Explore Our On-Demand Webinars
Exploring CRQ Tools and Solutions?
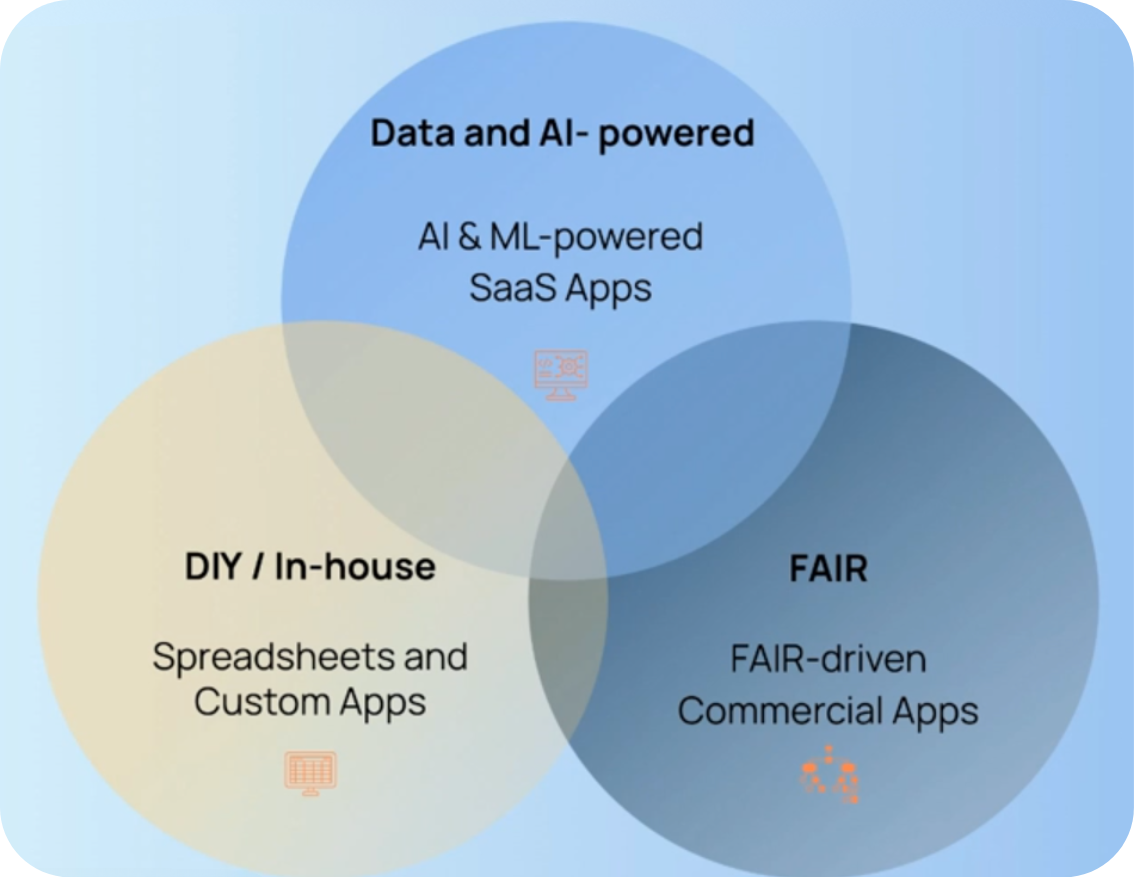
Choosing the Right Cyber Risk Quantification Solution Webinar
Watch this on-demand webinar of the popular use cases for CRQ programs and the benefits and challenges of CRQ approaches and solutions.
Watch Now