Posted
The escalation of geopolitical tensions specifically focused on the Iranian Conflict over the last days of February 2026 has intensified the significant cyber and physical security risks to organizations globally.
With threat activity emanating from advanced Iranian state-sponsored actors, aligned hacktivist collectives, and opportunistic criminal groups, security teams must remain agile, informed, and proactive.
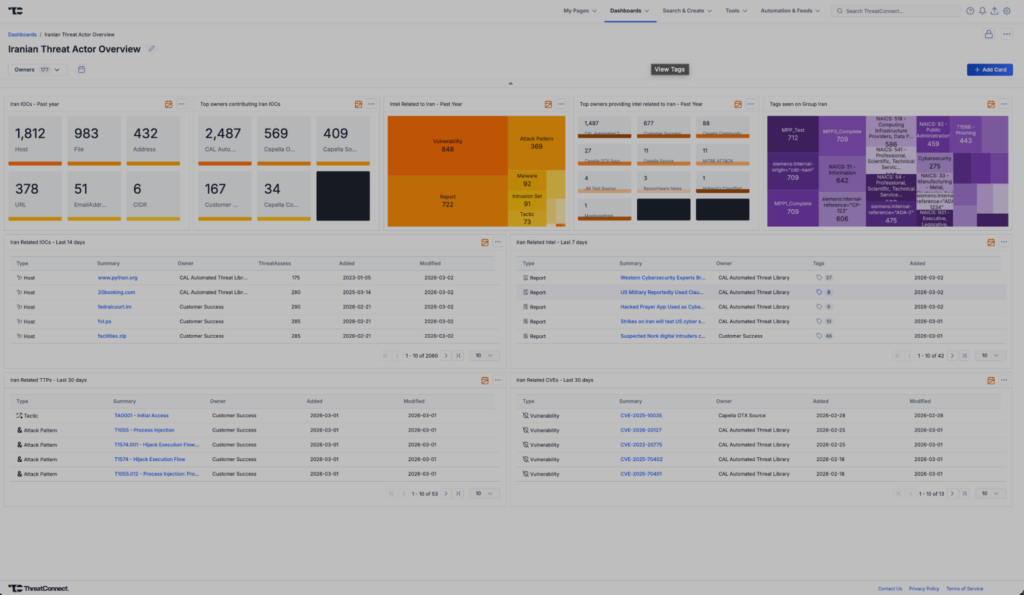
The Iranian Conflict Intelligence Dashboard has been updated to equip defenders with timely, high-fidelity intelligence that specifically reflects the dynamic threat environment shaped by this high-profile regional conflict with a heightened focus on Iran-linked activity.
Key Threat Actor Groups & Campaign Themes Tracked Include:
- IRGC-affiliated Cyber Units (e.g., APT33, APT34, APT39, APT42): Tracking activity from primary state-sponsored groups.
- Proxies and Ideological Hacktivist Actors: Monitoring activity from groups like CyberAv3ngers, APT IRAN, Handala Hack, Lulzsec, Dark Storm Team, GhostSec, Cyber Islamic Resistance, and others aligned with Iranian strategic interests.
- Coordinated Influence and Disinformation Campaigns.
- OT and Critical Infrastructure Targeting Efforts, particularly those targeting Israeli and Western assets.
Rather than tracking isolated threats, the –Iranian Conflict Intelligence Dashboard dashboard provides strategic context and operational detail across the broader cyber conflict spectrum, enabling faster detection, response, and mitigation.
Key Benefits:
- Conflict-Centric Intelligence Aggregation – Centralized indicators of compromise (IOCs), TTPs, and threat insights related to Iranian-linked campaigns, sourced from open source intelligence (OSINT), premium threat feeds, and internal telemetry.
- Live Threat Environment Tracking – Monitors shifts in activity across major adversary groups, cyber incidents, defacements, DDoS campaigns, and geopolitical events fueling escalation.
- Accelerated Incident Response – Enriched and correlated intelligence to support triage, prioritization, and response activities during periods of elevated tension or retaliatory operations.
- Custom Visualization & Analysis – Interactive dashboards featuring timeline analysis, actor overlap matrices, infrastructure clustering, and geographic threat origination maps.
