
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.

Getting Started with Threat Intelligence: A Guide for Retailers
How any size retailer can get started with ThreatConnect to gain context about threats Are you a retailer? Just getting started with threat intelligence? Then you are going to want to read this — our first post in a series directed toward specific business verticals. Retail is a vast ecosystem that connects merchants to suppliers, […]
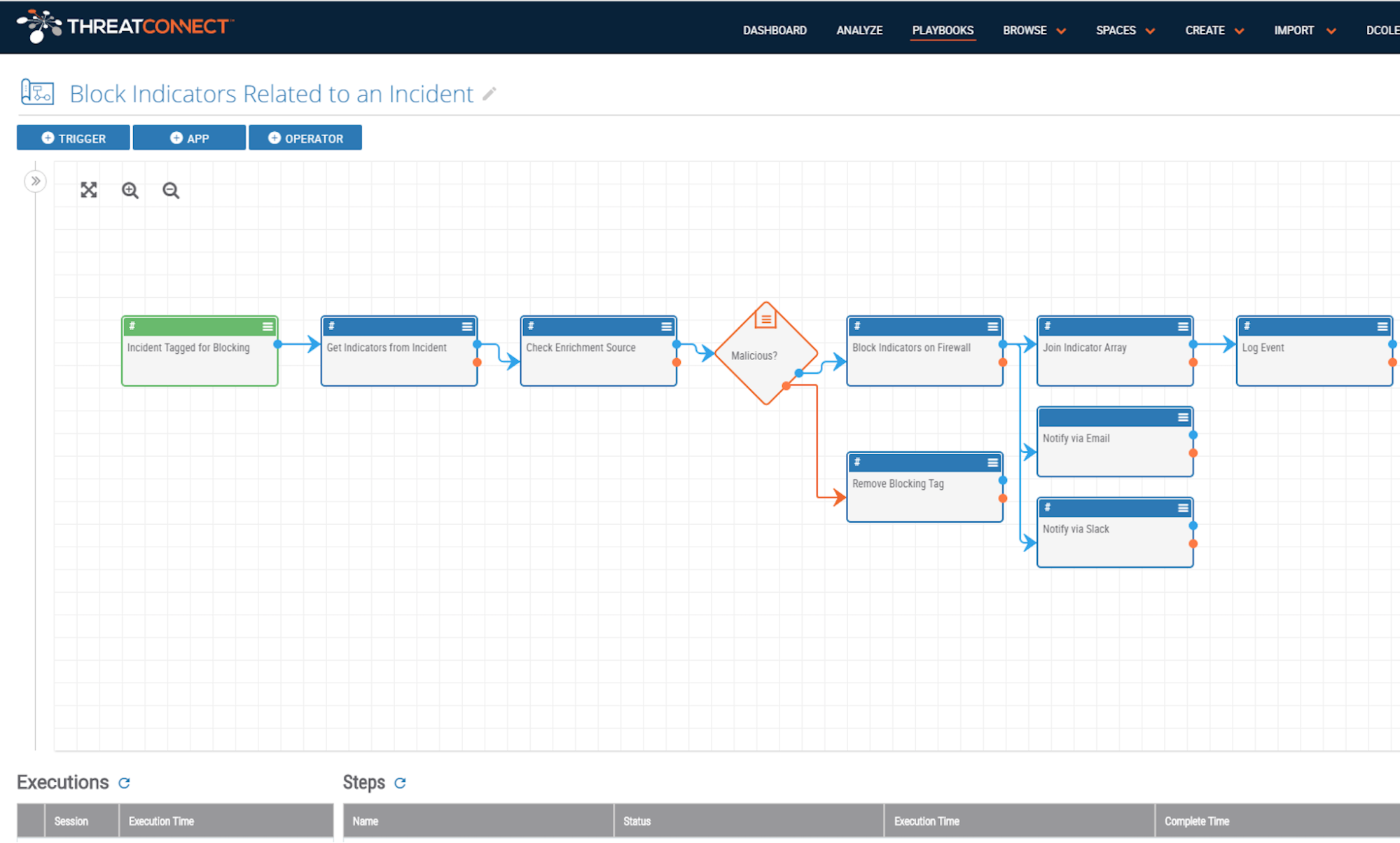
Save Time and Accomplish More with Playbooks
ThreatConnect Playbook Actions: Be More Efficient and Gain Control with Automated Actions ThreatConnect’s Playbooks feature automates almost any cybersecurity task using an easy drag-and-drop interface – no coding needed. ThreatConnect uses Triggers (e.g., a new IP address Indicator, a phishing email sent to an inbox) to pass data to apps, which perform a variety of […]

Share The Love: Using ThreatConnect as a Threat Intelligence Sharing Platform for ISACs, ISAOs, and their Members
How ISACs, ISAOs, and their members use ThreatConnect’s threat intelligence sharing platform effectively to share threat Information For those who read “share the love” and hoped this was a post about reggae music, and its rhythmic message of peace, love, and unity, my apologies. This post is actually about the smooth sound and power of […]
The FORCE of STIX & TAXII: Why STIX & TAXII are so Important to Financial Services Companies & EMEA
The Force of STIX & TAXII Use the force, Luke. If your cybersecurity team were given a common threat intelligence language and transport method that surrounded, penetrated, and bound you in an impressive-galactic-sort-of-way to other fighters of cybercrime, would you take it? The free, open-source tools, STIX and TAXII are doing just that. With the […]
Measuring the Detection and Response Gap
Measuring the Detection and Response Gap Despite efforts to stockpile the best technology and assemble an army of defenders, today’s security organizations struggle with inefficiencies. Threat actors are getting more efficient at compromising networks, taking only minutes or less to compromise systems. Organizations, meanwhile, are taking weeks (or longer) to discover breaches – and oftentimes […]
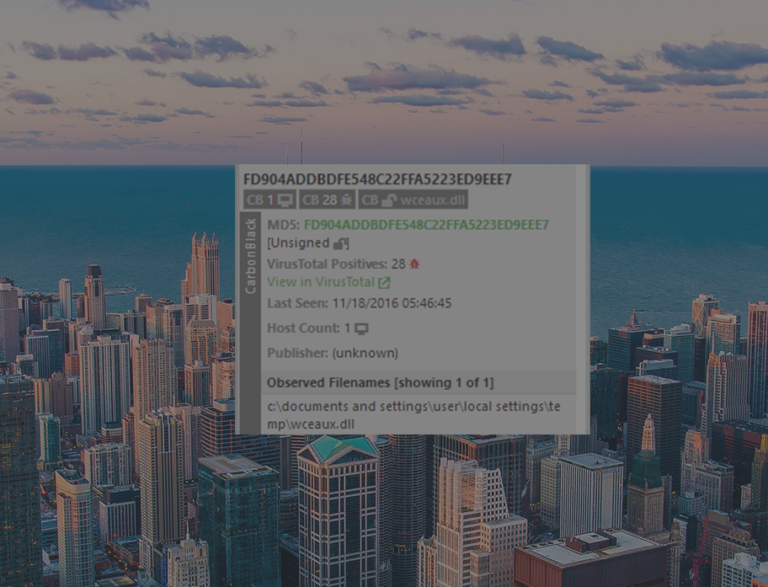
Know Every Binary That Has Ever Run in Your Environment
Binary file hashes are a common indicator used in information security. Unfortunately, files hashes are hard to read, let alone memorize. Here are some examples of what file hashes look like: 18f8e43b6de2dcf7c8e96af329ded882 0cc61d25f0e009e730e3a95d778325ed16ef26da 88237ec59eefc109f564e055216d8b7c6a4afd88ced7e3ef81a5801b083cecd2 I challenge you to memorize one of these, let alone the thousands that run in your environment every day. An information […]
