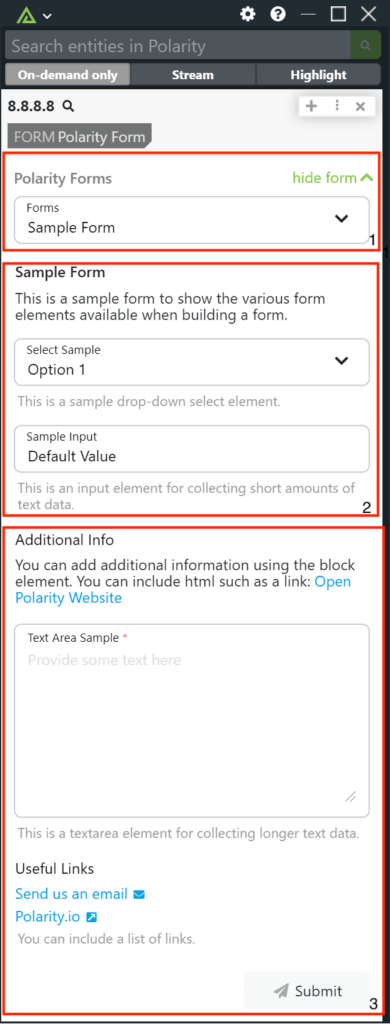
Polarity
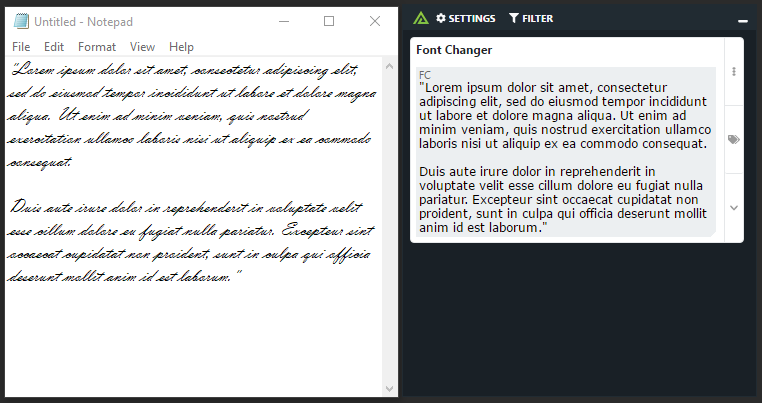
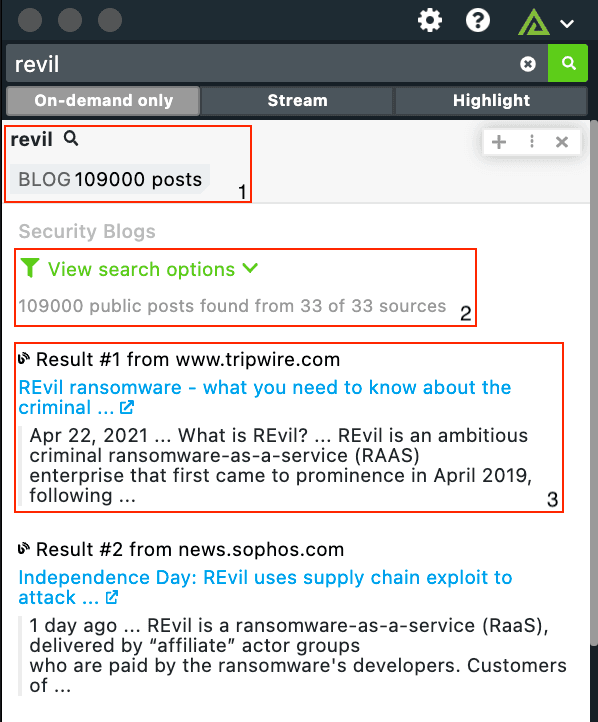
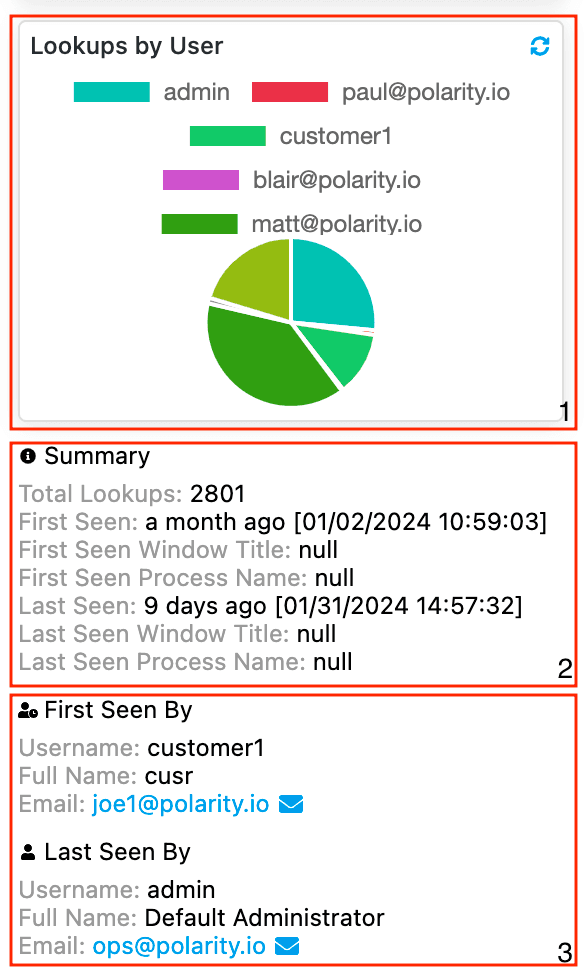
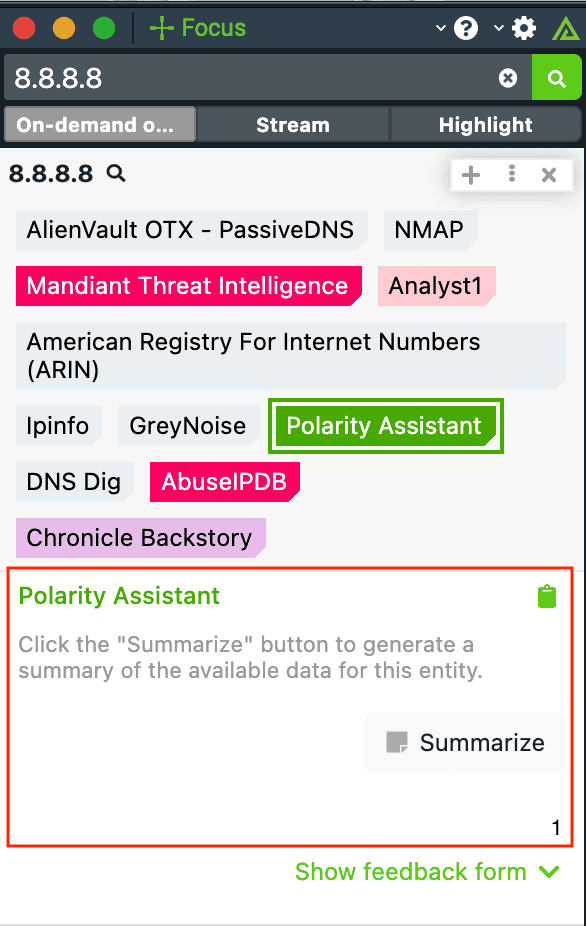
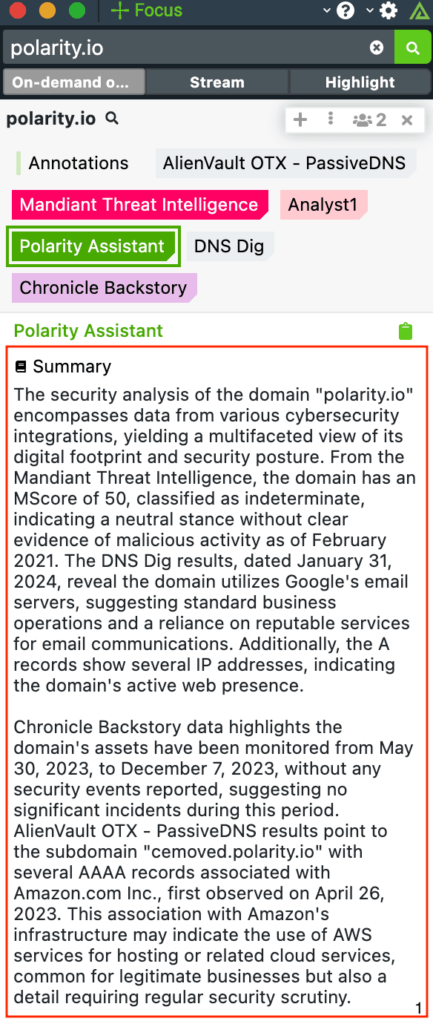