- ThreatConnect Automation Integration – Seamless correlation with existing ThreatConnect adversary profiles, intrusion sets, and signature-based alerts to identify high-risk overlaps with organizational environments.
Leveraging this dashboard allows security teams to anticipate conflict-related threats, understand attacker motivations, and tailor defenses to emerging risks as the Iranian cyber conflict evolves.
Specific Intelligence Focus: Iranian Malware List
- APT42: tamecat, tabbycat, vbrevshell, powerpost, brokeyolk, chairsmack, asyncrat
- APT34: powbat, powruner, bondupdater
- APT33: shapeshift, dropshot, turnedup, nanocore, netwire, alfa shell
- Other Related Malware: Gh0st Rat, quasarrat, amadey, bittersweet, cointoss, lateop
Specific Intelligence Focus: Iranian ICS Targets
ICS Systems Likely to be targeted by Iranian threat actors (based on analysis like the Censys report):
- “Unitronics” or (“Vision” AND (PLC OR HMI))
- “Tridium” or “Niagara”
- “Orpak” or “SiteOmat”
- “red lion”
Dashboard Components Include:
- Indicators linked to state-sponsored and proxy cyber operations.
- Threat groups aligned to Iranian strategic cyber interests.
- Reports and advisories referencing the conflict, regional escalations, or actor-attributed activity.
- Campaign tracking with attribution timelines, victimology insights, and strategic objectives.
- MITRE ATT&CK techniques used by affiliated groups, mapped to known incidents.
- Keyword and tag intelligence trends across conflict-related reporting.
- Infrastructure associations (e.g., shared IPs, domains, malware hashes).
- Actor and alias mapping, including cross-reference to public and private sector intelligence.
- Vulnerabilities linked to recent Iran intelligence activity.
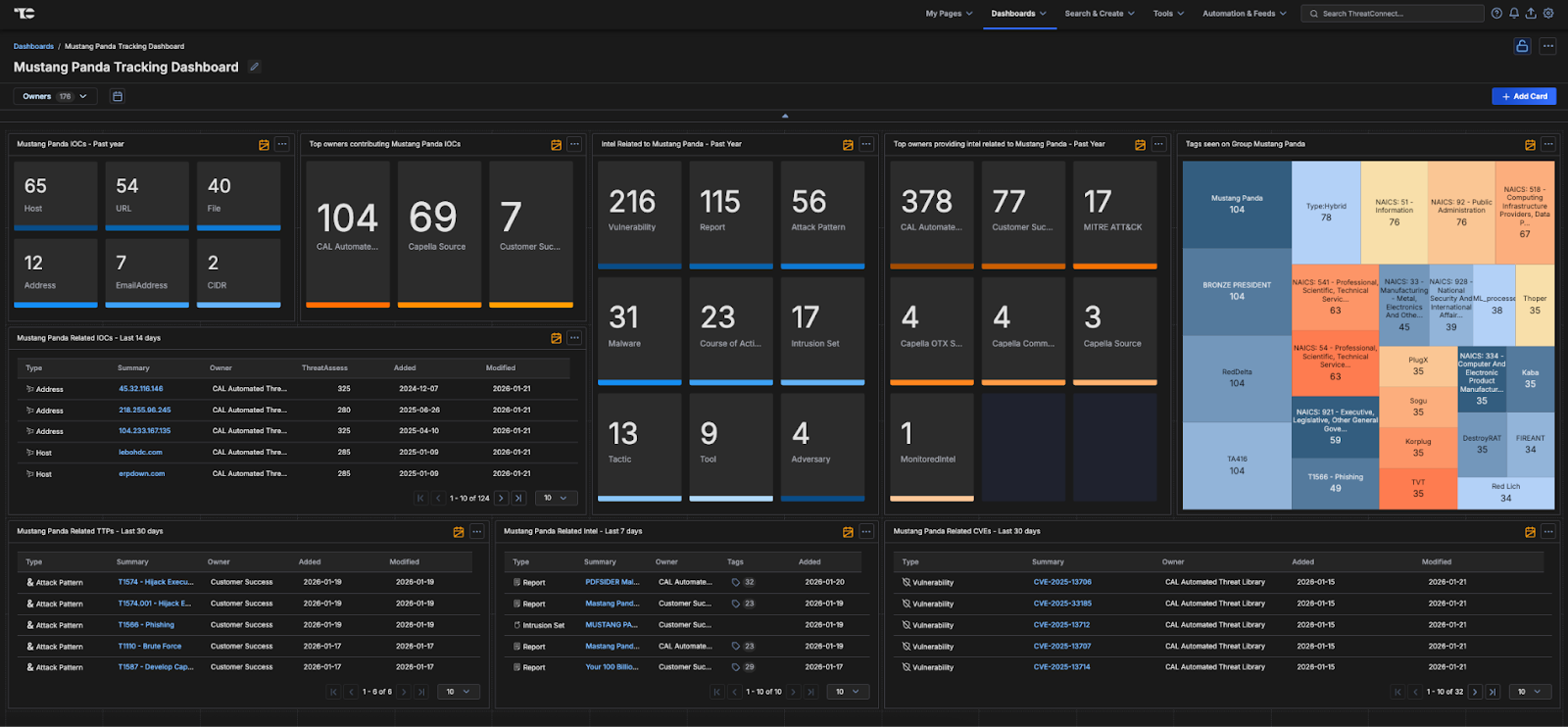
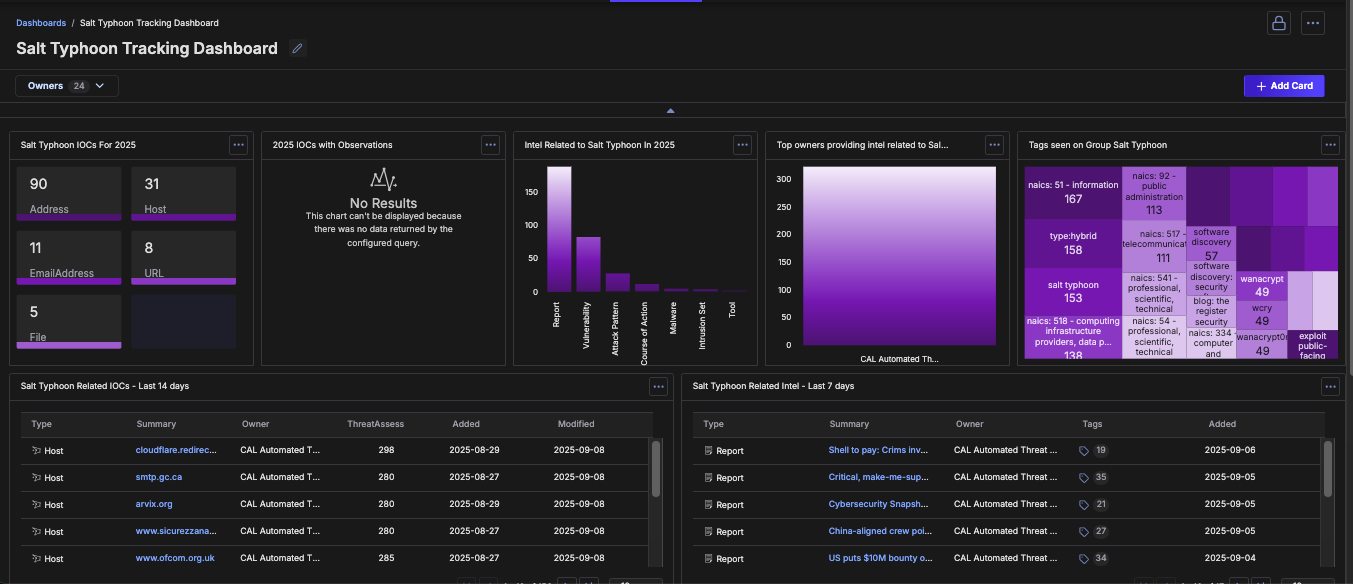
Screen Capture of Iranian Conflict Intelligence Dashboard
Lead Contributor – Adrian Dela Cruz , Customer Success Engineer
To gain access to the Iranian Conflict Intelligence Dashboard, please reach out to your Customer Success team or reach out to us through our contact form.
The dashboard is also available here, and can be added manually to your ThreatConnect instance.