No Results Match Your Search
Please try again or contact marketing@threatconnect.com for more information on our resources.
ThreatConnect and IntelFinder
IntelFinder is a fully automated and scalable service for customer–specific and actionable threat intelligence. The unique automated design enables IntelFinder to provide a comprehensive all–inclusive intelligence service at a fraction of the cost compared to existing services on the market. IntelFinder performs on–going monitoring to identify a wide variety of potential threats that exist outside […]
SANS Vulnerability Management Survey 2020
The SANS 2020 Automation and Integration Survey looks into how organizations are using automation to discover vulnerabilities and helps establish a thorough process to remediate vulnerabilities.
ThreatConnect and Shodan Integration
ThreatConnect® and Shodan® allow users to enrich their threat data and enhance their decision-making skills when performing an investigation.

Detection of Automatically Generated Domain Names in Real-time with Machine Learning
In our ongoing mission to help make security practitioners faster and more effective at their jobs, we explored a series of machine learning techniques to help detect suspicious domains created via domain generation algorithms (DGAs). While indicative of a sophisticated and well-resourced adversary, these DGAs can be tricky to track and traditional methods require substantial […]
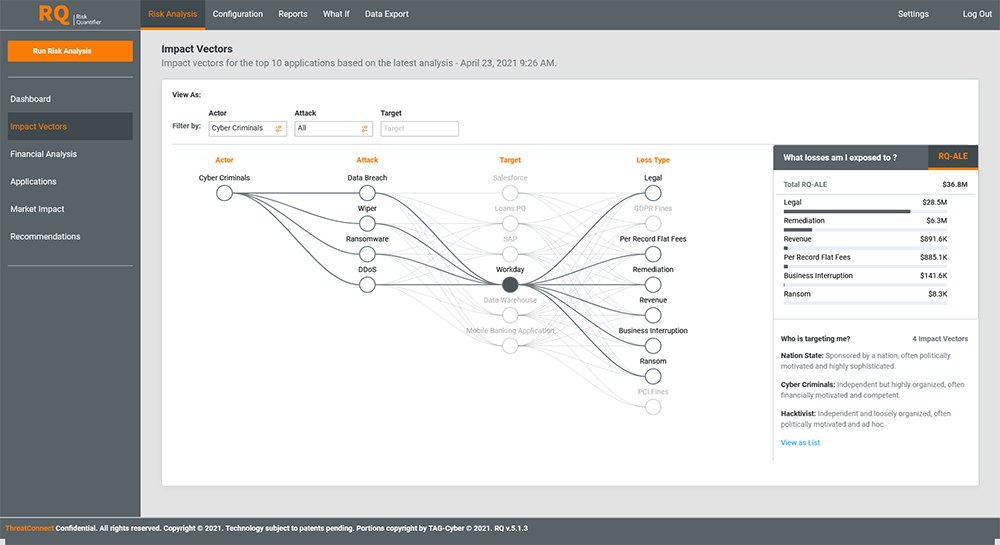
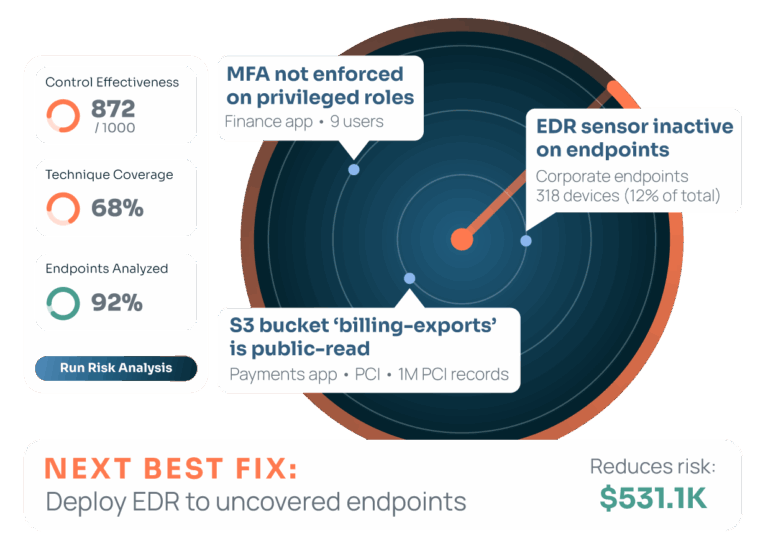
Changing the Way Security Works – Risk|Threat|Response: The Acquisition of Nehemiah Security
In this webinar, we discussed the acquisition of Nehemiah Security. The company provides a simple SaaS solution — RQ (Risk Quantifier) — that enables organizations to identify the cyber risks that matter most by financially quantifying them and providing ROI based mitigations.
Empowering SecOps – Spend Time Where It Matters Most
In this webinar we explore in-depth how security analysts are spending their time versus where they believe they can have the biggest impact… and why the disconnect leads to burnout and turnover.
Proactive Infrastructure Hunting with ThreatConnect & DomainTools
In this webinar, explore how network defenders and incident responders can effectively and efficiently protect their own organizations.
ThreatConnect and DomainTools
Together, ThreatConnect® and DomainTools®Iris Investigate allow security analysts to automate intel processes, investigations, alert triage, and response actions leading to faster detection and response.
Change the Way Security Works
Learn about features and functionality of our platform and discover our vision for changing the way security works.
ThreatConnect and ServiceNow Integration
ThreatConnect Risk Quantifier (RQ) and ServiceNow have partnered together to offer more robust integrations with the ServiceNow Orchestration and ServiceNow Security Operations products, and to launch an enhanced Playbook app for managing ServiceNow records from within ThreatConnect.

ThreatConnect and SlashNext Phishing Incident Response Playbook
SlashNext Phishing URL Analysis and Enrichment enables SOC and IR teams to dramatically reduce the time and effort involved in researching and reporting on suspicious URLs. Whether in emails, network logs, or other digital sources, teams can now get accurate, definitive, automated analysis of suspicious URLs on demand and at scale.
ThreatConnect and SlashNext Agentless Phishing Defense
SlashNext Agentless Phishing Defense is the industry’s broadest real-time phishing threat intelligence feed of live phishing sites and C2s. It’s a continuously updated, high fidelity, block-ready threat feed (i.e. blocklist) of zero-hour phishing sites, complete with IoCs.