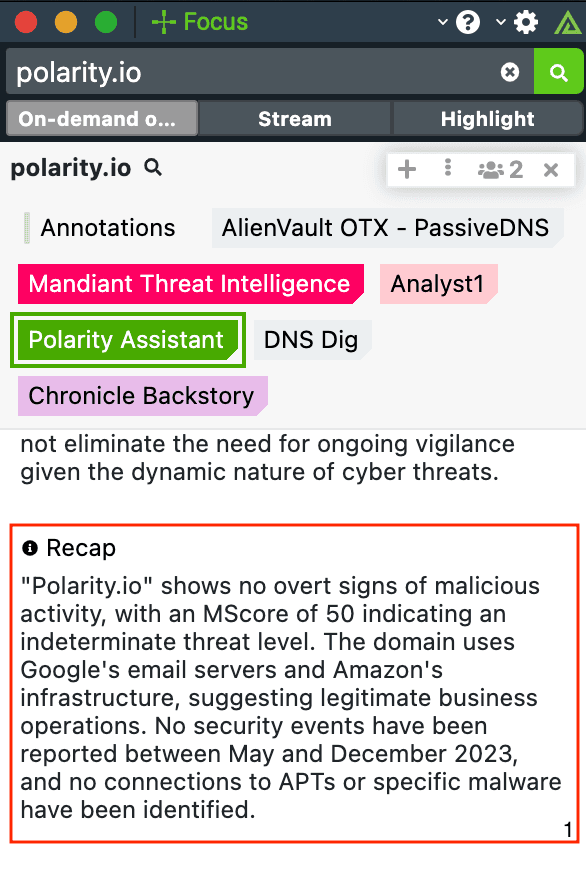
If you had a photographic memory, how much faster would you be at your job? Now what if you had a collective memory across all members of your team, organization, or industry, how much better would you be at your job? Polarity