No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.

Building a Threat Intelligence Program – Growing the Program
The 2018 Building a Threat Intelligence Program Survey focuses on how organizations are leveraging threat intelligence to combat increasing cyber threats. Among cybersecurity decision makers, 52% said they lack the staff or resources to monitor all cyber threats.
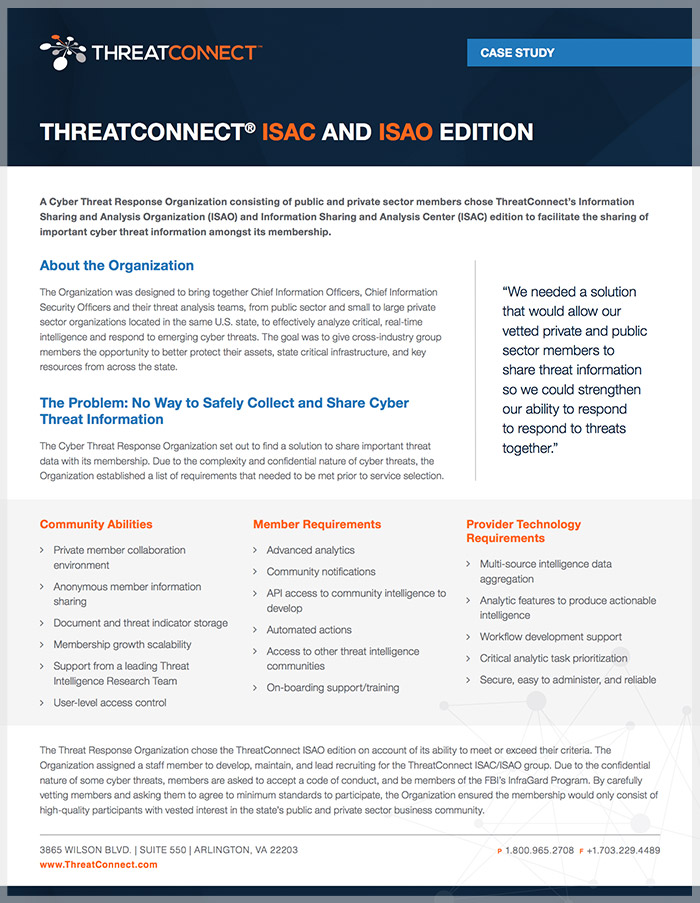
ISAC and ISAO Edition Case Study
This case study illustrates how a Cyber Threat Response Organization used the ThreatConnect ISAC and ISAO Edition to provide a single Threat Intelligence Platform (TIP) for their membership to aggregate their threat data, analyze a complex set of indicators, and take corrective action against their adversaries. Community members are now seeing an improvement in the […]
ThreatConnect Apps: Make the Most of Your Existing Tools
Having all of your threat data in one place can save you valuable time and effort. And maximizing the effectiveness of your existing tools can open the doors to a wealth of actionable threat intelligence for your organization. Watch this webinar to learn how you can aggregate all your data in the ThreatConnect platform by […]
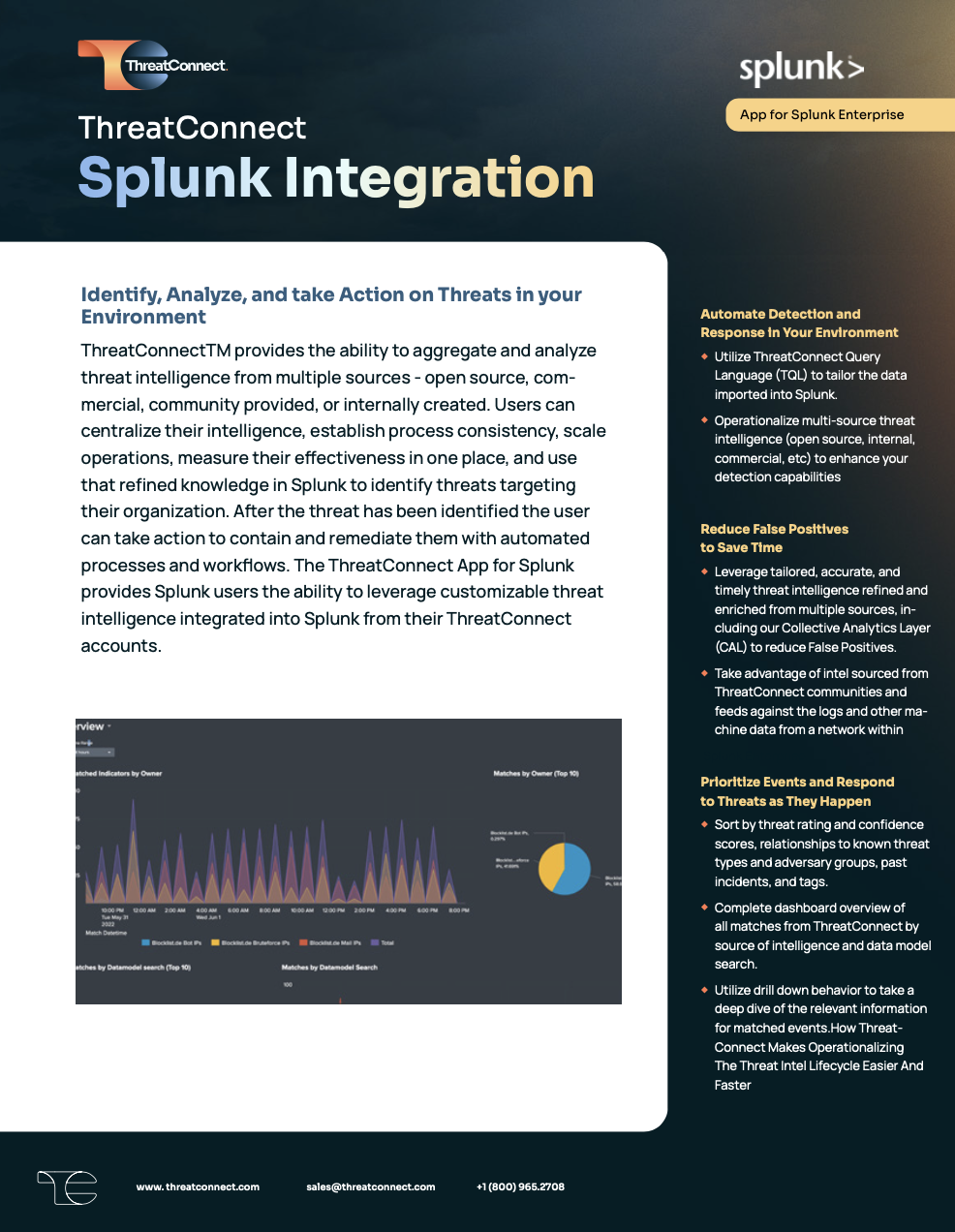
ThreatConnect App for Splunk Enterprise
