to tackle it – Part II
Those of us who can address the inherent challenges of remote work can thrive despite them. By implementing some simple tactics, we can learn to be high-performers as well as satisfied employees in a remote setting. To build on Part I, here are some tactics to address the challenges of remote work from the organizational level. […]

The hardest part of remote work – and how to tackle it – Part I
It’s safe to say that the honeymoon phase of remote work is coming to a close. With more and more teams fully dispersing, the stock photo fantasy of reclining on a white sand beach, laptop and piña colada in hand, has started to dissipate as the reality of remote work comes into wider recognition. Sure, there […]
Introducing ThreatConnect’s New Learning Portal
New courses and our knowledge base are combined in one place We are very excited to introduce our new Learning Portal! Accessible to all of our registered users, this portal not only houses the courses that are available to users, but is also the new home of our Knowledge Base. The Knowledge Base is where you […]
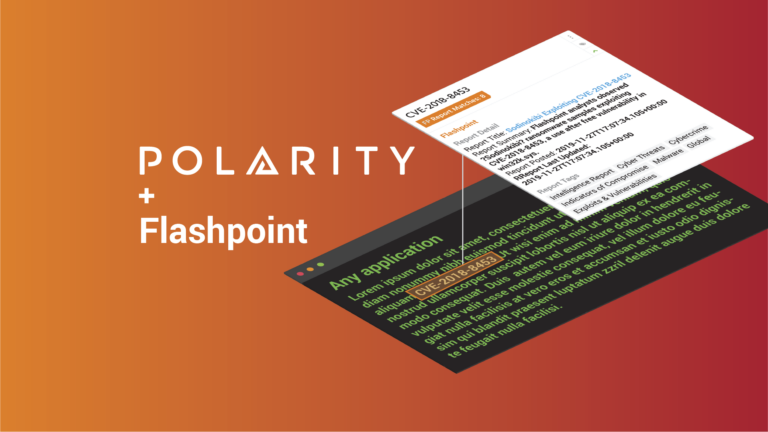
Automatically Access Key Intelligence Reports with the Polarity-Flashpoint Integration
More and more sensitive information ends up on illicit online communities every day, and trying to comprehend all of that information and turn it into actionable intelligence for your organization is difficult. Flashpoint provides Business Risk Intelligence (BRI) to empower organizations worldwide to combat threats and adversaries. Fueled by a combination of sophisticated technology, advanced data collections, […]
How to Avoid Security Analyst Burnout
A roadmap for the passionate, dedicated, tired analyst (and their organization) In the constantly evolving threat landscape where there are 24/7, nonstop threats occurring, Security Analysts are constantly having to adapt to new techniques in an incredibly demanding environment. Keeping up is no easy feat – between working long hours, learning on the fly, and frequently operating […]
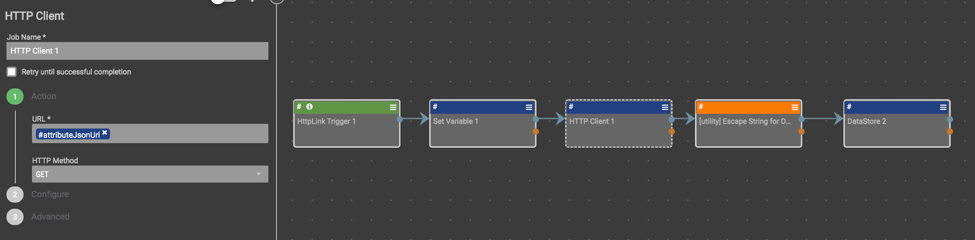
Playbook Fridays: The Indicator Importer Spaces App
A Case Study in Using Playbooks with Spaces Apps How to use Playbooks to make spaces apps more effective You can find the Indicator Importer spaces app discussed in this post here. There are two goals for this blog post: To introduce the “Indicator Importer” spaces app (designed, open-sourced, and maintained by ThreatConnect users). How to […]

Polarity’s Year in Review: What we learned, how we changed, & what we want to accomplish in 2020
An Interview with Polarity’s CEO, CSO, and CTO 2019 – what a year for Polarity! From big product updates to growing our team to adding 42(!) new integrations, we have a lot to look back on – and even more to look forward to. Get an inside look at Polarity’s 2019 reflections and 2020 aspirations through the eyes of […]

The New Polarity Update Just Made Your Team That Much More Efficient
Team Polarity is thrilled to announce our all-new Web and Server Releases! These releases will introduce some really exciting new functionalities throughout our platform that give users even more flexibility, transparency, and customization power. New Features Who else has seen this Annotation? Now, users can see who else has seen any annotation when they view […]
The Polarity-Intel 471 Integration Arms Users with Instant Cybercrime Intelligence
Security analysts rely on cybercrime intelligence to lead them in threat investigations. Without the information available to reference potentially malicious activity, they lack the context to keep their organizations safe and secure. That’s why cybersecurity teams leverage tools like Intel 471, to mitigate threats with as much information in their arsenal as possible. What is Intel […]

The Polarity-Google Translate Integration Introduces a Simple Solution to a Global Problem
Due to the global reach of the dark web, there is no default language for cyber threats, leaving analysts to rely on tools like Google Translate to understand and mitigate threats in languages foreign to them. While translation tools certainly help bridge the knowledge gap, it is also tedious and time-consuming for analysts to repeatedly copy and […]
Playbook Fridays: Leveraging ThreatConnect to Enrich Greynoise IOCs
Querying GreyNoise’s both free and paid APIs to retrieve insights on IOCs for alert triaging and filtering purposes Analysts get inundated with alerts from all sorts of activity; both targeted and also part of widespread activity such as mass port scanning, crawlers, search engines, etc. Our customers wanted a way to use GreyNoise data from […]