has developed a technology that makes this possible through software. The system analyzes the contents of users’ computers screens and gives them real-time access to information without affecting their existing workflow. The system makes it easy to capture new “memories” so that if other users are looking at similar content, they will automatically be notified of the most relevant information at the most opportune time.
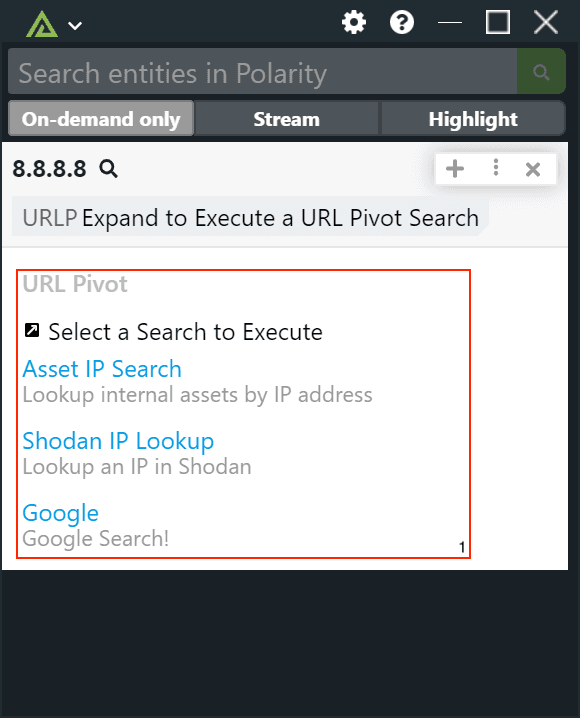
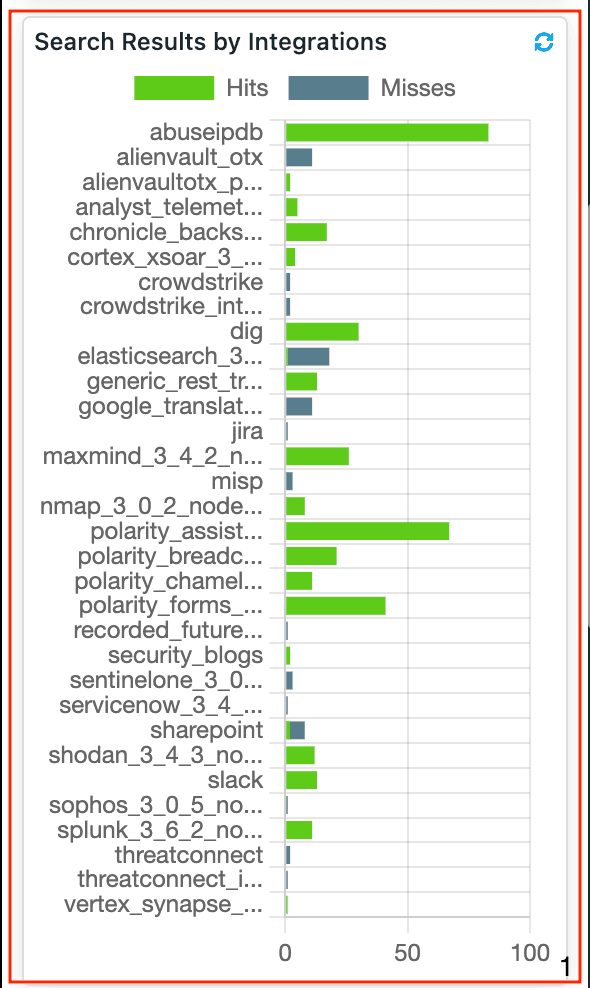
Integrations
