
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.

The Importance of Assessing & Communicating the Financial Impact of Cyber Risks
Just as a captain would navigate their ship across vast oceans, it’s the responsibility of business leaders to determine the direction of the overall corporate strategy. To do this effectively, they need to understand their environment and the conditions that may hinder them along the way. Unfortunately, things aren’t always smooth sailing in real […]

Supercharge Your Security Operations With ThreatConnect 6.5
Security operations teams are super busy and it’s not getting any easier. Analysts need to be able to get more done in their day by working smarter, faster, and better. We get it and we hear you! In this release of ThreatConnect 6.5, we have supercharged the ThreatConnect Platform with some exciting updates: Threat Intel, […]
A Long Way in 11 Years: I’m Passing the Torch at ThreatConnect
After 11 years the time has come for me to pass the torch as ThreatConnect’s CEO. This decision, although hard, is one that I make with great pride for how far the company has come from founding through startup, to what it is today. I’m so proud of the advancements we’ve driven in cybersecurity, proud […]
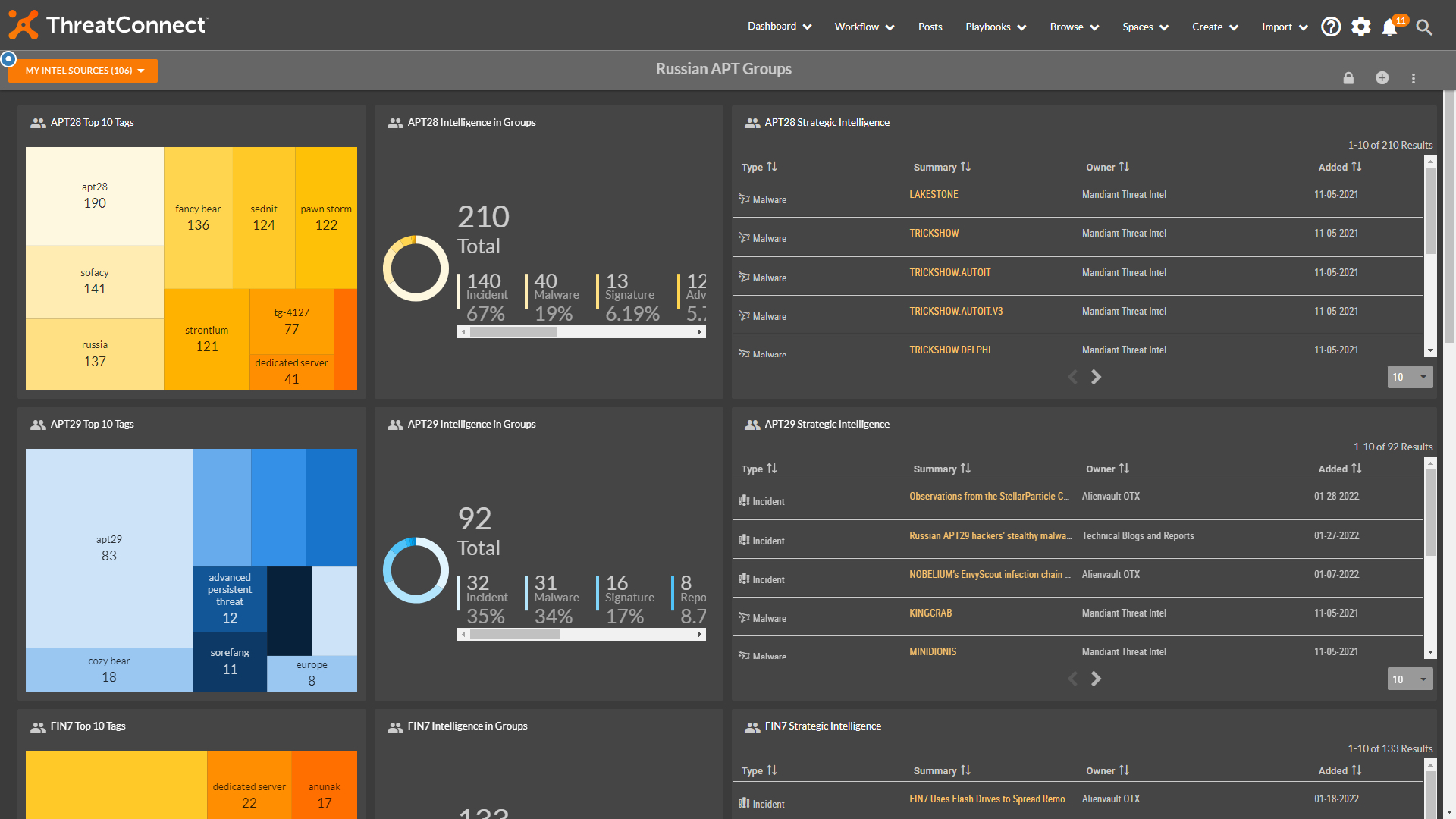
How To: Russian Threat Actor Dashboards
Since our previous threat intelligence dashboards blog on how to get more visibility over the threat landscape associated with the Russian-Ukraine war, the situation unfortunately hasn’t been resolved, and the U.S. Government has recently issued statements warning of potential cyberattacks by Russia against the United States ThreatConnect has continued to look at how we can […]