Research One: A ThreatConnect Story
Research One: A ThreatConnect Story We’re excited to announce the availability of our newest product: TC Identify™, a threat-driven, context-enriched intelligence source provided through, and enabled by the ThreatConnect Platform. As we are wont to do with many of our notable announcements, we decided to draw a corollary to the Star Wars universe. Wait a […]
Towards Data-Driven Threat Analysis
Make Better Decisions Based on Your Indicators of Compromise A random person on the Internet once said, “Threat Intelligence is a lot more than Intel feeds.” This person was absolutely right. In fact, the very premise of a cybersecurity platform is that indicators of compromise (IoCs) alone are just one piece of your security puzzle, […]
Stepping to Fancy Bear
Stepping to FANCY BEAR (or how to efficiently validate and enrich a jumbled list of indicators) Over the last few weeks the U.S. government released two reports on Russian hacking and influence operations related to the U.S. election. Most notably, the unclassified version of the Intelligence Community Assessment (ICA) “Assessing Russian Activities and Intentions in […]
Do You Make Swords, or Do You Wield Them?
Classifying Analysts: Intelligence Producers and Intelligence Consumers The disciplines of swordsmith and swordsman have been intrinsically linked since the dawn of war. The swordsmith who crafted the sword is using a different skillset than the swordsman who wields the sword. In this same way, intelligence analysts come in two broad categories: intelligence producers and intelligence […]
How Companies Use ThreatConnect To Create a System of Record: A Use Case
This is the third in a series of blog posts about how organizations are utilizing the ThreatConnect platform. We’re going to share stories of how customers just like you have transformed their security programs using ThreatConnect, in particular, creating a cybersecurity system of record. In order to keep our customers secure, will be using pseudonyms […]
Hacktivists vs Faketivists: Fancy Bears in Disguise
What is a faketivist? One of the more surprising stories of 2016 was the Russian effort to shape the outcome of the U.S. presidential election. What surprised us most at ThreatConnect was not Russian APTs breaching the Democratic National Committee, but the efforts to “weaponize” that information through a campaign of strategic leaks. This stands […]