ThreatConnect provides the ability to aggregate threat intelligence from multiple sources (i.e., open source, commercial, communities, and internally created), analyze and track identified adversary infrastructure and capabilities, and put that refined knowledge to work in Splunk, identifying threats targeting organizations.

More is Not More: Busting the myth that more threat intel feeds lead to better security
It’s a common misconception that a large quantity of threat intelligence feeds leads to more effective security. Unfortunately, threat feed overindulgence can lead to confusion, disorganization, and inaccurate threat reports. Instead of adding more threat intel feeds, you should incorporate the feeds that provide the most value to your organization’s security operations. Download the paper […]
ThreatConnect Enriches Data Case Study
This case study illustrates how an organization utilizing ThreatConnect was able to develop a predictive network defense by taking a single indicator discovered from network traffic monitoring and finding additional indicators for more predictive analytics. Learn how integrated services enabled this organization to manage threat intelligence dynamically.
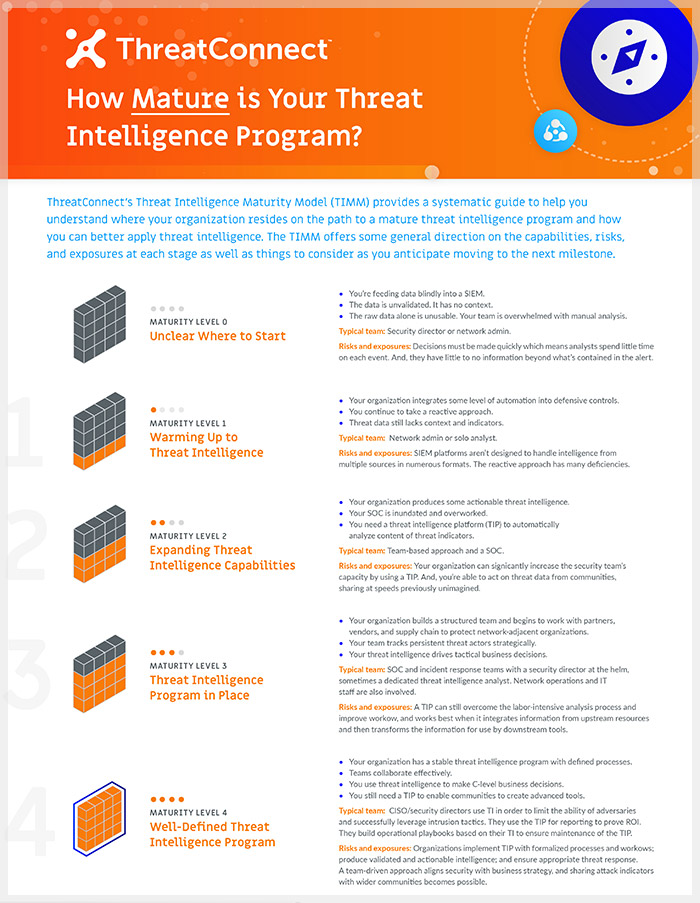
How Mature Is Your Threat Intelligence Program?
