Posted
In cybersecurity, contextual data is important. Contextual data with speed becomes everything. But many cybersecurity teams are too far away from the critical information they need to make fast and accurate decisions. Time is not on your side. It is just an unfortunate fact that threat and security researchers spend too much time digging through multiple threat feed sources and disparate logs searching for key information and not enough time making the data actionable.
ThreatConnect’s new Intelligence Anywhere brings the critical information your security team needs within fast and easy reach. You can review web-based resources and have potential indicators of compromise and related data elements highlighted to show that additional information is available. In one click, you can find expanded data gathered from the ThreatConnect CAL Automated Threat Library and all the threat intel sources available.
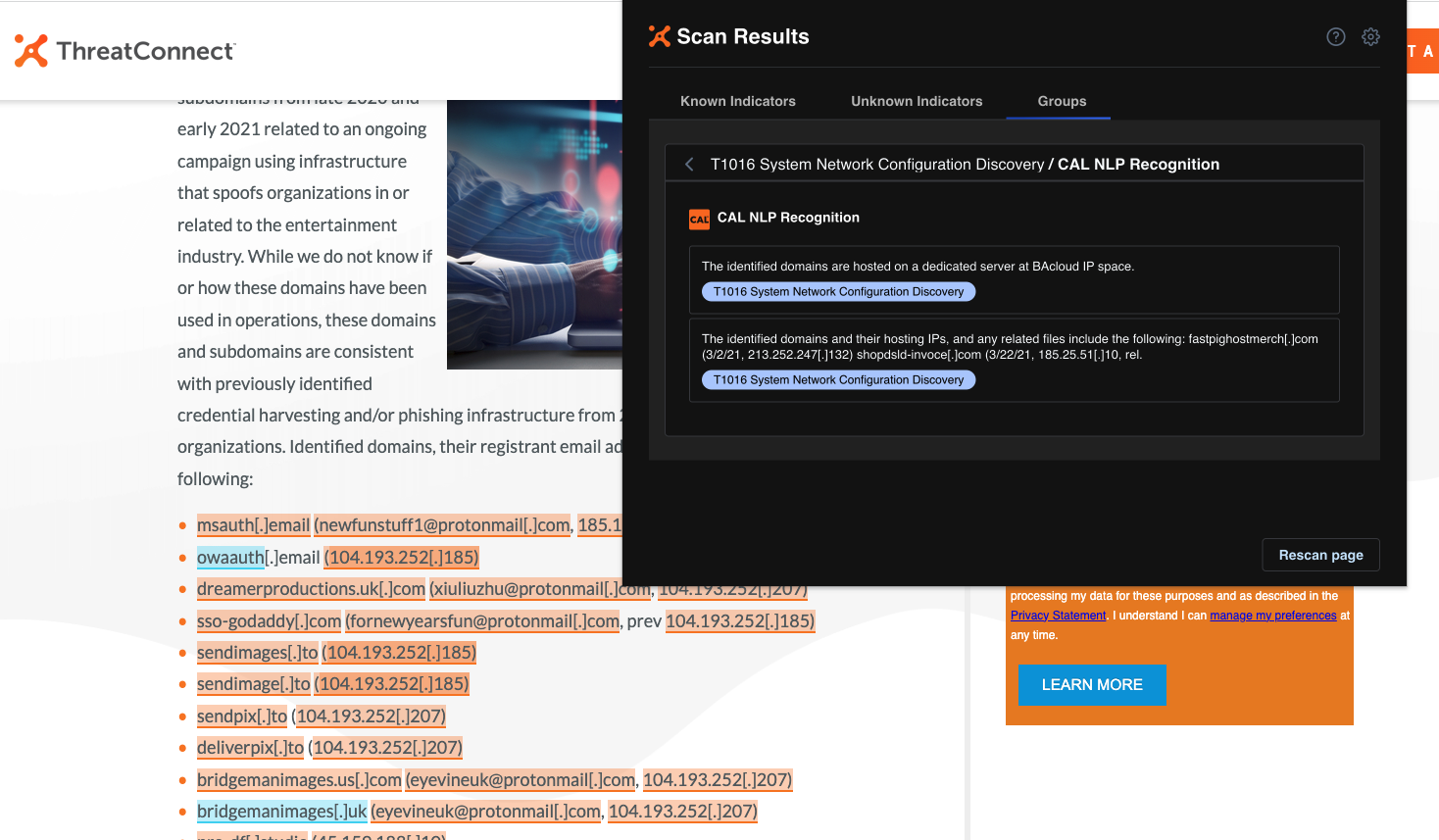
A practical example of Intelligence Anywhere is being used to disambiguate threat actor groups. So, in your document, you might see the term APT41. ThreatConnect Intellectual Anywhere has highlighted and hyperlinked this term to show that there is data available. You can click the hyperlink to instantly see, “APT41 is a threat group that researchers have assessed as a Chinese state-sponsored espionage group that also conducts financially-motivated operations. Active since at least 2012, APT41 has been observed targeting healthcare, telecom, technology, and video game industries in 14 countries. APT41 overlaps at least partially with public reporting on groups including BARIUM and Winnti Group.”
