Reversing Labs
ReversingLabs solutions drastically accelerate and broaden organizations’s ability to detect new threats, respond to incidents and gain intelligence on attacks. Large enterprises and security vendors use these solutions as a foundation for protecting digital assets. Our solutions implement unique, innovative technologies that detect and analyze threats within files. Spectra Core Automated Static Analysis evaluates internal threat indicators in files in milliseconds to support real-time and high volume applications. Spectra Intel File Reputation service identifies and provides up-to-date threat intelligence on 2 billion goodware and malware files.
Integrations
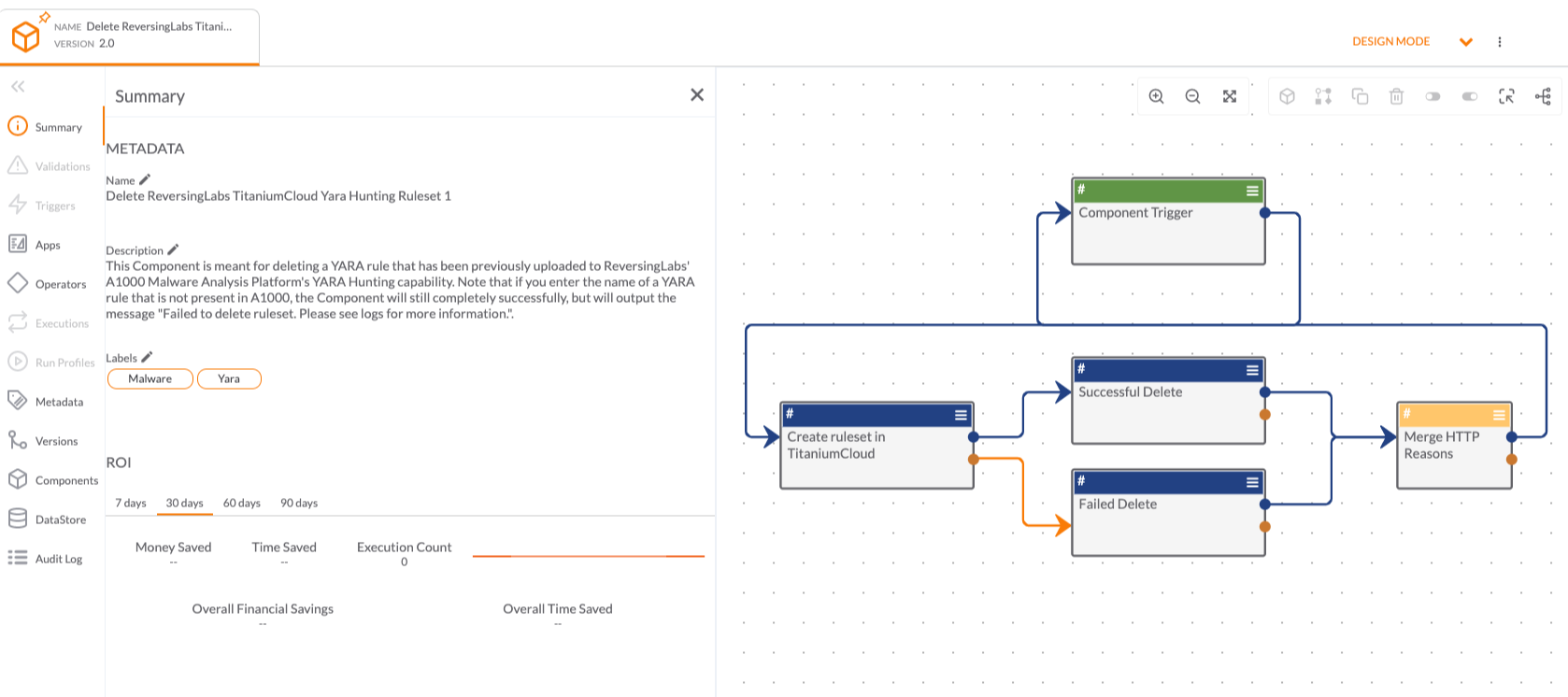
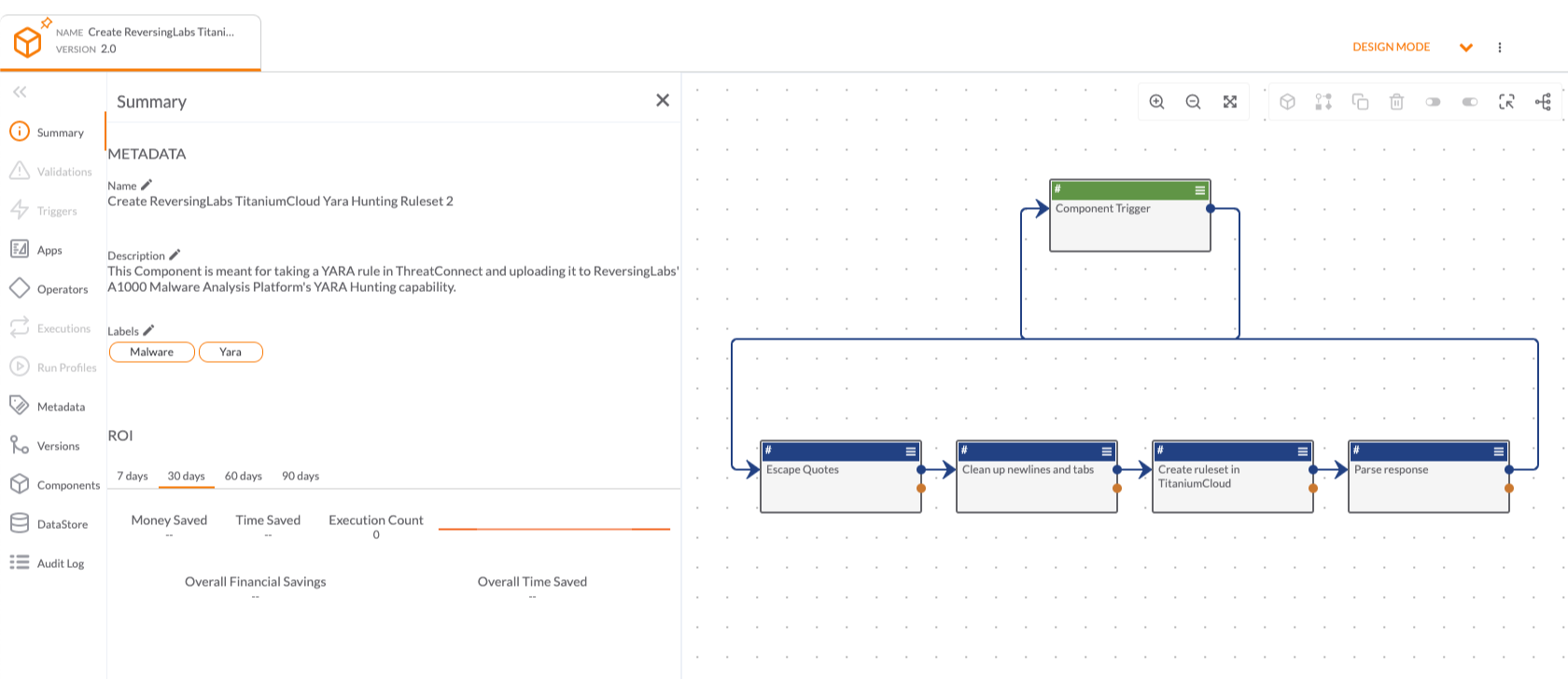
Built By ThreatConnect
Built By ThreatConnect
Built By ThreatConnect
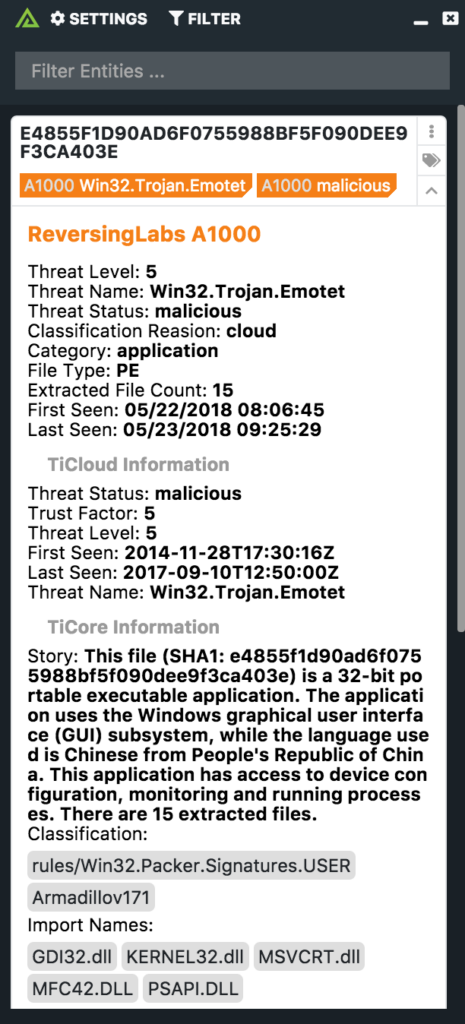
ReversingLabs Spectra Analyze with Polarity
Keep ReadingPlaybooks
Built By ThreatConnect



 Polarity
Polarity