
Read insights, thought leadership, and platform updates.
No Blogs Match Your Results
Please try again or contact marketing@threatconnect.com for more information on our blogs.
ThreatConnect Introduces Version 5.6
More Results, More Analysis, More ROI Earlier this quarter we announced the release of ThreatConnect version 5.6. It’s centered around making our platform even more effective for user collaboration and analysis. Having what you need exactly when you need it is critical across security operations, but especially when dealing with threat intelligence. So much so, […]

ThreatConnect achieves ISO 27001:2013 certification
Continuing our commitment to protect our customers’ data What is ISO 27001? ISO 27001 is an internationally recognized standard defining requirements for a systematic approach to managing sensitive information, also known as an information security management system (ISMS). But what’s an ISMS? Think of an ISMS as the blueprint for how we identify, assess, and […]
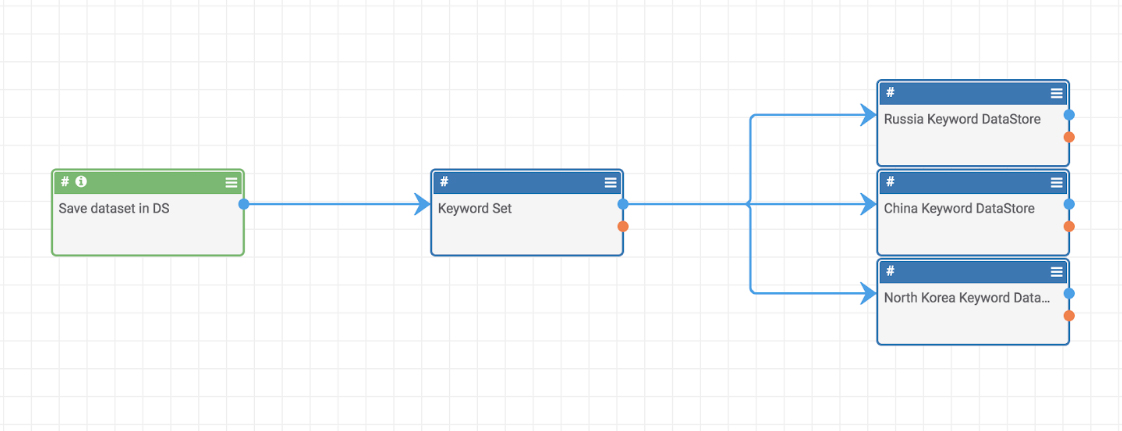
Playbook Fridays: Document Parsing and Keyword Scanning/Tagging
Automatically tag the documents with keywords and focused areas of interest without human intervention ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human […]
How to Choose the Right Threat Intelligence Platform for You
Understand it’s “job” and what you and your team need The first step to choosing the right threat intelligence platform (TIP) for you is to figure out what you actually want the TIP to do. One pitfall that security teams often fall into is that they approach the selection with a checklist of criteria, without […]
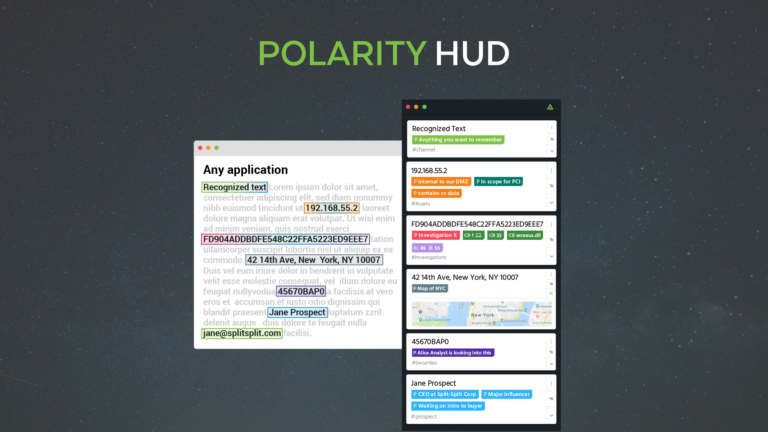
We’ve built an actual HUD, not a dashboard.
