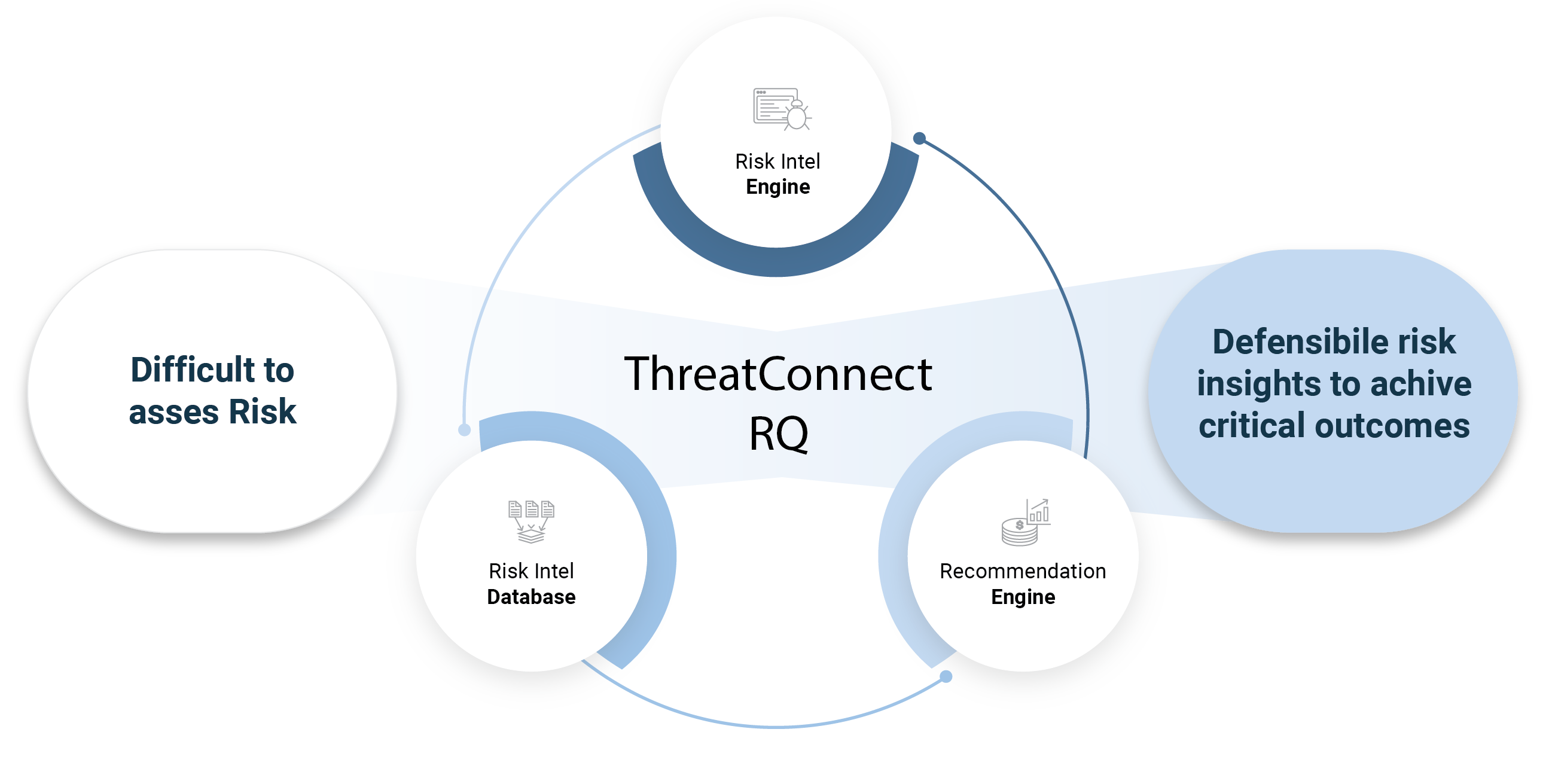
ThreatConnect Risk Quantifier (RQ) makes it fast and easy to analyze and quantify the financial impact of cyber risks, and prioritize remediations. RQ provides the data, AI-powered analytics and recommendations to deliver defensible results without needing to be a cyber risk expert.
Key Capabilities of Risk Quantifier
Data > Feelings
You need defensible, actionable risk intelligence. RQ delivers by analyzing real-world risk, loss, and attack data and specific attributes and context of your business
Insights and Context – Powered by AI/ML
Using AI and machine learning, RQ automates cyber risk analysis, allowing you to rapidly overlay your business context with our models, obtaining the most accurate insights possible.
Prioritize Risk Remediation for Maximum Impact
Choosing which controls and vulnerabilities to tackle first can be challenging. RQ provides financial, impact-based recommendations so you’ll mitigate the greatest risks to your business.
Communicate Impact, Enable Good Decisions
Financially quantifying cyber risks enables you to talk to executives and directors in terms they understand – money and costs – and gain strong alignment when making decisions.
Start Quickly, Grow As You Need
RQ meets you where you are in your cyber risk quantification journey, whether using custom models or FAIR.
Overcome the Skeptics with Defensible Data
RQ makes your cyber risk analyses and decisions transparent and defensible to skeptics who might not believe or understand the validity of your approach.
Covering Your Most Critical Use Cases
- Risk and Control Mitigation Prioritization
- Defining SEC Materiality / Risk Appetite
- Improving cyber risk communication
- Vulnerability Prioritization
- Third Party & Supply Chain Risks
- Compliance with regulations and frameworks
- Managing End-of-Life assets
- Risk Exception and Gap Management
Focus on what matters to you
Quantify cyber risks with speed and ease
Use an open, data-driven approach, rather than subjective inputs to models, to quantify cyber risk.
Learn how a ThreatConnect RQ made risk analyses easier, faster, and more robust.
Evolved cyber risk management
Leverage data and AI-powered cyber risk quantification
ThreatConnect RQ – The Industry-leading CRQ Solution
Make smart cybersecurity investment decisions
Prioritize risk mitigation investments based on defensible financial impact, not gut feelings
Learn how to operationalize cyber risk quantification.
Want to learn more about cyber risk quantification?
Learn why CRQ is important to 3rd-party risk management.
We Power CRQ In Leading Solutions
RQ Integrates with Your Security Stack














Choosing a Cyber Risk Quantification solution
Understand how to choose the right platform for your cyber risk management strategy to strengthen your cybersecurity programs.
ThreatConnect RQ – The Industry Leading CRQ Solution
Learn why ThreatConnect RQ is an industry leader in Cyber Risk Quantification Software according to Forrester.
See ThreatConnect Risk Quantifier in Action
Want to experience the power of ThreatConnect RQ yourself. Take our self-guided solution tour today.