Just getting started with a TI program or seeking to expand an existing one? The Threat Intelligence Maturity Model infographic helps you understand where your organization resides on the path to a mature threat intelligence program.
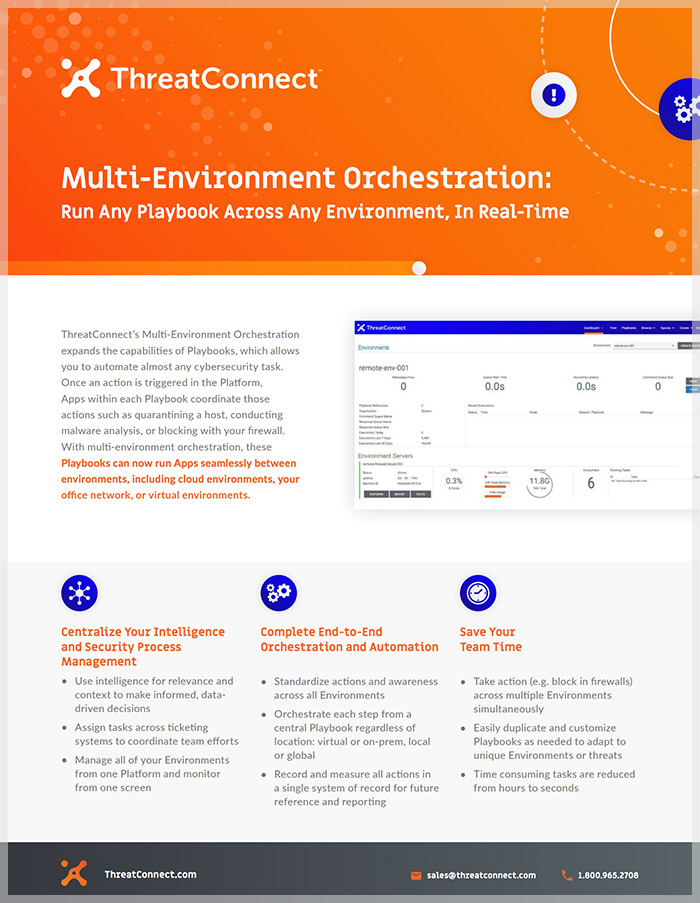
Multi-Environment Orchestration
Run Any Playbook Across Any Environment, In Real-Time ThreatConnect’s Multi-Environment Orchestration expands the capabilities of Playbooks, which allows you to automate almost any cybersecurity task. ThreatConnect’s Multi-Environment Orchestration expands the capabilities of Playbooks, which allows you to automate almost any cybersecurity task.
ThreatConnect’s Customer Success Team
Our Customer Success team is dedicated to ensuring that you can articulate, progress towards, and ultimately achieve your threat intelligence and security program goals. Each customer is assigned a dedicated Customer Success Manager who leverages proactive collaboration, resources within ThreatConnect, and their experience as an intelligence analysts to ensure your organization is moving in the […]
Smarter = Faster: Security Orchestration with Threat Intelligence
Understand how you can make smarter decisions to move faster — both blocking an adversary and disrupting them altogether — by using orchestration with intelligence.
ThreatConnect Powered by SAP HANA
The latest edition of the ThreatConnect platform is built on SAP’s ground-breaking in-memory computing technology to enable you to move at the same speed as your adversary. It has the same robust features analysts, SOCs, and IR teams depend on, only accelerated: delivering actionable insight from massive volumes of threat data faster, more comprehensively, and more […]
Financial Services Sees Success with Smarter Threat Intelligence
We’ll examine one global financial services organization’s set-up and continued success with using the integration, and attendees will walk away with a new tool in their arsenal to effectively analyze and defend their networks using sophisticated threat intelligence.