Posted
ThreatConnect has long supported the MITRE ATT&CK framework and, we are delighted to be among the first to support MITRE ATT&CK Sub-techniques.
As a quick refresher, MITRE ATT&CK® is a globally-accessible knowledge base of adversary tactics and techniques based on real-world observations. The ATT&CK knowledge base is used as a foundation for developing specific threat models and methodologies in the private sector, government, and the cybersecurity product and service community.
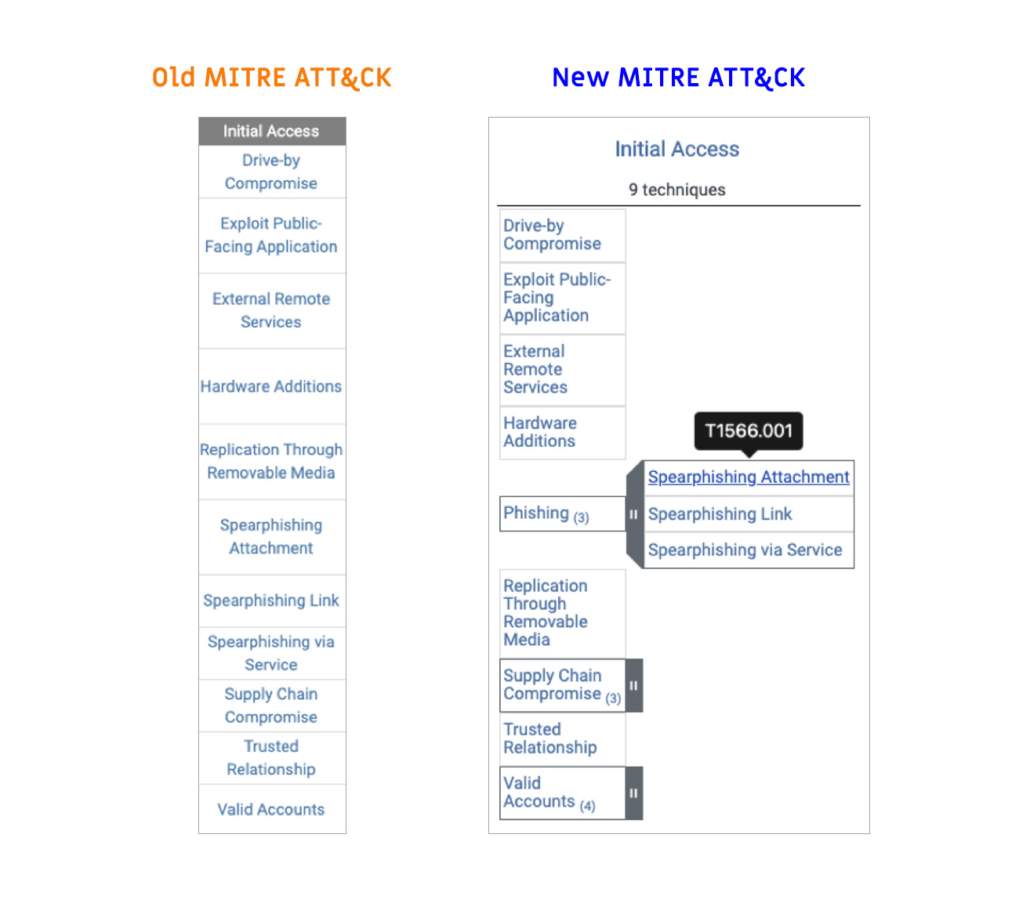
MITRE recently announced the addition of sub-techniques to their framework. In their own words, “Simply put, sub-techniques are more specific techniques. Techniques represent the broad action an adversary takes to achieve a tactical goal, whereas a sub-technique is a more specific adversary action.”[1] Let’s take a look at an example of how some of these changes demonstrate themselves in the new version. Below you will see ‘Initial Access’ a Tactic found on the ATT&CK Framework. In the previous version of the Framework, Spearphishing Attachment, Spearphishing Link, Spearphishing via Service were techniques, and in the new version, they are all sub-techniques and consolidated under Phishing, which now exists at the Technique level. You can also see that Supply Chain Compromise and Valid Accounts added new sub-techniques that were not there previously. New sub-techniques were required across the entire framework to properly scale and respond to threats as they evolve.
By combining existing similar sub-techniques into groups and developing new sub-techniques across the entire framework, MITRE has solved a problem with granularity and built a new framework that can continue to evolve and scale for years to come. “ATT&CK’s growth has resulted in techniques at different levels of granularity: some are very broad and cover a lot of activity, while others cover a narrow set of activity. We wanted to address the granularity challenge while also giving the community a more robust framework to build onto over time.”[1]
Applying ATT&CK Tags to threat intelligence enables you to classify, correlate, and derive meaningful conclusions to help you prioritize response and make better decisions.
Lastly, incorporating ATT&CK into ThreatConnect Playbooks lets you automate how the framework gets utilized in your workflow. For example, notify your Security Operations team and add indicators to blocklists when Incidents associated with Tactics and Techniques relevant to your organization occur.
If you’re a ThreatConnect customer, please reach out to your dedicated Customer Success Team for more information on migrating to the new version of MITRE ATT&CK. If you’re not yet a customer and are interested in ThreatConnect and this integration, contact us at sales@threatconnect.com.
[1] https://medium.com/mitre-attack/attack-with-sub-techniques-is-now-just-attack-8fc20997d8de