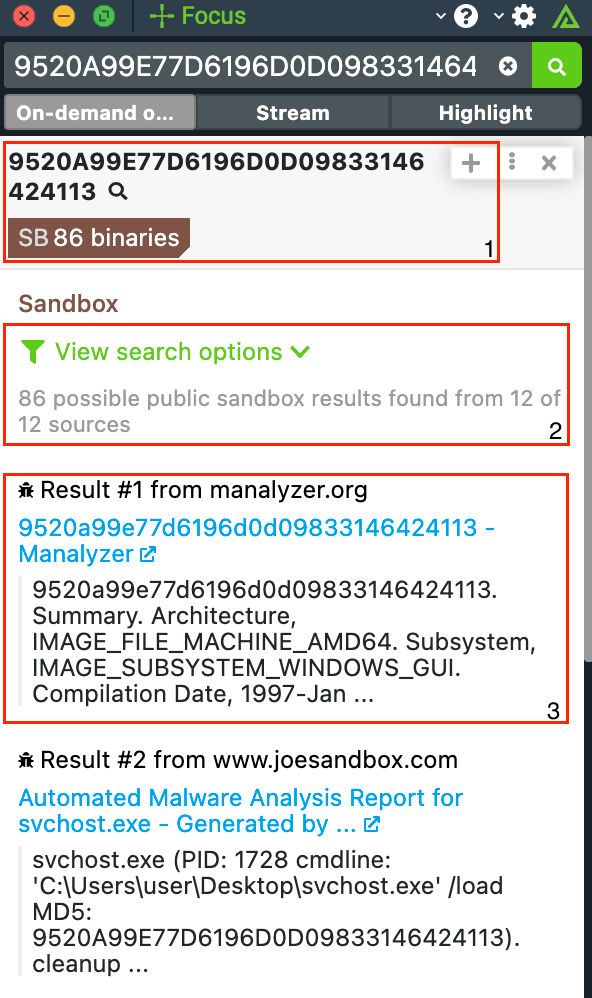
Sandboxes
Keep ReadingRelated Resources
Built By Polarity
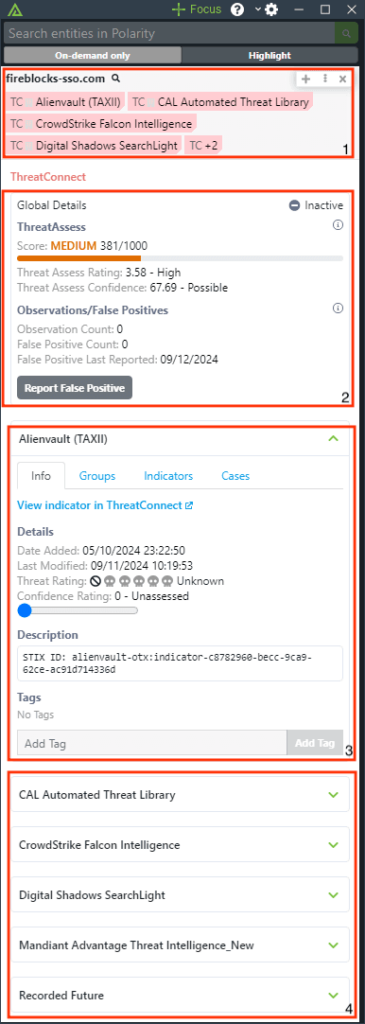
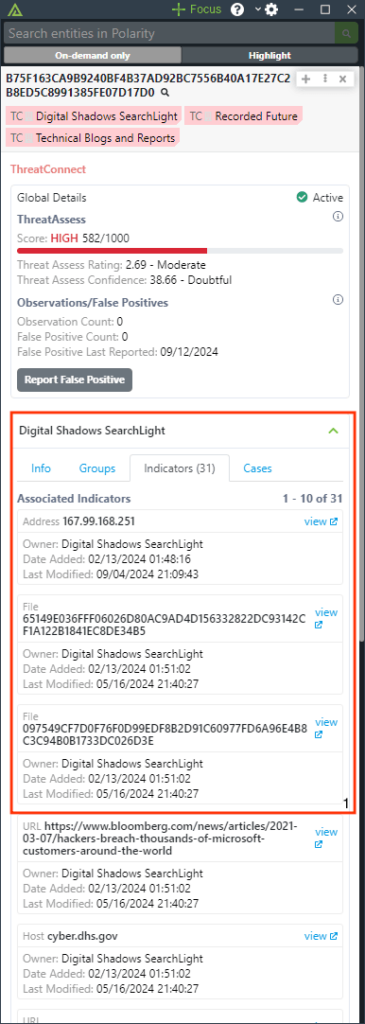
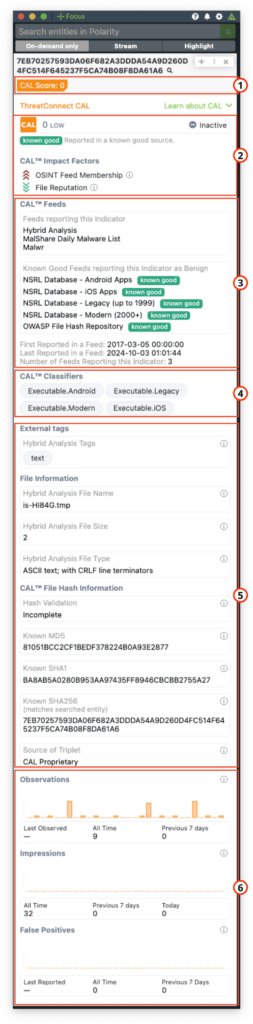
ThreatConnect with Polarity
Keep ReadingRelated Resources