Every Type of SOC Needs a SOAR
Many organizations have a Security Operations Center (SOC). It may not be one that has a large room full of analysts, engineers, threat hunters, and incident responders, with a wall of monitors providing a heads-up display for the staff. It may be a couple of staff working remotely augmented by a SOC as a […]

To Code Or Not To Code
To code or not to code? That is the question that many security teams grapple with when attempting to solve a specific problem or introduce a new capability. While TIP and SOAR platforms like ThreatConnect offer many out of the box applications and integrations to support threat intelligence and security operations teams, there may come […]
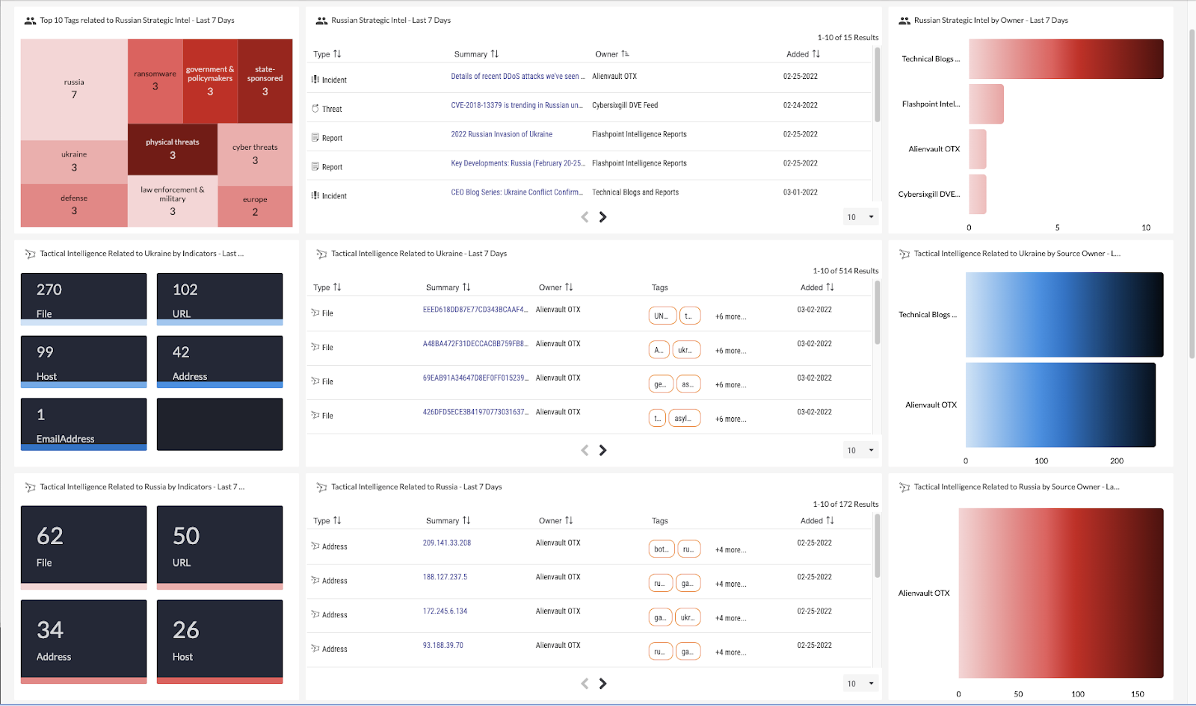
How to: Dashboards for Ukraine Conflict Threat Intelligence
The ThreatConnect Platform is optimized for providing organizations the ability to create a custom dashboard for pulling together real-time, topical threat intelligence into a single view. The current situation in Ukraine has led organizations to ask – “how should I operationalize our intelligence related to this situation so we can have a better perspective on […]

Let’s talk about CFOs and Cyber Risk
If you have read my previous three blogs in this ‘Let’s talk’ series, you’ll know that we’ve talked about our conversations with CISOs and CIO – and now it’s time to turn our attention to Chief Financial Officers (CFOs). The CFO’s job is really important. They’re the ones who determine financial strategy and budgets. Usually, […]
Software and Seinfeld with ThreatConnect’s CAL™
It’s been awhile since the CAL Analytics team has updated the world on our latest creations. Right before the holidays, we released our CAL 2.11 update (some months after our CAL 2.10 update). Both of these major releases shared a common theme: getting you more data. Now that people are returning to work and facing […]

Let’s talk about CIOs and Cyber Risk
In our previous blog, we looked at how cyber risk quantification (CRQ) can help CISOs and their teams to address some of the most pressing cybersecurity issues today. But change requires buy-in, so cross-functional collaboration and communication are vital. In this blog, we are going to look further into the concerns of their fellow C-suite […]

Let’s Talk About CISOs and Cyber Risk Quantification
Chief Information Security Officers (CISOs) serve a critical role in protecting their business from internal and external threats. They need to design and implement the right resources to mitigate growing digital security risks and maintain regulatory compliance. This requires an understanding of the current and future security risks to business operations that could hinder the […]

It’s Time to Make Crypto Assets First-Class Citizens in Threat Intelligence
As the world evolves from Web 2.0 to Web 3.0 – think decentralized protocols for crypto assets, identities, and compute-services leveraging blockchain technology – cyber threat teams must evolve their understanding of the technology at play to stay ahead of threats. That’s easier said than done. Some of the challenges that security teams face are […]