The time has come for the official release of the HUD. As of today, the feature users have been asking for is officially out of beta. In this post, we share the reasons users wanted the HUD to be real-time, what problems it solves, and how it works. Why Since data awareness and improving decisions […]
Kinetic and Potential Energy Framework: Applying Thermodynamics to Threat Intelligence
ThreatConnect proposes a framework for evaluating and triaging indicators based on physical energy properties All variety of scientists, from chemists to physicists and engineers, measure kinetic and potential energies to better understand how objects are acting or will act within a given situation or system. We posit that these energy concepts can be applied to […]

Polarity – Confluence Integration
Interoperability by Design is the foundation for our dynamic Integration Framework, allowing you to integrate with almost any database or API. The more you integrate the internal or 3rd party, commercial or open source, data you already use to Polarity, the more powerful Polarity becomes. Integrations make you, your teams, and your tools, exponentially more […]

Save Time By Recognizing Machine Time
Occasionally our users come across UNIX Epoch time, the representation of time as the number of seconds elapsed since January 1st, 1970. The representation was not meant to be human-readable and often users must convert the time to something more human consumable. For example, the UNIX Epoch timestamp 1445400000 will be converted into a representation […]
Playbook Fridays: How to Use ThreatConnect Playbooks to Manage Security APIs
Planning for APIs as part of your security architecture This is my first Playbook Friday blog post. I love the ones that the team creates and thought I would try my hand at one. That said, because I am not in the Platform as much as I’d like to be, I enlisted the help of […]
ThreatConnect and the Rise of the Security Developer
Taking Your Team & Career to the Next Level with ThreatConnect’s GitHub Repositories Going to the Next Level with ThreatConnect’s GitHub Repositories When I walk the show floors at RSA or Black Hat, I’m always struck by the number of new products that pop up every year. The “hot topic” varies – this year it […]
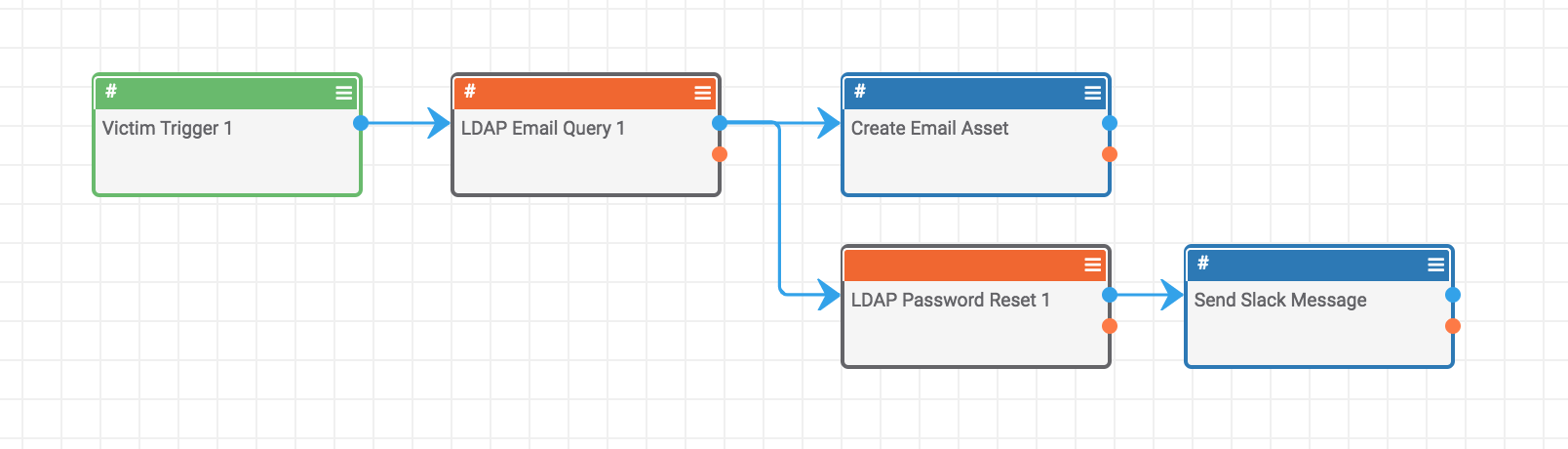
Playbook Fridays: Forcing Active Directory (AD) Password Resets via ThreatConnect Victims
Leveraging the Active Directory and ThreatConnect integration to help automate security processes ThreatConnect developed the Playbooks capability to help analysts automate time consuming and repetitive tasks so they can focus on what is most important. And in many cases, to ensure the analysis process can occur consistently and in real time, without human intervention. This […]
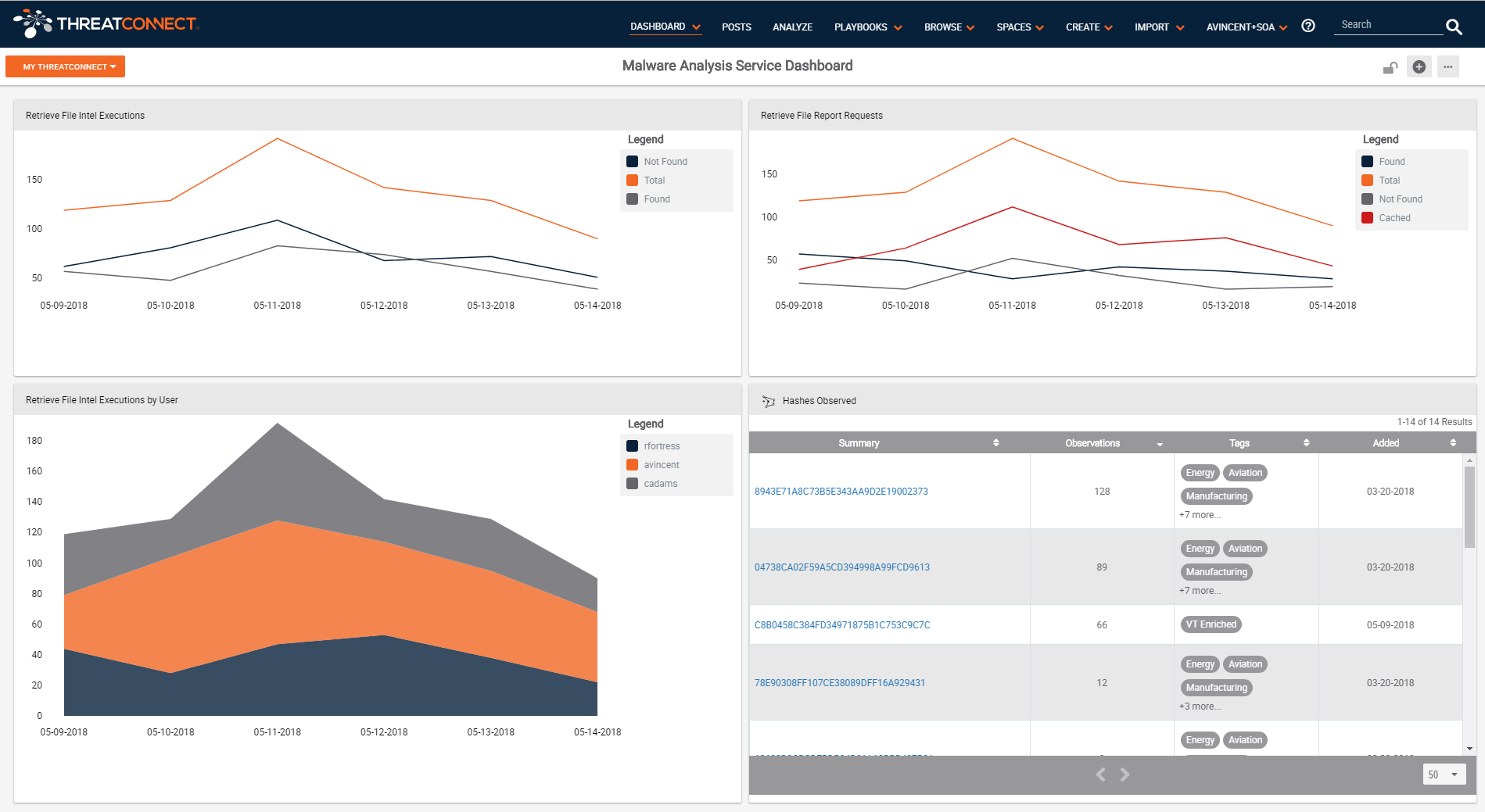
Introducing ThreatConnect’s Intel Report Cards
Providing insight into how certain feeds are performing within ThreatConnect As part of our latest release, we’ve introduced a new feature to help users better understand the intelligence they’re pumping into their systems. Intelligence can be a fickle thing; indicators are by their very nature ephemeral and part of our job is to better curate […]