Built By Polarity
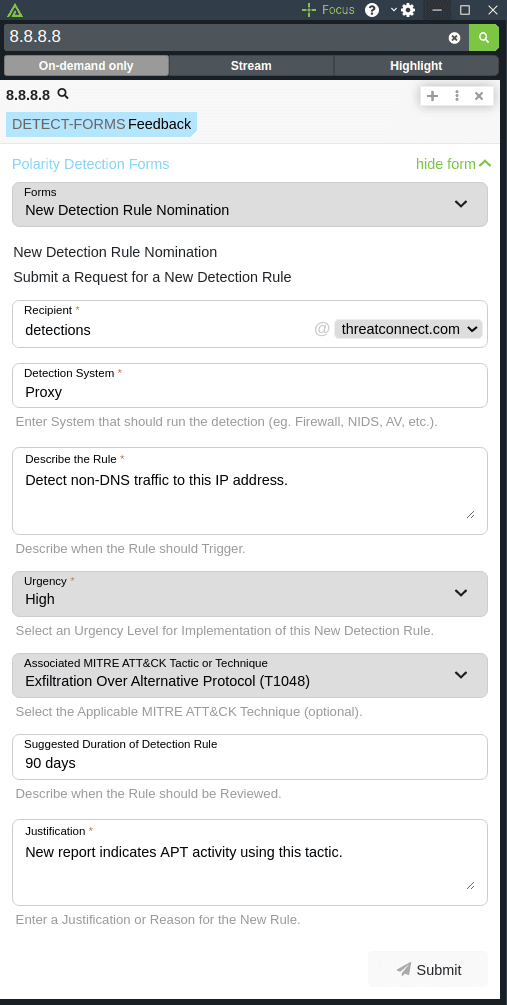
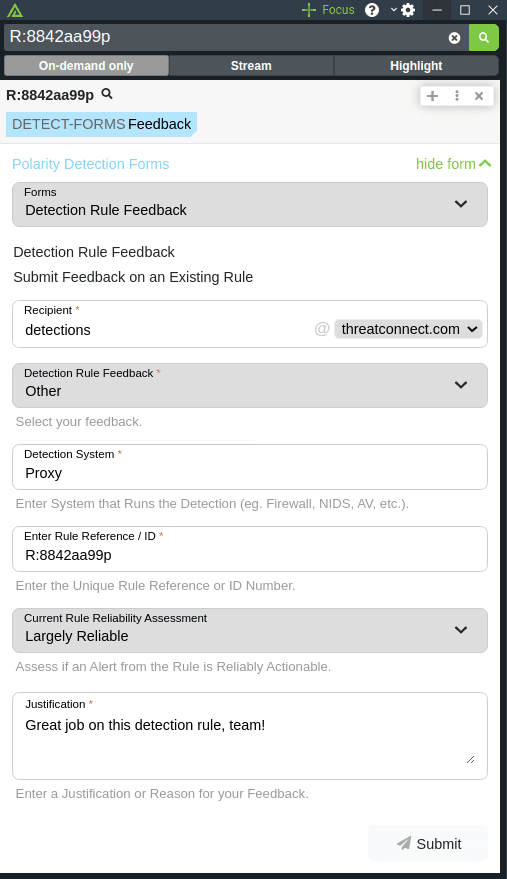
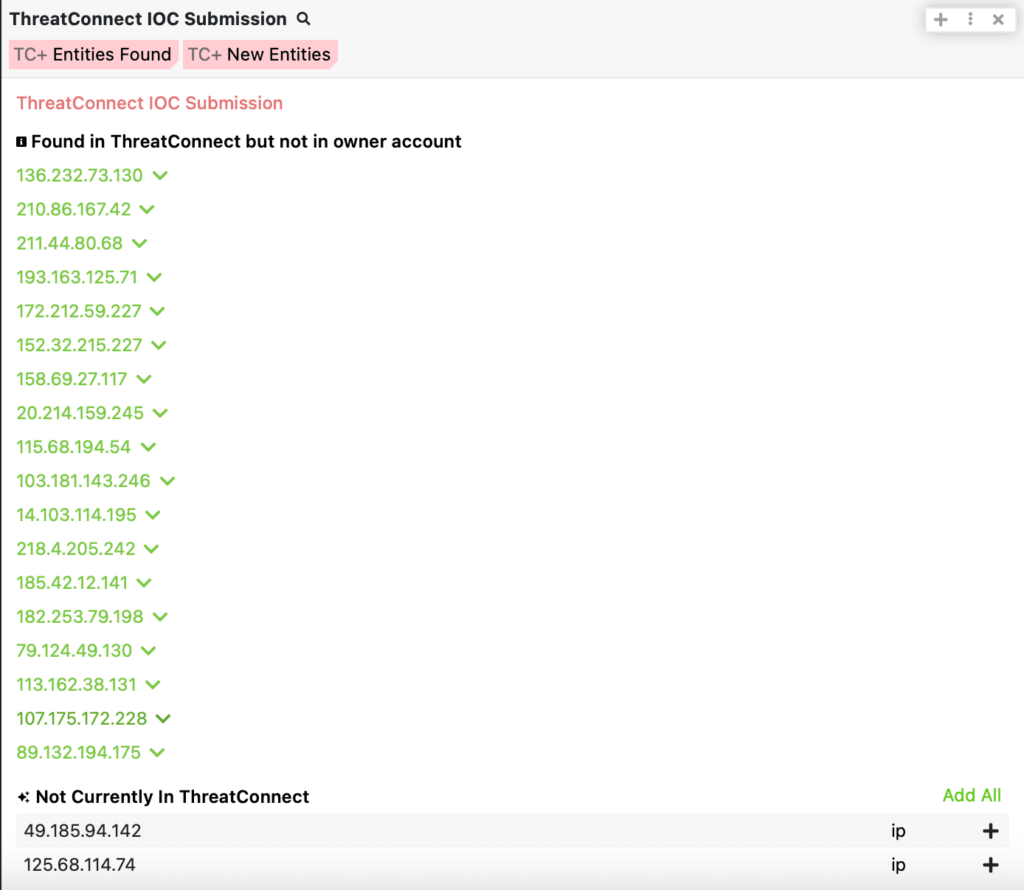
ThreatConnect IOC Submission with Polarity
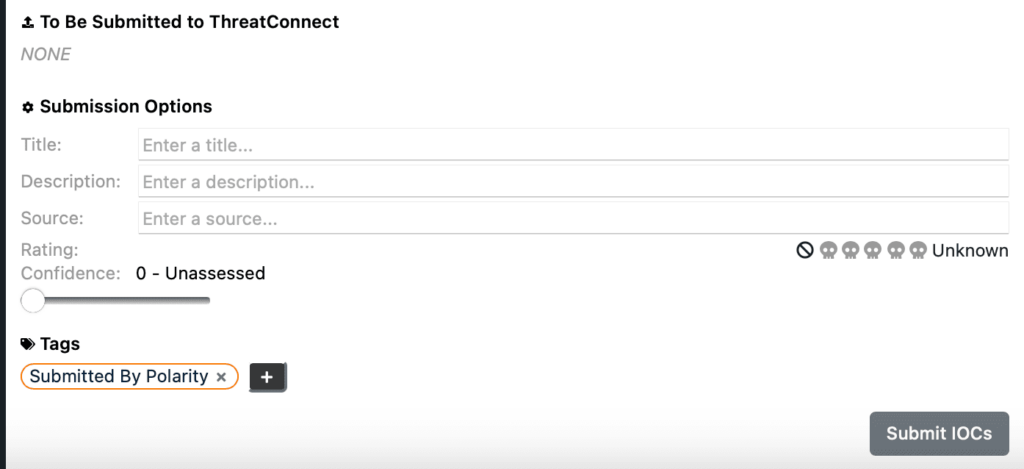
