No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.

ThreatConnect and Arcsight Joint Solution Brief
ThreatConnect® and Micro Focus have partnered to enable users to detect and act on ThreatConnect intelligence in ArcSight Enterprise Security Management (ESM)™. This integration allows users to combine validated Threat Intelligence in ThreatConnect with their aggregated internal logs from ArcSight ESM. Users can easily spot trends or patterns that are out of the ordinary and act […]
Project CameraShy Closing The Aperture On China’s Unit 78020
China is aggressively claiming territory deeper into the South China Sea, threatening economic and political stability in the Southeast Asia and beyond. The territorial activity is accompanied by high-tempo cyber espionage and malware attacks, malicious attachments and spear phishing, directed at Southeast Asian military, diplomatic, and economic targets. ThreatConnect®, in partnership with Defense Group Inc., […]
Threat Intelligence Platforms
Everything you’ve ever wanted to know but didn’t know to ask Today’s threat environment is complex and dynamic. The internet was built for connectivity, not security, and approaches such as intrusion detection systems, anti-virus programs, and traditional incident response methodologies by themselves are no longer sufficient in the face of the widening gap between offensive […]
ThreatConnect and Crowdstrike Falcon Host
Through an expanded partnership with CrowdStrike, ThreatConnect® users can now act on intelligence in CrowdStrike Falcon Host. This integration allows users to discover and investigate both current and historic endpoint activity within seconds of ThreatConnect sending an indicator to CrowdStrike Falcon Host.
The Diamond Model for Intrusion Analysis
“The Diamond Model for Intrusion Analysis” is the product of years worth of research and development by expert security analysts working on some of the toughest cyber security problems. Informally, it is a cognitive model that presents a framework upon which to discover new activity, maximize analytic pivot opportunities, correlate and synthesize new information, and […]

ThreatConnect and Qualys Vulnerability Management Solution
The ThreatConnect and Qualys Vulnerability Management (VM) integration allows users to query Qualys scan results from within the ThreatConnect platform. Creates tasks, indicators, and attributes in ThreatConnect based on matching results automatically. Shows which machines are vulnerable to specific indicators, so one can pinpoint exactly where to take action. Together, ThreatConnect® and Qualys enable data-driven […]
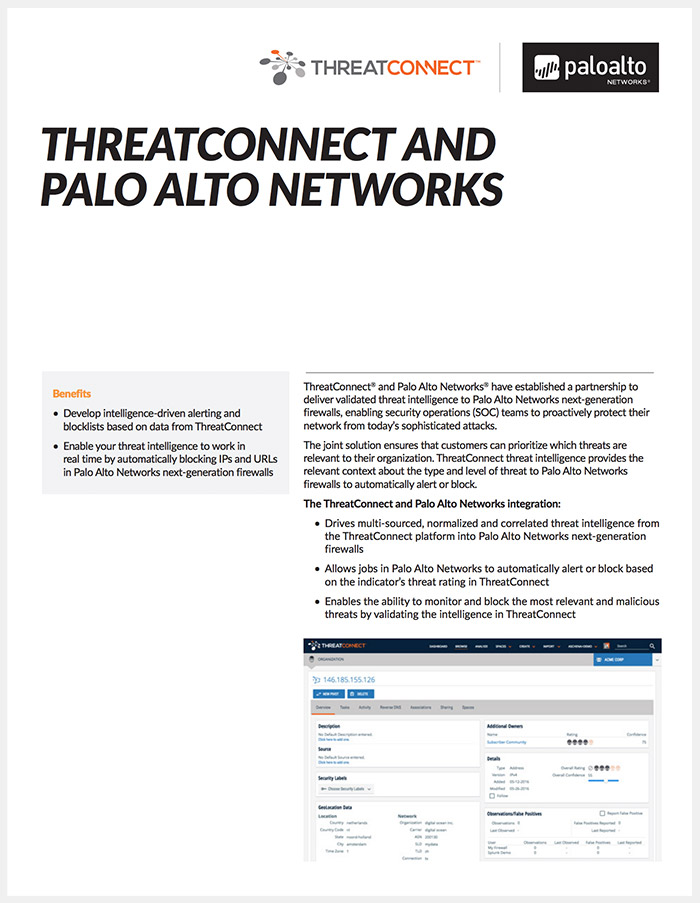
ThreatConnect Palo Alto Networks Integration
ThreatConnect and Palo Alto Networks® have established a partnership to deliver validated threat intelligence to Palo Alto Networks next-generation firewalls, enabling security operations (SOC) teams to proactively protect their network from today’s sophisticated attacks. The joint solution ensures that customers can prioritize which threats are relevant to their organization. ThreatConnect threat intelligence provides the relevant […]