Further, you can click an additional highlighted link and learn that “The state-sponsored group APT41 is also known as ARIUM, Winnti, LEAD, WICKED SPIDER, WICKED PANDA, Blackfly, Suckfly, Winnti Umbrella, and Double Dragon.” This contextual data helps maximize insight so that the best-informed decisions can be made quickly and efficiently.
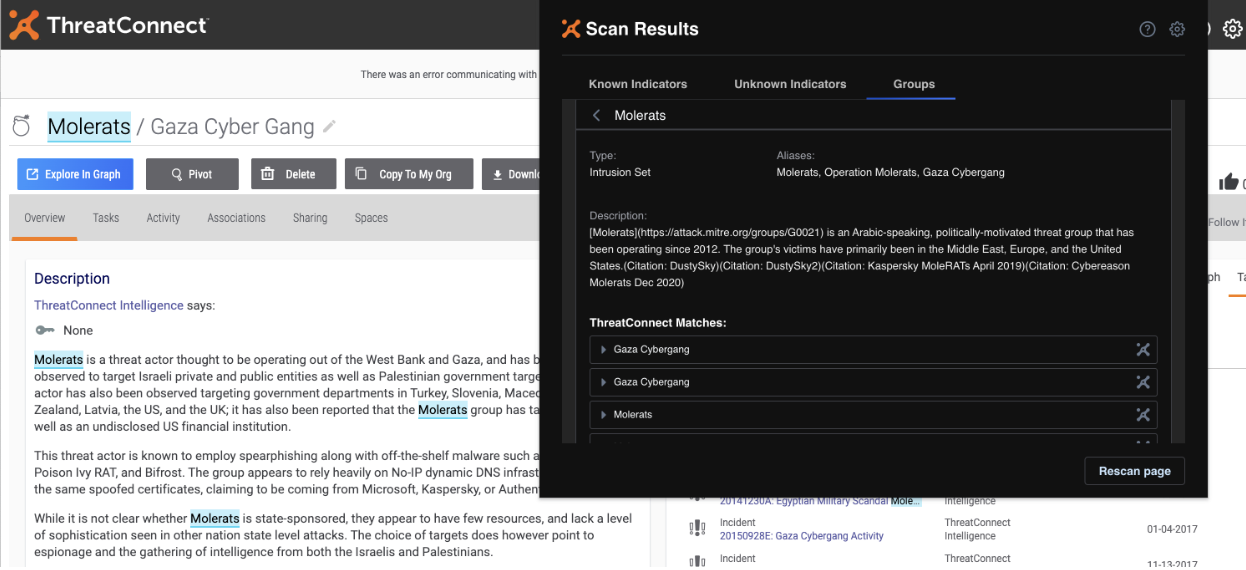
By operationalizing rapid and easy access to threat intelligence, you help maximize collaboration, break down silos, and increase the value of your threat intelligence program. ThreatConnect Intelligence Anywhere provides an easy and automated way to share rich, contextualized threat intelligence on web pages or web-based SaaS tools.
It’s Not a Job—It’s an Adventure
Your SOC team doesn’t have a job—almost every day is a hand-to-hand combat adventure. Every day, your team needs the tools and information to gain an advantage on the threat actors that would do your organization harm. Speed and rapid access to information enables your team to make the best decisions and execute them faster.
