Posted
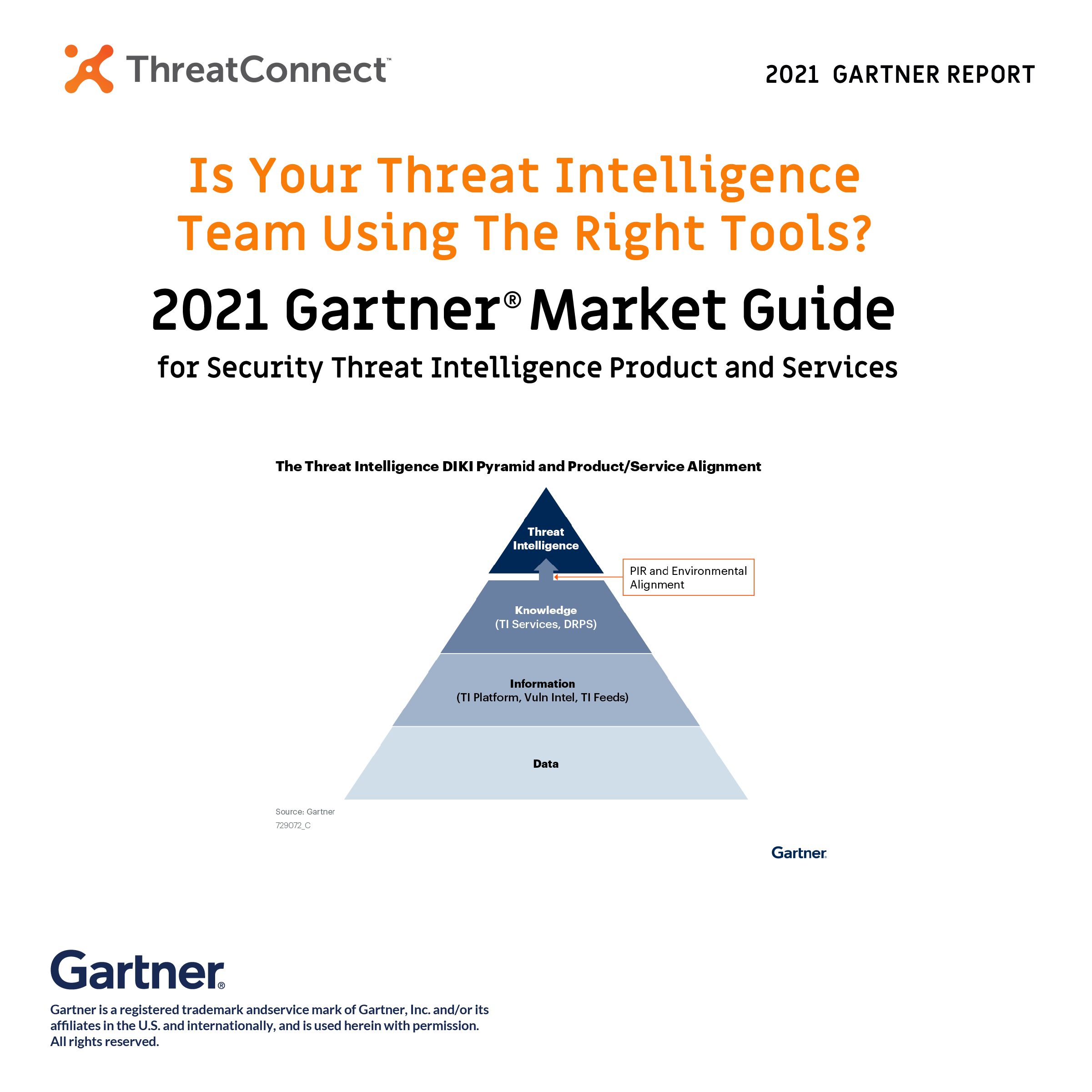
Threat intelligence teams have a problem, a big data problem due to the velocity, variety, and volume, of the different sets of data they collect. Data comes through non-stop in different forms, from different sources, and from different environments. To make matters worse, not all data is good data because it’s not always accurate or relevant to the business. Too often, teams are left parsing through the data manually, slowing down the process to find and understand risks and threats in their environment. Teams need tools to help aggregate and normalize each data feed to find relevant data. When you make sense of the relevant data, you have intelligence.
When cyber threat intelligence (CTI), aka threat intel or TI, is the core of your security program, you’ll fuse TI with security operations, maximizing the consumption, usage, and collaboration between teams. To get there, you need to find the right threat intelligence management tool to manage and operationalize threat intel of greatest concern to the business.
We believe the 2022 Gartner® Market Guide for Security Threat Intelligence Product and Services does a great job of laying out the difficulties TI teams face and recommendations on how to evaluate and leverage the right vendor to get the most value out of your TI program.
As per Gartner, “The threat intelligence market consists of a very large number of vendors with Gartner monitoring 75+ vendors and providers in this market from the commercial space alone.” With so many options and overlaps, how can you find what you need to enable better decision-making and reduce risk?
It starts with a plan in the form of priority intelligence requirements (PIRs). Starting with PIRs may sound obvious, especially if you’re familiar with the Intelligence Lifecycle. Without PIRs your TI program won’t be focused and effective.
“The core of any TI program are priority intelligence requirements (PIRs), used to identify where the organization will focus intelligence efforts and what tools are required to achieve it.” – “Gartner®, Market Guide for Security Threat Intelligence Products and Services” December 2021, John Collins, Ruggero Contu, Mitchell Schneider, Craig Lawson
Setting your PIRs makes the rest of the selection process for TI tools and services easier; it will also help you justify the budget for your TI program. When setting your PIRs, focus on areas that meet the requirements of the business, like use cases with the fastest return on investment (ROI) and the environments you need covered in your growing landscape (cloud, operational technology (OT)).
If you want to get the most out of the threat intel services, Gartner® suggests you must acquire, aggregate, and act. We 100% agree! In our opinion, this means using the tool(s) to align your data feeds with your PIRs and ultimately ensuring you operationalize high-fidelity threat intel and can act on the threats you identify. Knowledge helps detect threats but falls short if you can’t respond.
Getting the most out of your tools leaves you time to focus on operationalizing the TI program and enables the rest of the security team to make intel-powered decisions, including IR, threat hunting, and vulnerability management teams.
Want to know more? This is only a small part. Reach out to us to learn how ThreatConnect’s Platform can help you aggregate, normalize, and act on data.
Gartner®, Market Guide for Security Threat Intelligence Products and Services, 10 December 2021, John Collins, Ruggero Contu, Mitchell Schneider, Craig Lawson
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally, and is used herein with permission. All rights reserved
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.