RSA NetWitness Platform
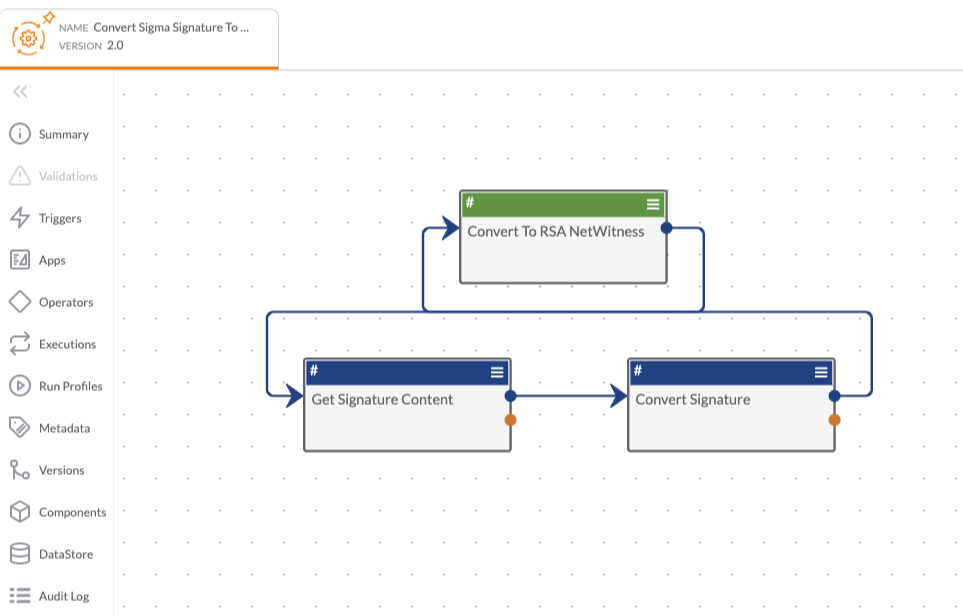
ThreatConnect and RSA have partnered to enable users to detect and act on ThreatConnect intelligence in the RSA Netwitness Suite. With this integration, users can aggregate their internal logs and combine them with validated threat intelligence, so they can easily spot trends or patterns that are out of the ordinary and act on them efficiently. The integration helps ensure organizations are sending validated and actionable intelligence from ThreatConnect to the RSA Netwitness Suite First, it takes aggregated logs from the RSA Netwitness Suite and combines them with user's threat intelligence in ThreatConnect. ThreatConnect provides context with the indicators and enables a user’s security team to easily spot out-of-the-ordinary trends or patterns and act on them efficiently. Benefits and features include:
- Sends all available threat data from ThreatConnect into RSA Netwitness Suite for validated alerting
- Provides the necessary context to be able to take action on the indicators
- Enables real-time threat analysis and indicator correlation
- Automates the detection of advanced threats
- Ensures that you are sending validated threat intelligence to RSA
This listing consists of 4 apps.
The RSA NetWitness Logs & Packets Playbook app imports ThreatConnect intelligence data into RSA for analysis, threat identification, incident response, and more.
The RSA NetWitness Platform - Respond Playbook app allows users to ingest incidents and alerts from RSA Netwitness as Cases in ThreatConnect. From there ThreatConnect Workflow can orchestrate a predefined alert triage process and guide the analyst through a combination of automated and manual tasks to resolve the incident. Additionally, the original incident in Netwitness can automatically be updated with a Journal entry containing the results of investigation and the status can be marked closed or as a false positive. The following actions are available to Playbook designer from within the app:
- Get Incident
- Update Incident
- Get Incidents By Date Range
- Add Incident Journal Entry
- Get Incident Alerts
- Parse Alert
- Parse Event
The RSA NetWitness Platform - Respond Service app is used to pull NetWitness incidents on a schedule and trigger Playbooks when a new incident matches the criteria. The main use case for this app is to ingest RSA NetWitness incidents as Cases in ThreatConnect.
The RSA NetWitness Platform - Events Playbook app enables the automation of search, enrichment and hunting actions with the RSA NetWitness raw events, PCAP, and metadata. The app allows Playbook designers to query the SDK/Query, SDK/Content, SDK/Values, and SDK/Packets API endpoints as part of their security workflows and playbooks. This is a very technical but powerful app in what it enables.
These apps can be found in the ThreatConnect App Catalog under the following names:RSA NetWitness Packets and Logs, RSA NetWitness Platform - Events, RSA NetWitness Platform - Respond, and RSA NetWitness Platform - Respond Service.
Keep Reading