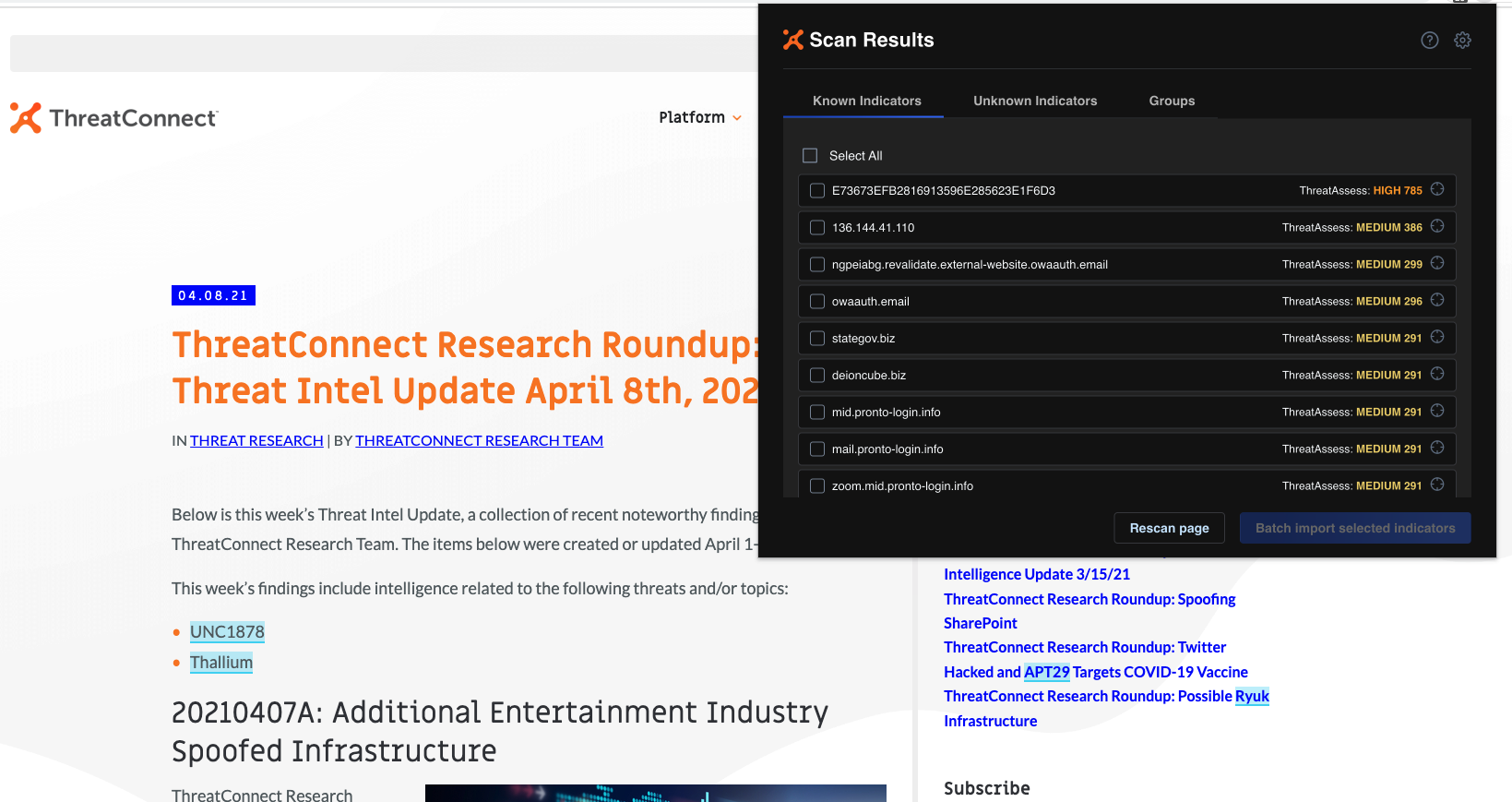
ThreatConnect Intelligence Anywhere can enable your team to leverage automated data retrieval for maximized efficiency. The speed of access to relevant and important data can improve collaboration throughout the team and improve decision-making.
Behind Intelligence Anywhere is the full power and capability of the ThreatConnect platform. You can leverage our automation and orchestration to power your cyber threat intelligence operations to scale and execute with light speed. ThreatConnect’s built-in automation and orchestration can reduce workloads and help your team make better security and business decisions. Your SOC will benefit from faster, smarter, and repeatable processes with accessible and readily available intelligence, and customizable workflows in the ThreatConnect platform.
Learn More
ThreatConnect Intelligence Anywhere can give you the speed you need. To learn more, check out its features and benefits here.
To learn more about how ThreatConnect can help your organization maximize insight, increase efficiency, and improve overall collaboration, please take a look at the ThreatConnect Platform. Reach out to us via https://threatconnect.com/contact/, and we’ll be pleased to share a customized demonstration of the ThreatConnect Platform.