Keep ReadingThreatConnect Intel Search with Polarity
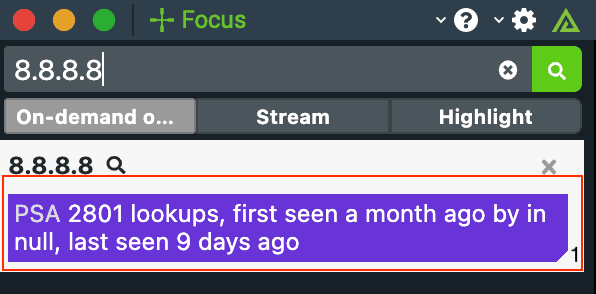
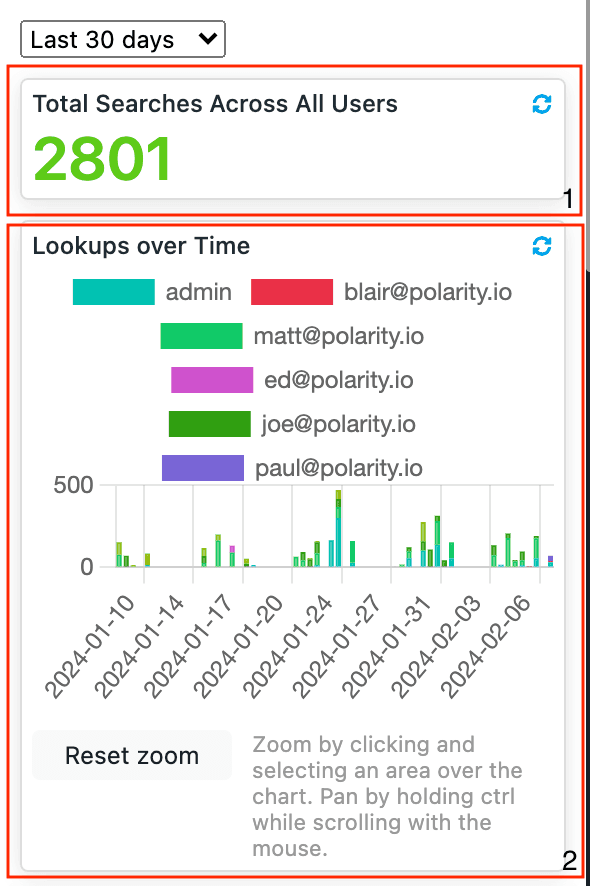
Keep ReadingAnalyst Telemetry - Elasticsearch
Keep ReadingAnalyst Telemetry - Splunk
Keep ReadingRelated Resources
Built By Polarity

 Polarity
Polarity